Detect Suspicious Communication with a Public DNS Resolver
We are excited to announce a new capability to detect unusual DNS resolver activity.
This detection notifies you of unusual behavior by a virtual machine or container in your cloud environment, which is communicating with a public DNS resolver that it hasn’t communicated with recently.
DNS Resolvers
Trusting your DNS resolvers is a critical part of your overall security hygine, since this is the component that maps out IP addresses for hosts connected to the Internet.
Indicators of Compromise
Due to its important nature, DNS resolution issues are often the cause of network outages. Errors such as misconfigurations in a single DNS server can cause widespread communication failures for all services that communicate with it, and they are typically very difficult to identify since teams often need to investigate each server individually in order to find issues.
DNS is also the focal point or frequent target for many attacks, due to its important role in internet communication. Attackers can hijack resources and cause them to communicate with a public DNS resolver in attempts to gain access to an environment or steal data.
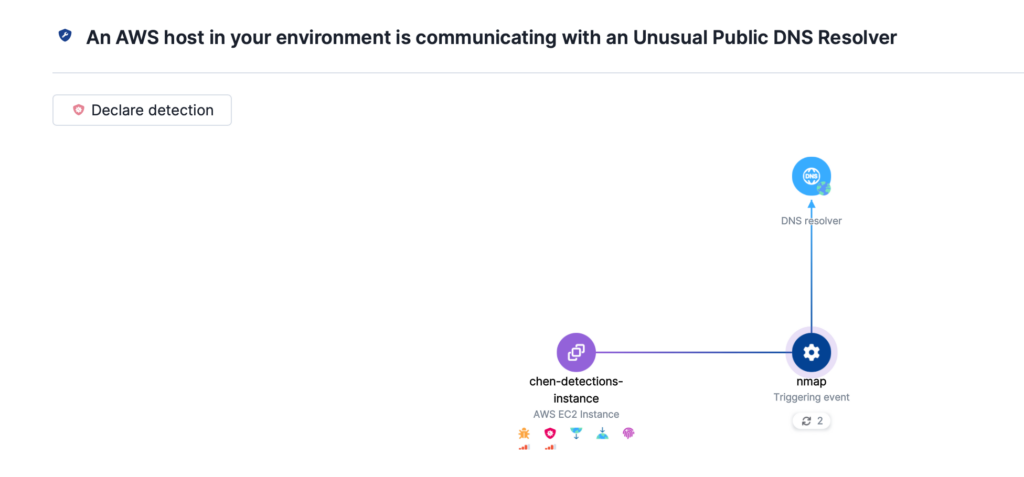
This detection notifies you of unusual behavior by a virtual machine or container in your cloud environment, which is communicating with a public DNS resolver that it hasn’t communicated with recently. This is suspicious because it deviates from the established baseline behavior of the resource within the environment and may indicate an attempt to use alternative DNS resolvers for bypassing network monitoring, exfiltrating data, or other malicious activities aimed at evading detection.
Upwind leverages runtime data to rapidly identify unusual DNS resolver communication and immediately alert you to suspicious activity. Read more about DNS resolver detections in the Upwind Documentation Center (login required).