Why Context-First Data Is the Future of Cloud Security
The Problem Nobody Wants to Admit
More data doesn’t automatically mean better security. It often means more homework.
Anyone who has sat in a security engineering seat knows the drill: map private to public IPs, line up container IDs with hosts, connect GUIDs to service accounts, and reconcile correlation IDs across distributed apps. Each source speaks a different dialect. You end up building a custom Rosetta Stone—parsers, lookup tables, and duct tape—hoping nothing breaks upstream.

Context-First Data Is The Future Of Cloud Security
The Problem Nobody Wants to Admit
More data doesn’t automatically mean better security. It often means more homework.
Anyone who has sat in a security engineering seat knows the drill: map private to public IPs, line up container IDs with hosts, connect GUIDs to service accounts, and reconcile correlation IDs across distributed apps. Each source speaks a different dialect. You end up building a custom Rosetta Stone—parsers, lookup tables, and duct tape—hoping nothing breaks upstream.
Collecting data is easy. Using it—in time to matter—is hard.
The Shift
From Tool-Centric to Data-Centric we’re conditioned to think in categories and dashboards. But the real question isn’t “Which tool fits this box?” it’s “Which data, with the right context, helps us decide and act now?”
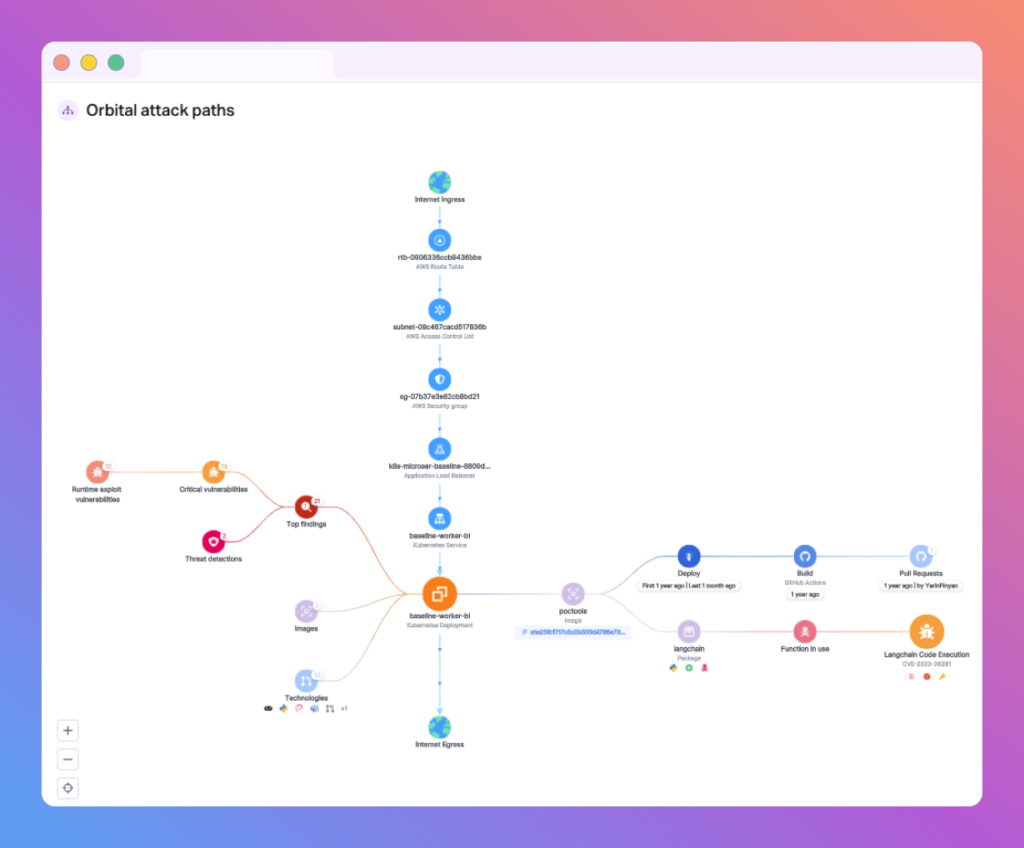
At Upwind, we call the answer a Security Fabric: a data layer that arrives pre-correlated across:
- Cloud control plane: who did what, when, and to which resources
- Data plane: what actually flows through your infrastructure
- Runtime telemetry: process, network, file activity
- The crosswalk: how a container IP maps to a Kubernetes service, to an API endpoint, to an IAM role
The magic isn’t aggregation. It’s correlation.
The Hidden Tax of “Bring Your Own Context” Alerts
Without context, they’re a tax on engineer hours—enrichment, correlation, and investigation that should have been built in from the start.
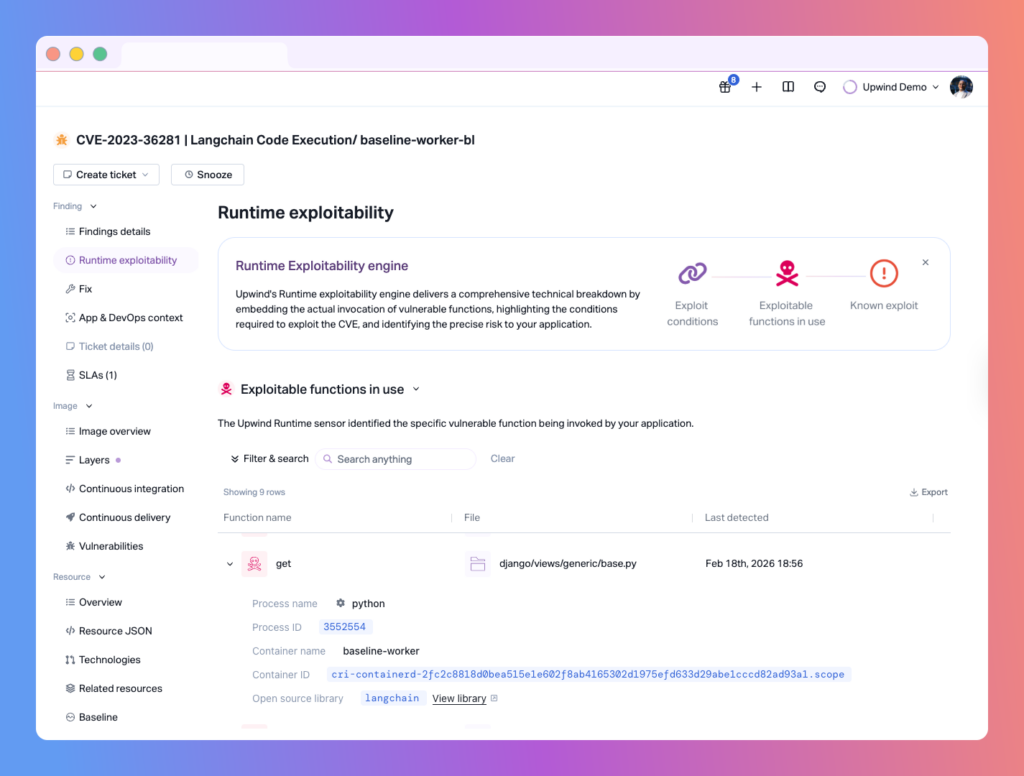
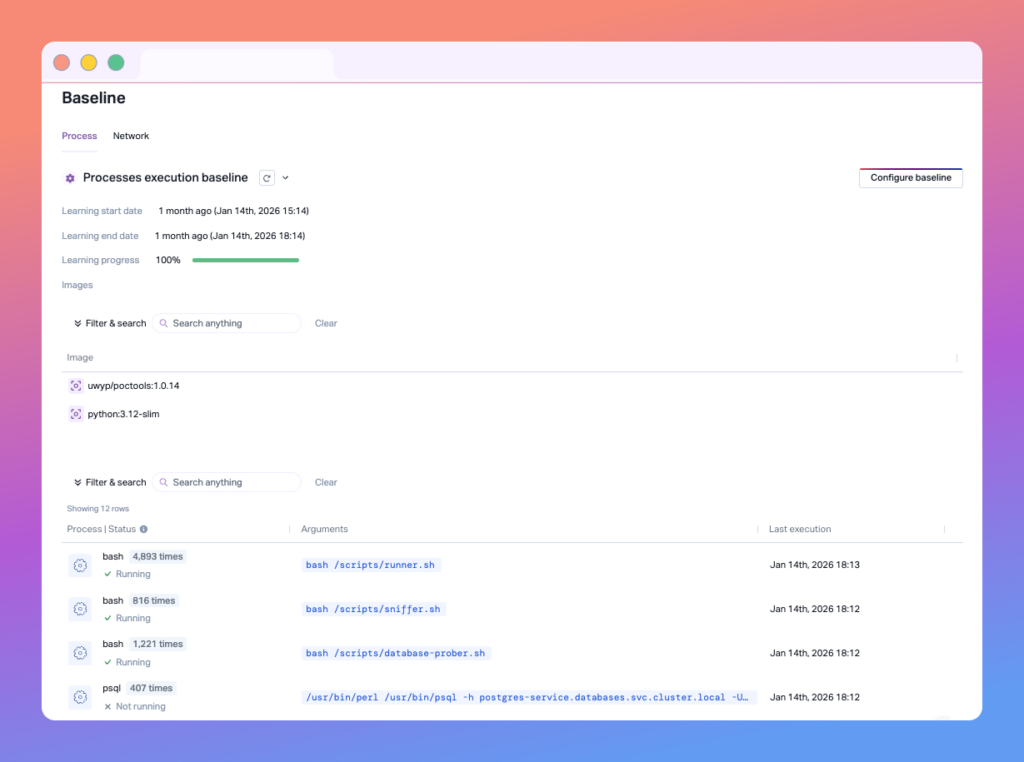
Vulnerability noise is a perfect example: mountains of “critical” items that never execute in production, drowning teams in work that doesn’t change risk. When findings are validated against real runtime behavior, you get fewer, clearer, more trustworthy signals—ready for action and automation inside your environment.
A Concrete Example: “Is This Lambda Supposed To Be Public?”
Here’s a scenario everyone has seen: a Lambda behind a public API endpoint. Sometimes that’s intentional (a payment webhook). Sometimes it’s a mistake (an internal function accidentally exposed). The difference really matters.
A minimal Terraform snippet that could be risky:
Copied
Why does this get messy fast? In real life, context is scattered.
- CloudTrail records API calls like CreateFunction, PutMethod, UpdateRolePolicy, CreateRestApi, DeployStage—each a breadcrumb.
- IAM tells you who touched what. Tags tell you “why” (if you’re lucky). API Gateway shows exposure details. Lambda config shows handlers and env vars. VPC settings influence reachability.
None of that meaning lives in one place. You stitch it together.
The Human Element
What you end up doing is the “human join.”
- You scan CloudTrail to see when the function and API were created, by whom, and if access changed recently.
- You check the IAM role to confirm permissions are scoped.
- You look for expected inbound sources (e.g., calls from Stripe IPs) and whether requests are signature-verified.
- You ask: Is this endpoint documented? Is it receiving the traffic we think it is? Is it running in a VPC? Does runtime behavior match the intended purpose?
Every one of those bullets maps to a log, event, or config you’d have to correlate by hand. That’s the tax.
Traveling with Context
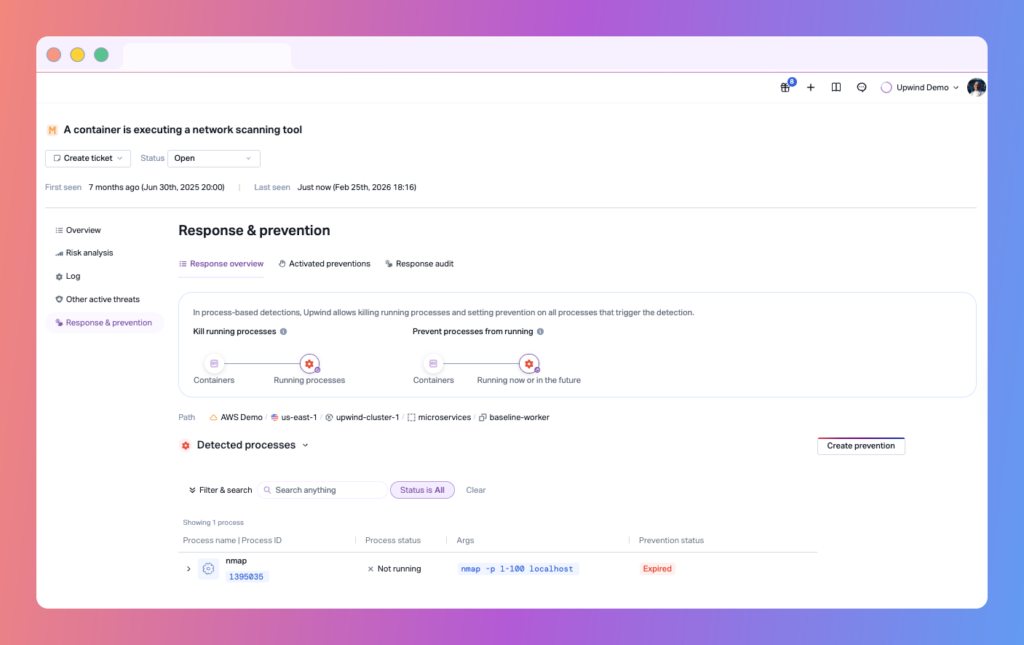
This is what a Security Fabric delivers: alerts that arrive complete, trustworthy, and immediately actionable:
Copied
Same surface symptom (a public Lambda). Completely different response—because context traveled with the alert.
What Your Security Fabric Should Provide
To understand the broader concept of a genuine Security Fabric—beyond the preceding example—let’s examine it step by step.
First, a pre-correlated identity mapping: Tie cloud resources, network identities, and humans—no manual lookups.
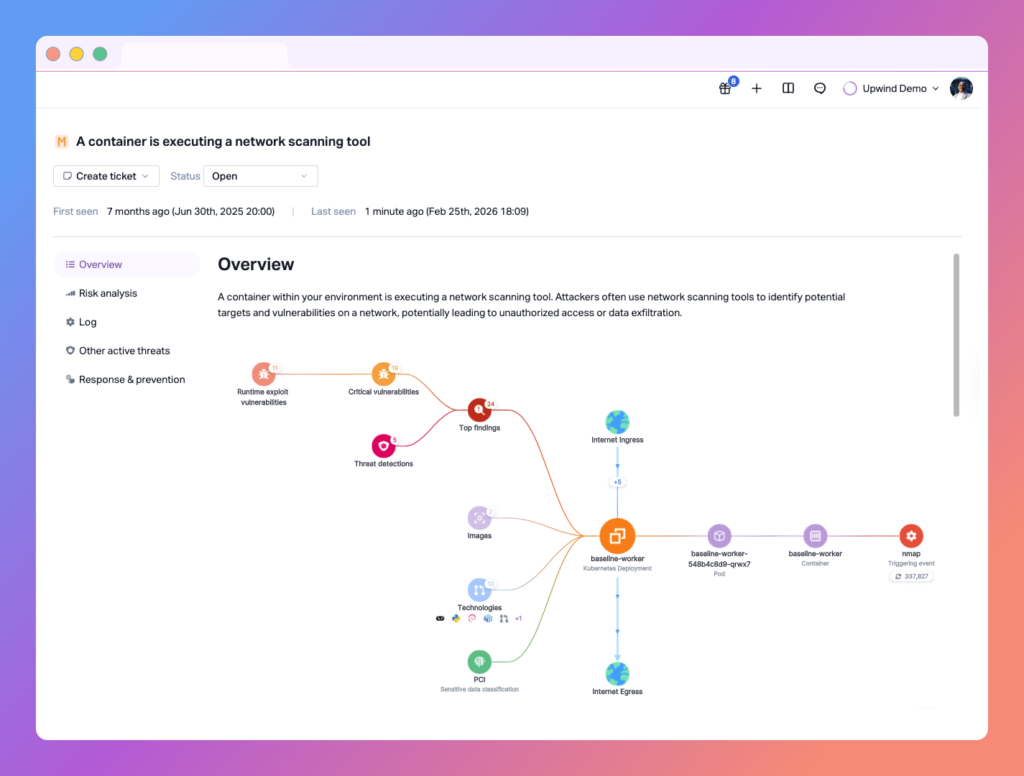
Runtime validation: Prioritize what actually executes and is reachable in production.
Topology awareness: Know if a finding touches a public entry point versus an internal batch job.
Temporal context: Detects new behavior, recent changes, and the actors behind them.
Actionability: High-confidence findings should plug directly into your workflows for automated handling where appropriate.
The Path Forward
We’ve proven that aggregating diverse sources adds value. We’ve also proven that correlation-as-homework doesn’t scale. The next wave isn’t “more feeds”—it’s data that arrives already contextualized and decision-ready. That’s what a Security Fabric is for: delivering signal, not noise.
When you evaluate your security approach, don’t start with categories. Start with questions:
- What decisions do we need to make quickly?
- What context must arrive with each signal to make those decisions?
- How much effort does it take to get that context today?
If the answer is “a lot,” you’re paying the wrong tax.
Final Thoughts
We’ve all heard that a picture is worth a thousand words. What we forget is that a picture is made of thousands of pixels. A single pixel means nothing. It’s just noise. Meaning appears when pixels connect – when colors align, edges form, and contrast creates depth.
That’s the promise of the Upwind Security Fabric.
Every AWS account, Azure subscription, GCP project, bucket, workload, identity, and network flow is a pixel. On its own, it’s an inventory. Connected, it becomes understanding. You don’t query five tools to trace traffic. You don’t pivot across dashboards to map identity, workload, and data flow. The picture is already rendered.
For years, security has focused on collecting more pixels – more logs, more telemetry, more coverage. But coverage isn’t clarity.
The next evolution in security isn’t adding data. It’s connecting it. When evaluating a security platform, ask one simple question: How fast can I see the full picture?
If it takes hours to assemble, you’re not seeing the story.
You’re just counting pixels.
See It In Action
If you’d like to see how this feature fits into your environment – or to explore how Upwind can help you prioritize and remediate risk more effectively – schedule a customized demo with us. We’ll walk through your use cases, integrations, and security goals to show how Upwind delivers actionable cloud security at scale.