Security for AI: Every Pillar of Cloud Security Just Got a New Job
A few weeks ago, I wrote about Upwind becoming agentic, AI for Security. We put a fleet of Agents, Blue, Red, and Green, to work investigating threats, validating exposures, and remediating risk at machine speed. That was one half of the story. This is the other half. Security for AI. AI has rewired our known […]

Upwind Brings Realtime Intelligence to Cisco Cloud Control
We are thrilled to announce that Upwind has been selected as a launch partner for Cloud Control Studio, part of Cisco Cloud Control, bringing realtime intelligence on cloud and AI security into the platform. Unveiled at Cisco Live Las Vegas on June 2, 2026, Cisco Cloud Control is the unified platform for agentic IT operations. […]

We Compiled the Top 10 MCP Use Cases for Upwind
A new vulnerability enters the backlog. A workload is exposed. A misconfiguration affects production. An identity behaves unexpectedly. A customer asks for evidence. An audit or pentest is coming up. Each moment requires the same understanding of what is real, what is urgent, what is connected, and what should happen next. The Upwind MCP Server […]
Scale AI Adoption Securely With Upwind AI Security
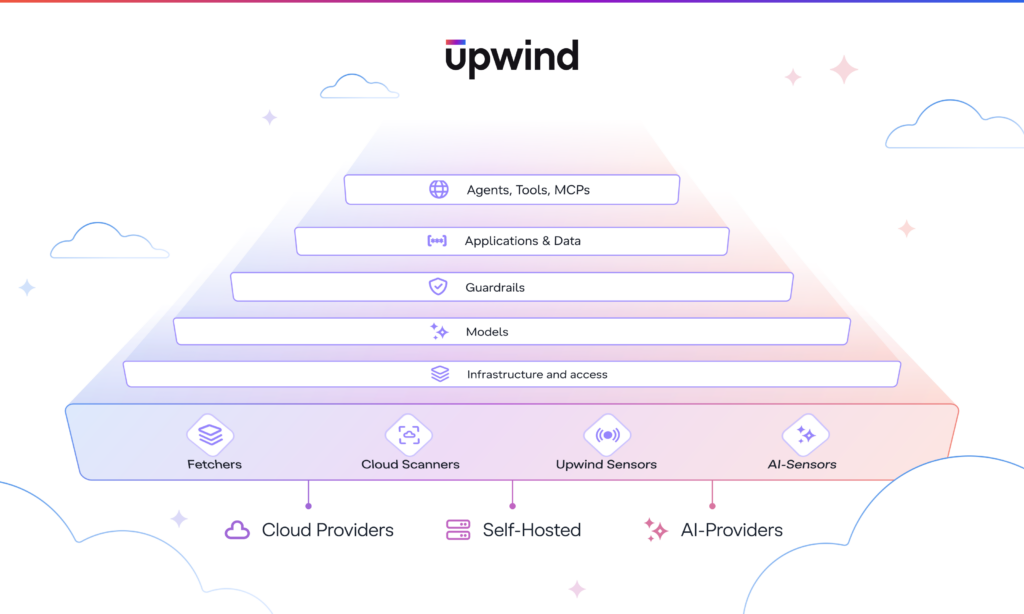
AI is entering production faster than many security teams can keep up. As teams embed AI into applications, developer workflows, and cloud operations, security teams need to know where AI runs, what it can access, and which risks need action. Upwind AI Security connects AI usage to realtime cloud context, giving teams a practical way […]
Upwind AI Security: Securing your AI stack from the inside-out
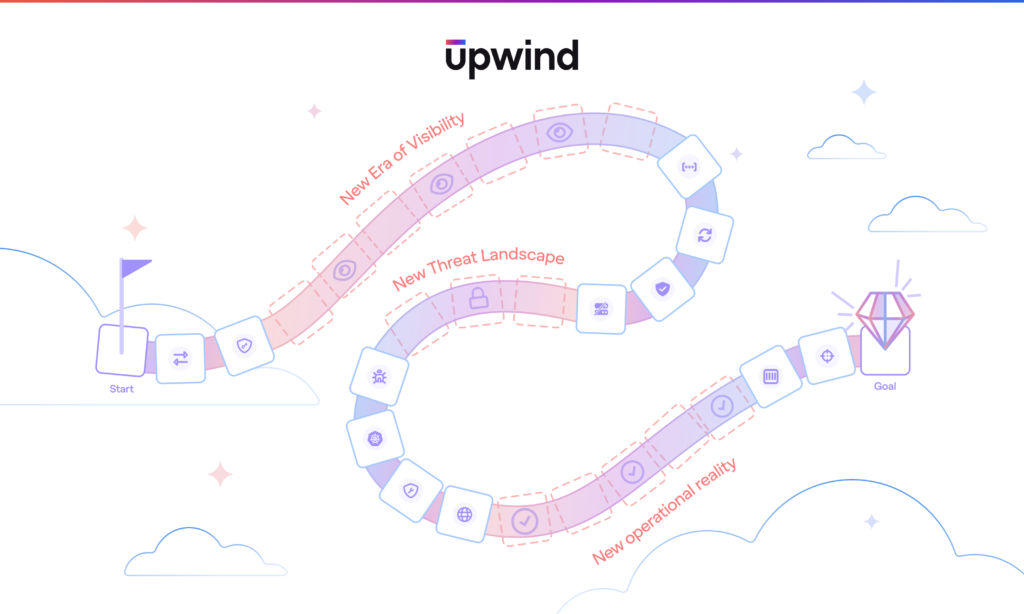
AI is changing how we build, work, and operate. It is moving from experimentation into production applications, customer experiences, developer workflows, and cloud operations. As AI moves closer to the core of the business, it is gaining access to the systems that matter most: sensitive data, internal tools, cloud services, and non-human identities. AI changed […]
Validate Real Cloud Risk with Red, the Validation Agent
After teams identify the risks that matter, the next challenge is proving which ones are actually exploitable. Severity scores, exposure labels, and long lists of findings can point teams in the right direction, but they do not always show whether an attacker has a viable path to impact. In cloud environments, that path often depends […]
Accelerate Cloud Security Investigations with Blue, the SecOps Agent
The AI threat landscape is moving faster on both sides. Attackers are using AI to scale campaigns, accelerate exploit development, and move faster from discovery to execution. Defenders need AI that helps them keep pace without adding noise or pulling teams away from the work that matters most. Prioritization helps teams focus on the risks […]

Move Faster From Cloud Risk to Remediation With Upwind Agentic Pack
Cloud security works best when teams can move from context to action in one place. Upwind already brings together runtime-powered security context across cloud infrastructure, applications, identities, workloads, APIs, and AI systems. Now, the Upwind Agentic Pack helps teams use that context faster across investigation, validation, and remediation workflows. Grounded in Upwind’s runtime-first platform, the […]

Introducing the Upwind MCP Server: Realtime Context for Stronger Cloud Security
Security teams already have enough findings to sort through. Vulnerabilities, misconfigurations, and alerts pile up every day, but only a limited number create real risk in production. The harder problem is knowing which issues are exposed, active, and worth fixing first. The Upwind MCP Server connects MCP-compatible clients to selected Upwind context and capabilities, helping […]

Prioritize Reachable Cloud Risk With Upwind Cloud Security Context
Cloud security teams are under pressure to move faster, but the volume of cloud risk keeps growing. Verizon’s 2025 DBIR found that vulnerability exploitation as an initial access vector increased 34% year over year, while IBM reported the global average cost of a data breach at $4.4 million. The issue is not that teams lack […]








