AI has changed everything we know about Code and Shift-Left security
Trusted by hundreds of enterprises around the world
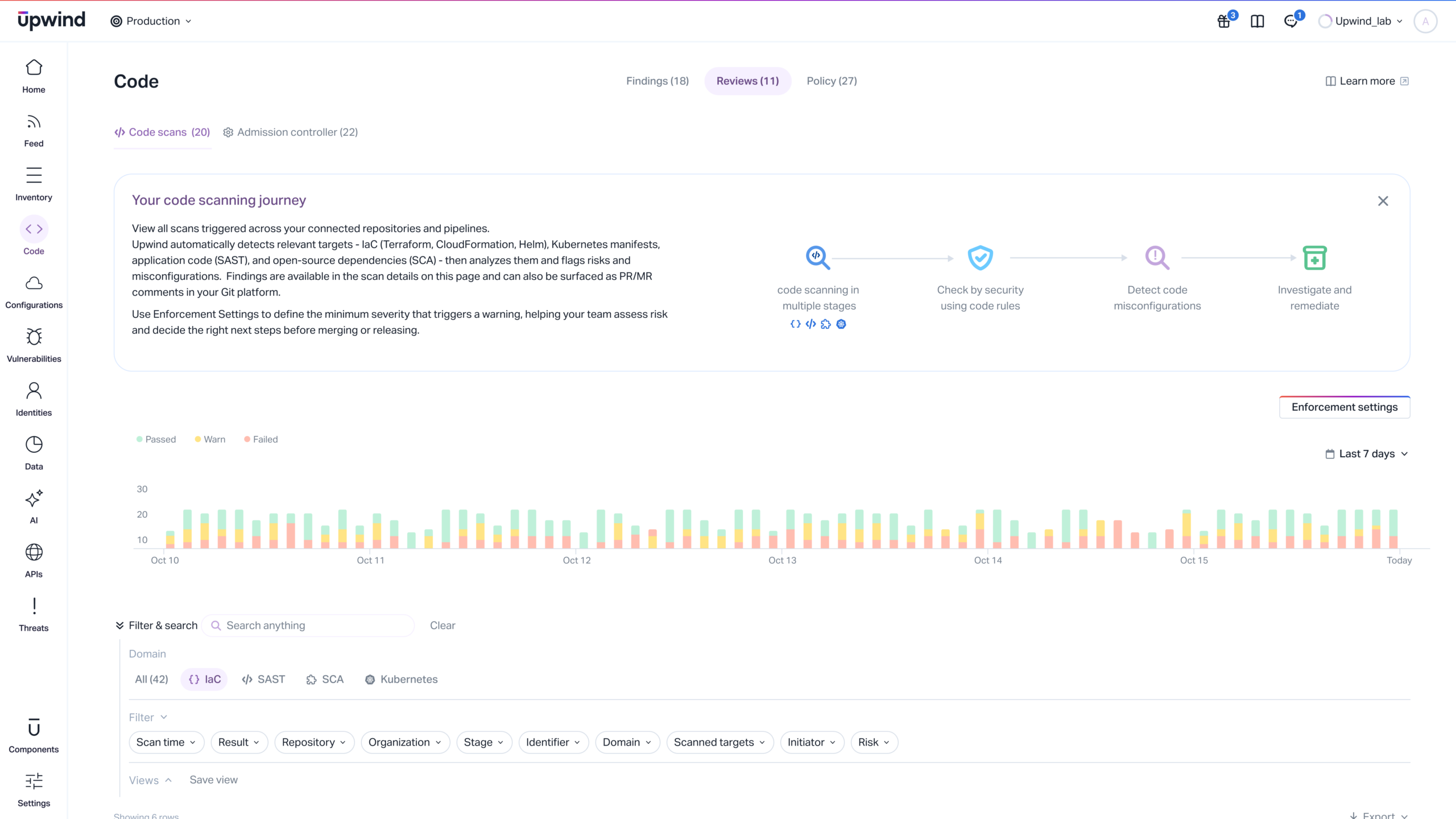
Code Security
- Scan traditional and AI-generated code instantly
Whether code is written by a human or an LLM, Upwind detects logic flaws, insecure patterns, and secrets in real-time, preventing vulnerabilities and risks from entering your codebase.
- Automated secret hygiene
Our advanced secret scanning detects and blocks API keys, tokens, and hardcoded passwords instantly, ensuring your accelerated development doesn’t lead to a data leak.
- Embedded in your flow
Upwind lives where you build. seamlessly integrated into Cursor, VS Code, and modern editors, giving you instant security feedback without context switching.
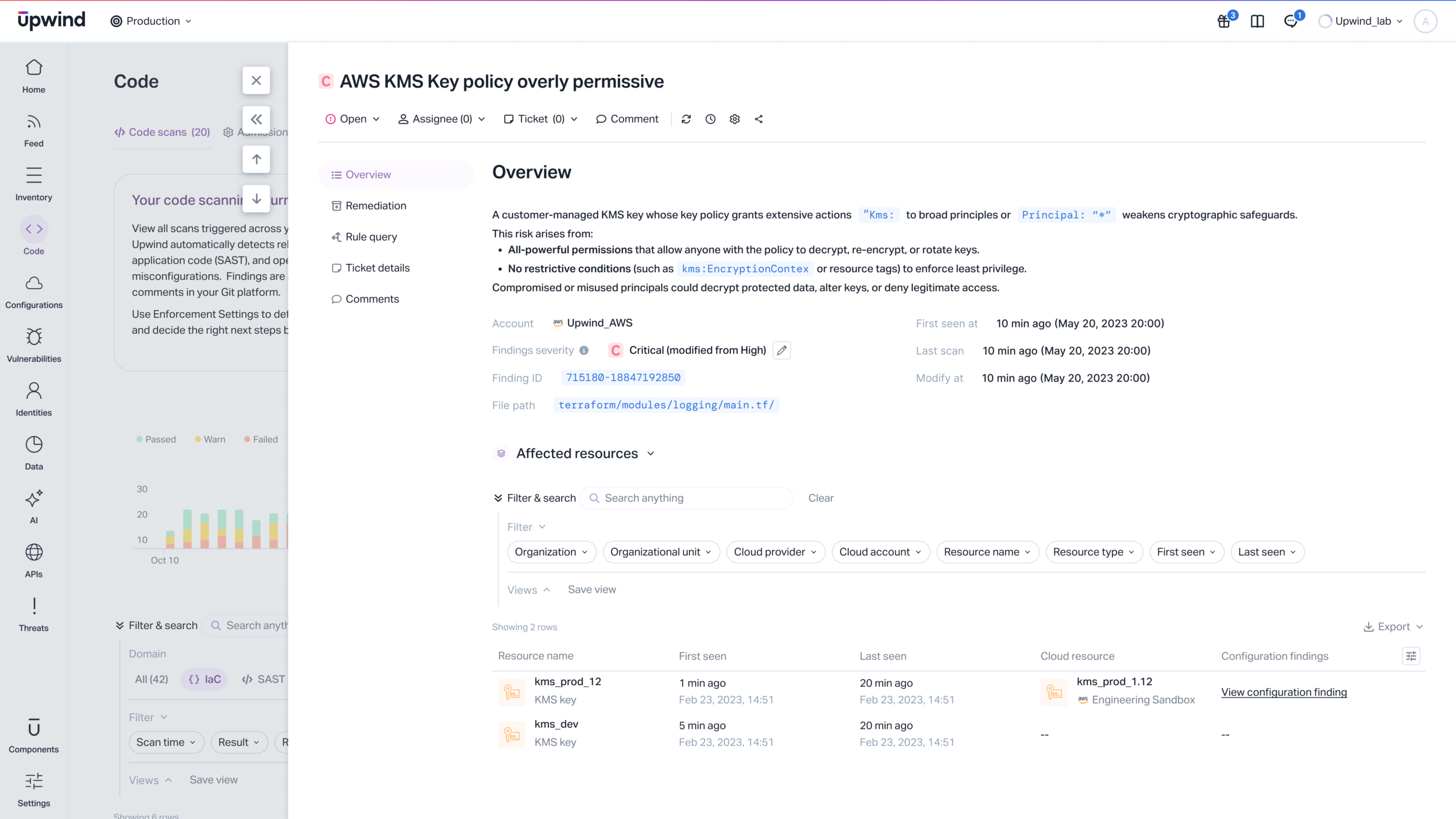
IaC & Deployment Scanning
- Deploy with Confidence
Analyze configuration files like Terraform and CloudFormation for accurate critical security flaws before they’re deployed, ensuring velocity never compromises security.
- Developer-First Detection
Get instant feedback on Terraform, Helm, and K8s manifests right in your CLI. We flag misconfigurations and compliance violations locally, so you can fix them before you even push.
- Frictionless CI/CD Guardrails
Security shouldn’t be a bottleneck. Our lightweight scanners integrate effortlessly into GitHub Actions, GitLab, Jenkins, and more. We enforce policies at the pipeline level with zero latency, blocking only the critical risks that violate your specific deployment standards.
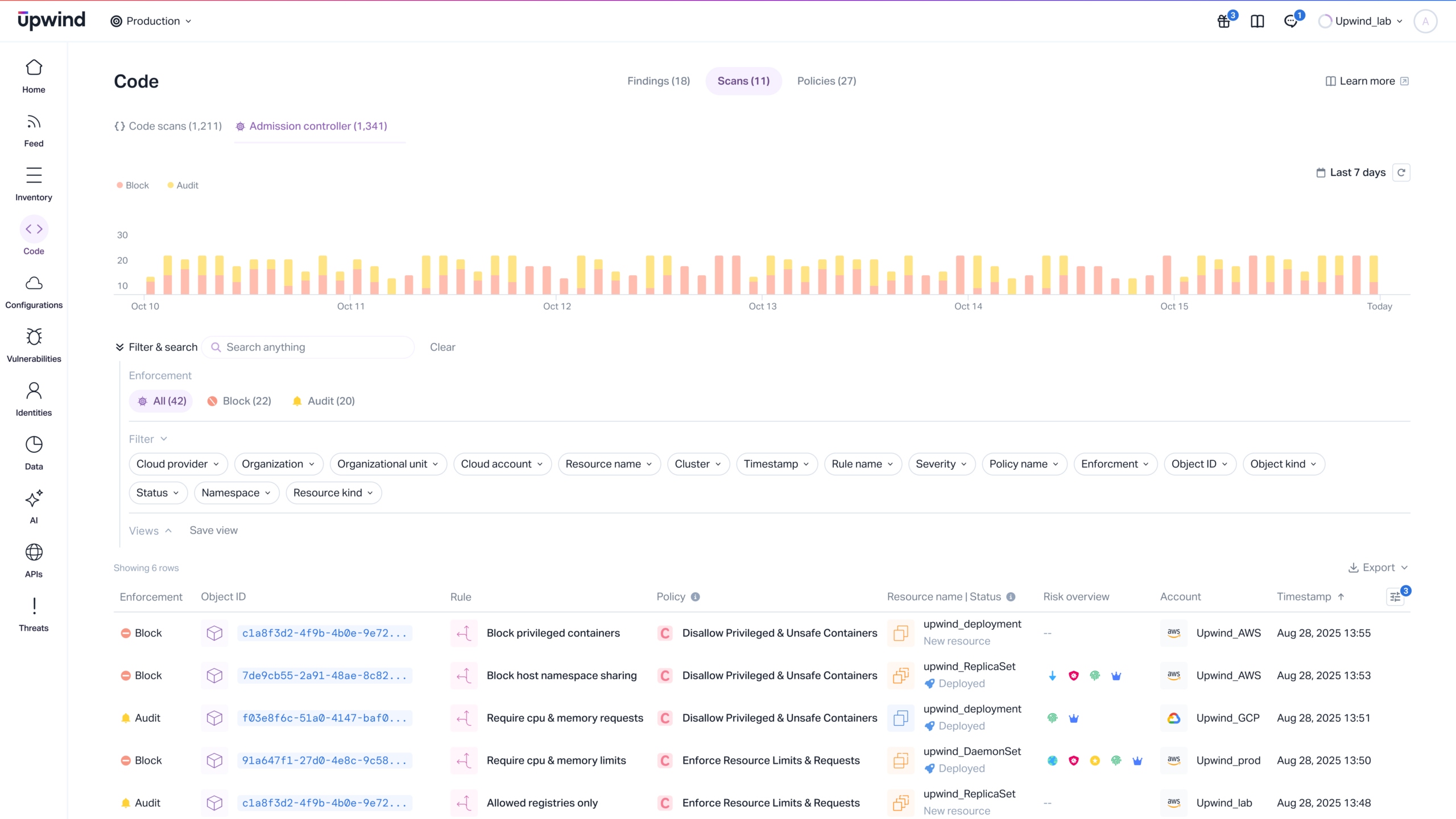
Admission Controller
- The Final Gatekeeper Before Production
Ensure absolute cluster and containers integrity. Our Admission Controller acts as the ultimate guard, enforcing granular policies to stop insecure workloads from ever starting.
- Native & Custom Policies Enforcement
Prevent privileged containers, root access, or unverified images from running. Use our out-of-the-box best practices or write custom policies to fit your specific organization’s compliance needs.
- Image Provenance & Integrity
Prevent supply chain attacks from entering your runtime environment. We validate image signatures and verify provenance at the door, ensuring that the container trying to run is exactly the same artifact your team built and verified, with no unauthorized modifications.
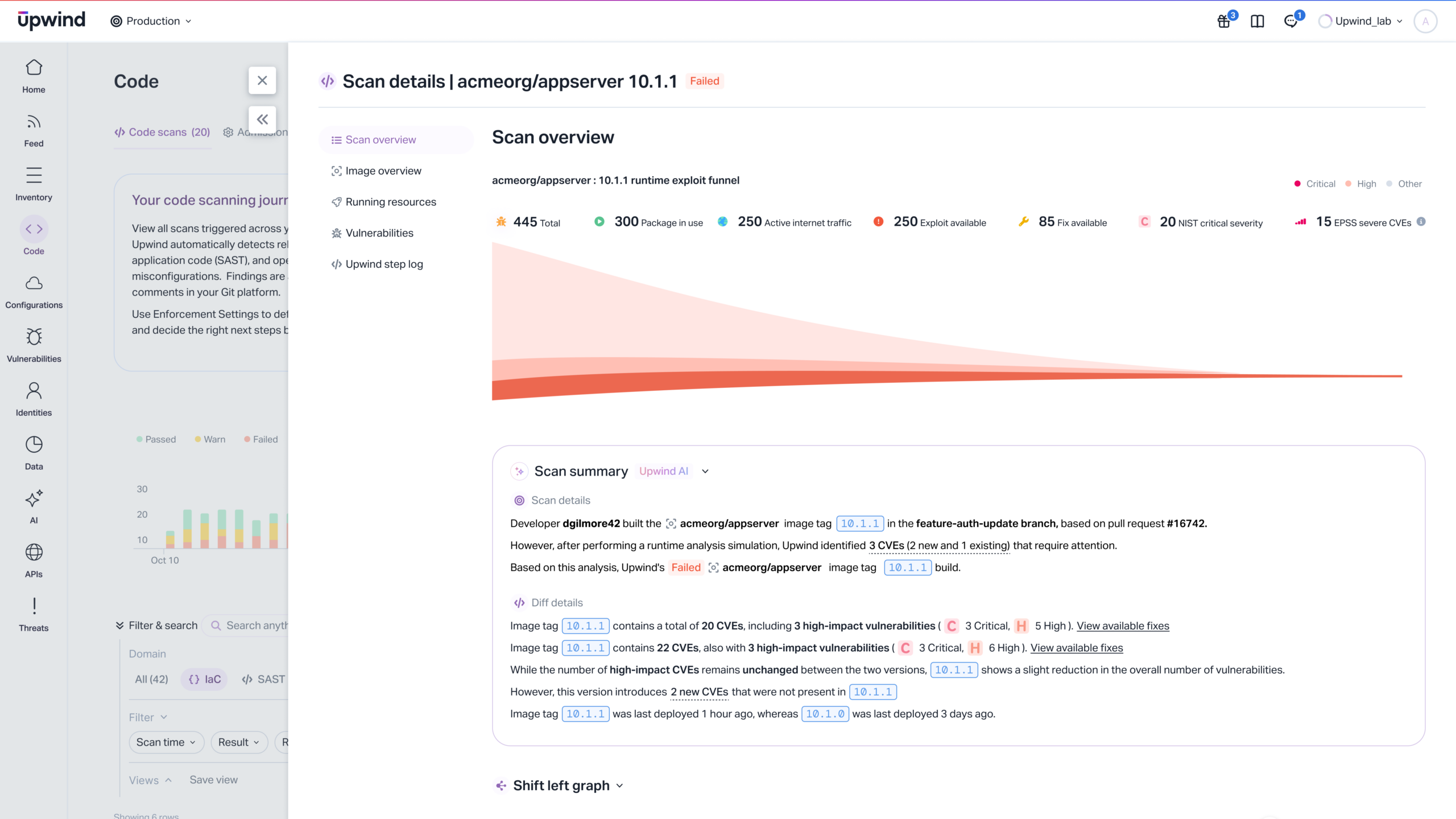
Runtime Prioritization
- Runtime-Validated Prioritization
We correlate your build-time alerts with live runtime data. See which vulnerable packages are actually loaded, running, and exploitable. We deprioritize the threats that are dormant, allowing you to focus entirely on the risks that are reachable.
- Silence the False Positives
Stop wasting cycles on theoretical vulnerabilities and risks. Upwind filters out the noise to give you a laser-focused list of the top 5% of risks that are actually exploitable in your specific environment.
- Direct Root Cause Resolution
Bridge the gap between Ops and Dev. When a runtime threat is detected, Upwind traces it back through the build pipeline to identify the specific repo, commit, and developer owner, enabling instant remediation at the source.
Secure Source Code with Runtime Intelligence
Secure modern cloud development with Upwind