
Thanks to GlassWorm, your developer’s laptop is now the most dangerous device in your company. You’re Welcome.
Key Takeaways We’ve spent the last decade hardening the perimeter. Using firewalls, Zero Trust and EDR on every endpoint. SOC analysts surviving on cold brew and adrenaline just to keep us safe. And then GlassWorm walked straight through the front door. Like taking candy from a baby. If you haven’t been following this one, here’s […]
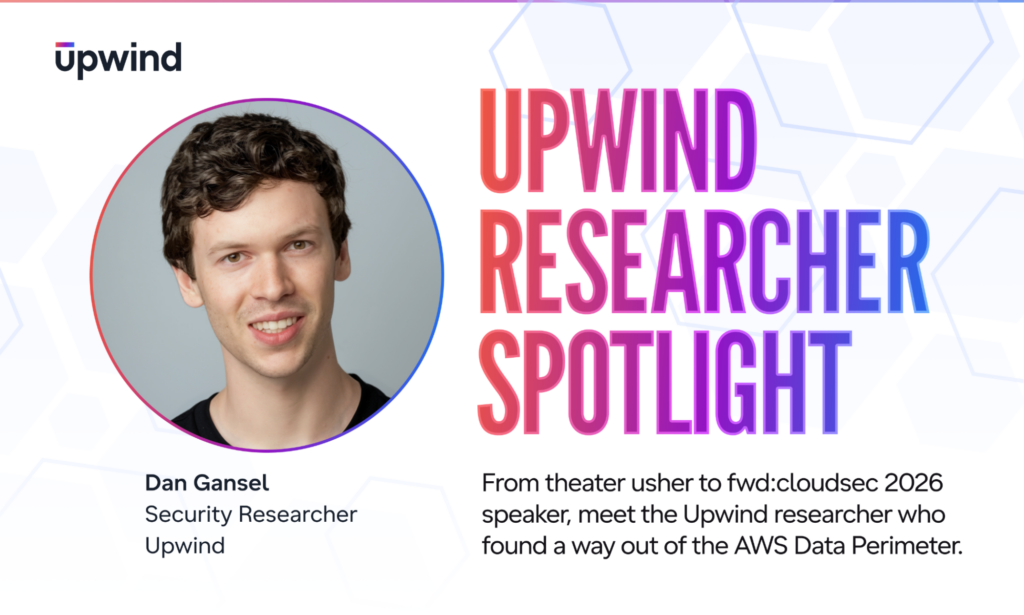
Upwind Researcher Spotlight: Dan Gansel
“You have to map the core logic and syntax of the system before you can find the interesting primitives.” This June 1st, Dan Gansel will walk on stage at fwd:cloudsec 2026 in North America to demonstrate a fully functional command-and-control channel that operates inside the AWS Data Perimeter, the cloud-native gold standard for keeping sensitive […]

Refuse the Seat: Why Modern CISO Leadership Advice Is Failing the Profession
Key Takeaways The single most repeated piece of advice in security leadership is also the one doing the most damage to the profession. Earn your seat at the table. Become a business translator. Integrate into the operator class. The CISOs who follow that advice end up burned out, legally exposed, and stuck in five-jobs-in-one roles […]
The AI Threat Landscape Demands a New Cloud Security Model
This week, the Shai-Hulud npm campaign showed how quickly a compromised package can move through the software supply chain, jumping across trusted dependencies and reaching build pipelines before many teams even knew what they were looking at. But this is not just an npm story, and it is not just a story about one campaign. […]

The next wave of AI is here. Upwind becomes Agentic.
One of the most fascinating technologies I’ve encountered in my personal life over the past few years is autonomous driving. It started as a curiosity, “can my car really drive itself?” Can it actually make decisions with enough necessary context, and not rely solely on static things it sees like trees and roads? Can it […]

The exploit window didn’t shrink. It flipped.
TL;DR: Time-to-Exploit (TTE), the gap between vulnerability disclosure and first observed exploitation, has gone negative. Mandiant’s M-Trends 2026 report shows attackers now exploit vulnerabilities, on average, before a patch is publicly available and we see the same in running environments. That breaks the foundational assumption every legacy CNAPP architecture was built on — that defenders […]

For the first time in 30 years, cybersecurity defenders might actually be winning
Everyone is catastrophizing about AI-powered attacks. Here’s the contrarian case, and why the window is narrower than it looks. TL;DR: The prevailing narrative at Black Hat 2025 was that AI has made attackers unstoppable. The most credentialed voice in the room said the opposite, and the data backs him up. The Mythos release through Project […]

The Real Shift Underneath Mythos
Key Takeaways Anthropic’s Mythos model has been called a cybersecurity watershed and a marketing stunt in the same week. Both camps have a point. Mythos appears to represent a real capability gain, and Anthropic deserves credit for releasing it through Project Glasswing rather than dropping it in the wild. At the same time, independent replication […]

We’ve Been Here Before and We Knew It Was Coming
The AI security industry is calling 2025 the new 1990s. The uncomfortable truth is that we predicted every mistake we’re making right now — and made them anyway. TL;DR: AI security in 2025 is repeating the same structural mistakes that made the early internet a golden age for hackers — not because the industry forgot […]
RSAC 2026 from the floor: What an AE heard between the keynotes and the handshakes
RSAC 2026 drew 43,500 attendees, 600+ exhibitors, and enough AI announcements to fill a small data lake. But the conversations that mattered most didn’t happen on the main stage. They happened in hallway pull-asides, over bad coffee, at HH and during blunt one-on-ones with security leaders who are done being marketed to and ready to […]






