Runtime Cloud Security: Focus on the Risks Attackers Can Actually Reach
Cloud security teams are under pressure to move faster, but the volume of cloud risk keeps growing. Verizon’s 2025 DBIR found that vulnerability exploitation as an initial access vector increased 34% year over year, while IBM reported the global average cost of a data breach at $4.4 million.
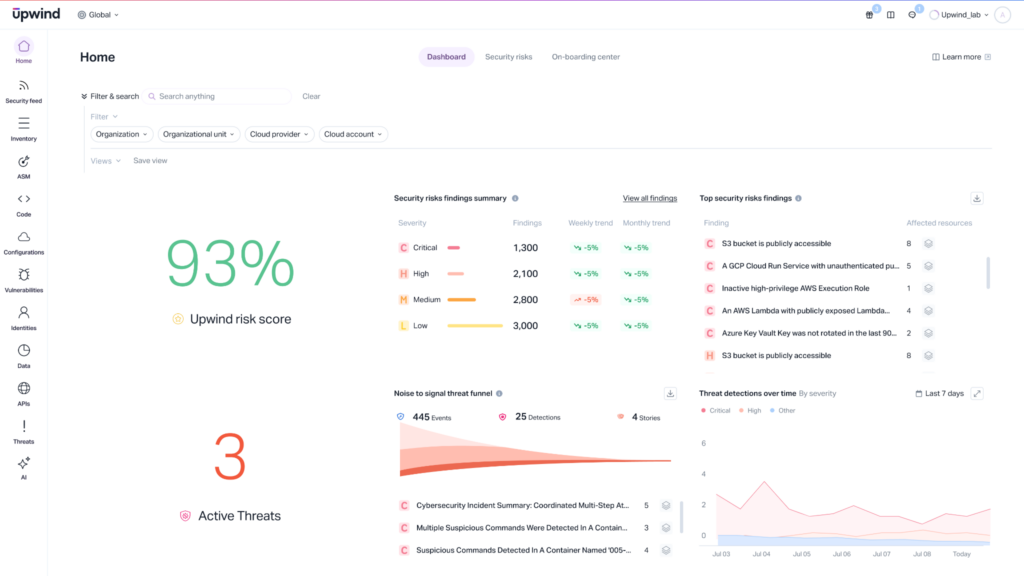
The issue is not that teams lack findings. It is that too many findings lack the context needed to act. Runtime cloud security helps close that gap by showing which risks are active, exposed, and connected to running workloads. Instead of prioritizing based on static severity alone, teams can use live workload, process, network, identity, API, and application behavior to focus on the issues that can create real impact.
Upwind applies this runtime-first approach across cloud deployments, configurations, workloads, and applications, giving teams real-time visibility from the inside out.
Static Findings Do Not Show Active Risk
Most cloud security programs still rely heavily on configuration checks, vulnerability scans, and asset inventories. These signals matter, but they do not always show whether a risk is reachable, running, or relevant to production.
That creates a prioritization problem. A critical CVE may sit in an inactive package or an isolated workload. A lower-severity issue may create more urgency if it runs inside an internet-facing service with access to sensitive data. Without runtime context, teams spend hours validating what deserves attention.
Runtime cloud security changes the question from “What could be wrong?” to “What is actually active, exposed, and behaving in a risky way?”
How Runtime Cloud Security Works
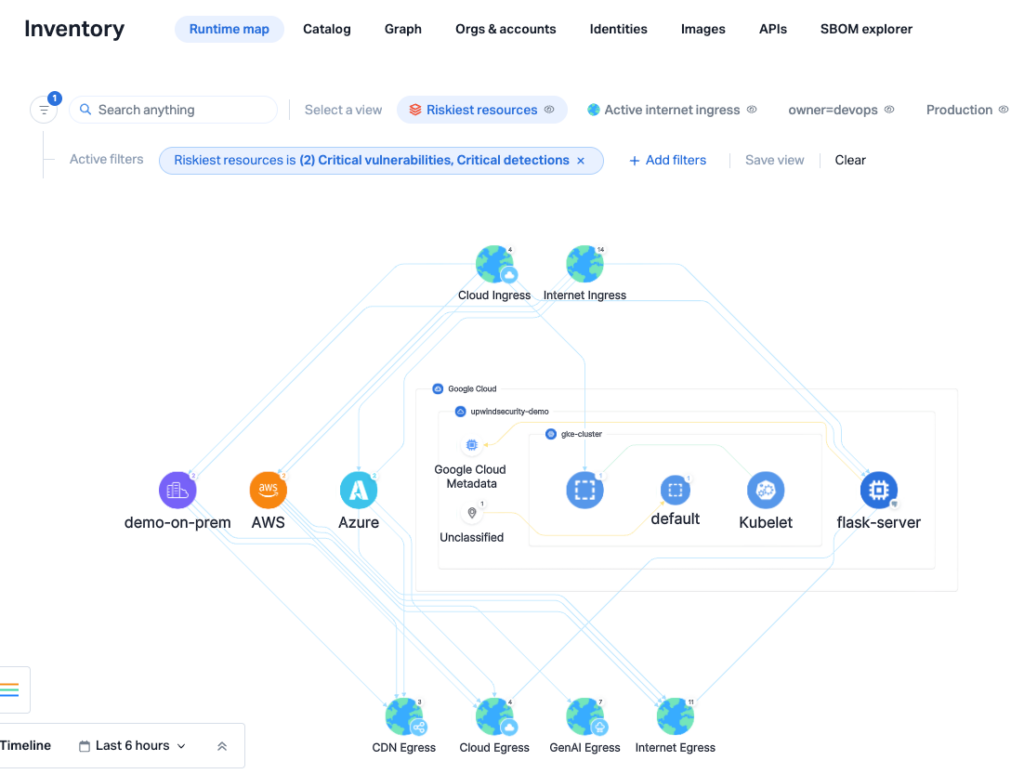
Runtime cloud security observes cloud environments while they operate. It connects live workload behavior with posture, vulnerability, identity, network, API, and application context.
In practice, this means teams can evaluate a finding based on real conditions. Is the workload running? Is the vulnerable component active? Is the service exposed? Is it communicating with sensitive systems? Is there unusual process or network activity?
Upwind’s runtime fabric brings this evidence together so teams can see how cloud assets behave in production, not just how they are configured.
Runtime Context Makes Prioritization More Accurate
Alert fatigue remains one of the biggest blockers in remediation. Mondoo’s 2025 State of Vulnerability Remediation report found that 53% of respondents cite alert fatigue as a top pain point.
Runtime context helps reduce that noise by validating risk against actual activity. Security teams can prioritize vulnerabilities in running workloads, investigate suspicious behavior with surrounding context already attached, and understand which posture issues create real exposure in production.
This also gives engineering teams clearer remediation guidance. Instead of receiving generic tickets tied to static findings, they can see why a risk matters, where it appears, and what runtime evidence supports the priority.

Practical Use Cases
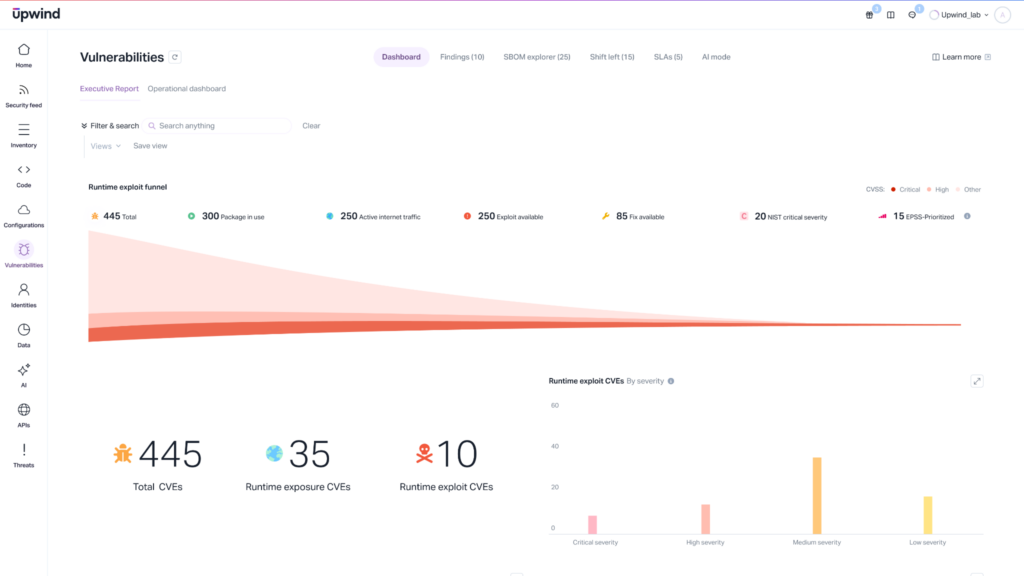
Prioritize Active Vulnerabilities
A team finds hundreds of critical vulnerabilities across containers and VMs. Runtime context shows which vulnerable components are active, exposed, and connected to sensitive services, helping the team fix the risks most likely to create impact first.
Investigate Suspicious Workload Behavior
A SOC analyst sees unusual process or network activity inside a workload. Runtime context shows the affected asset, related services, communication paths, and cloud relationships, helping the analyst understand scope and next steps faster.
Reduce Noise Across Cloud Posture Findings
A cloud security engineer reviews posture findings across accounts, clusters, and workloads. Runtime context helps separate theoretical issues from active risk by showing which findings relate to running infrastructure, reachable services, and real identity usage.
Runtime Cloud Security Turns Context Into Action
Cloud environments change too quickly for static analysis alone. Teams need live evidence to understand which risks are active, which systems are exposed, and where to act first.
With Upwind, security teams can connect posture, workload behavior, application activity, and threat detection through runtime context. The result is a more accurate way to reduce noise, investigate faster, and prioritize the risks attackers can actually reach. Contact us to learn more.