Image Layers are now in the Upwind Console
Upwind’s Image Layers capability gives you deep visibility into how container images are built—so you can assign vulnerability ownership correctly, find root cause faster, and remediate issues more effectively across teams.
Most tools only show the final image state. Upwind breaks images down layer by layer, so you can see exactly where a vulnerability was introduced during the build process.
What Image Layers delivers
With Image Layers, you can finally answer the questions that matter in seconds:
- Which layer introduced this vulnerability?
- Is this owned by the base image team or the application team?
- Which Dockerfile instruction caused it?
- Was it later fixed or overwritten in another layer?
That’s the difference between “finding CVEs” and actually fixing risk.
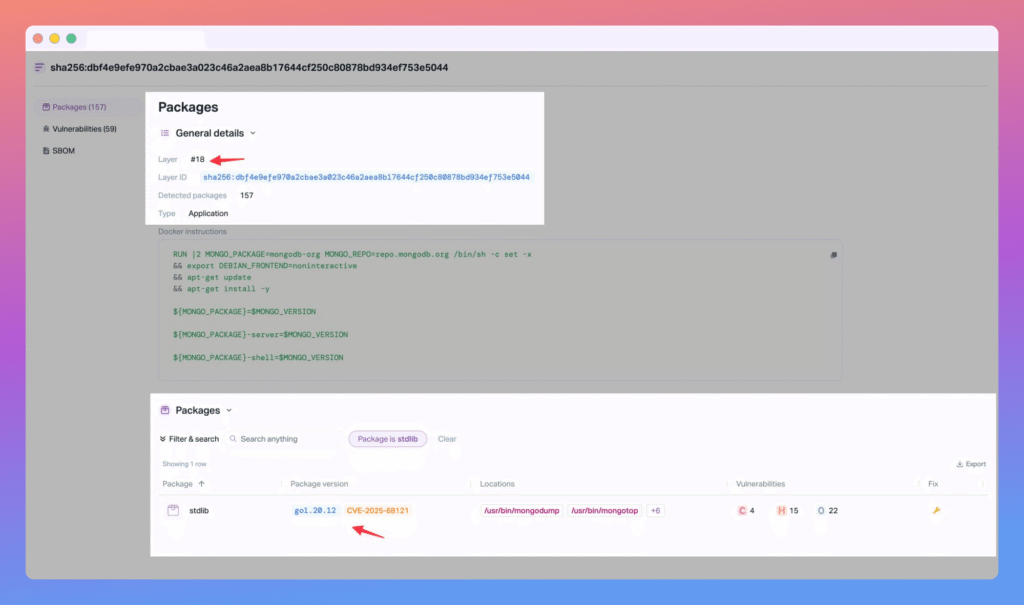
Layer-level vulnerability attribution
Upwind breaks container images into individual layers and pinpoints the exact layer that introduced each vulnerability—not just where it shows up in the final image.
Findings Go To The Right Team Immediately
Image Layers makes it easy to attribute ownership:
- Base image vulnerabilities (typically Platform / DevOps owned)
- Application vulnerabilities (typically Engineering owned)
So findings go to the right team immediately—without back-and-forth.
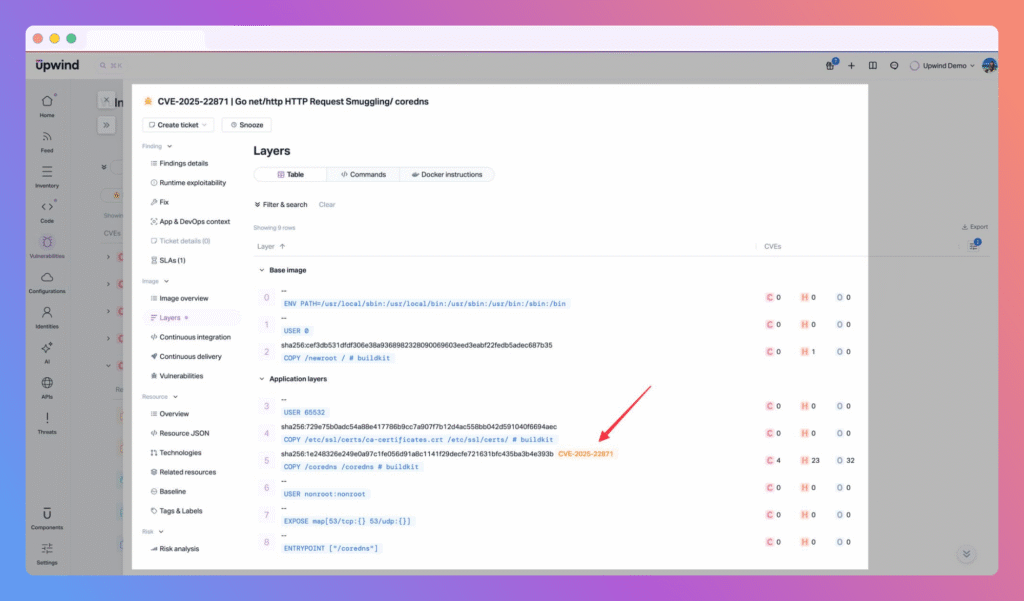
Build context visibility
Each layer is tied back to its Dockerfile instruction and command, giving developers concrete evidence of:
- what was run
- what changed
- and where to fix it
What you can do with Image Layers today
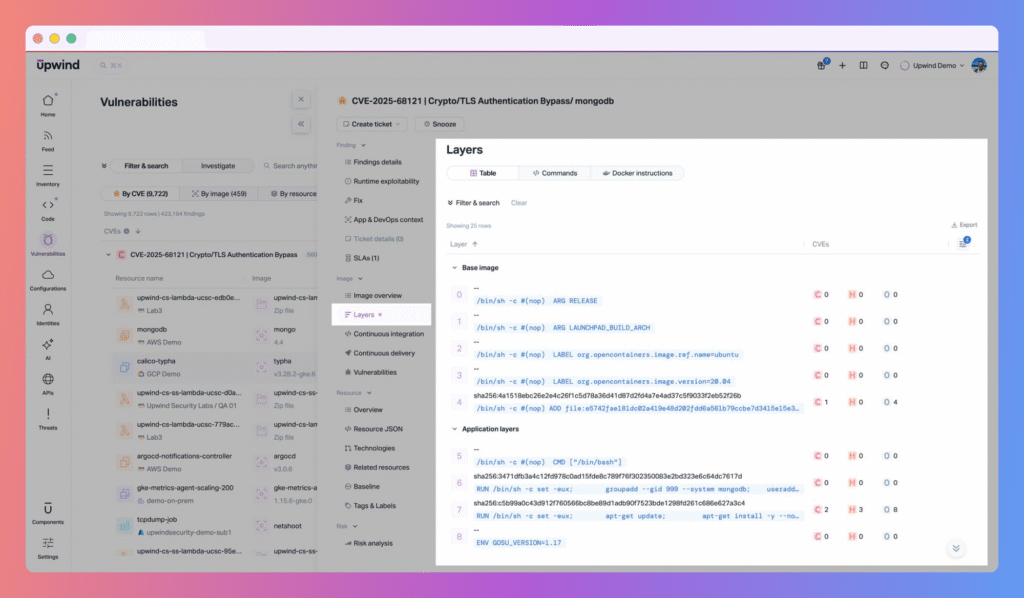
- Inspect images layer by layer (not just final state)
You can drill into an image and see a full layer breakdown, making it easy to understand how the image was assembled.
- See “introduced in layer” for every vulnerability
Each finding is tied to the exact introducing layer, so you know where the risk entered the build.
- Use per-layer SBOM visibility for better investigation
Upwind collects a layer-aware SBOM, so you can connect packages and vulnerabilities back to the layers where they appear.
- Trust the results even when layers change things later
Upwind accurately handles real-world builds where vulnerabilities are introduced, patched, or overridden by later layers—so the attribution stays meaningful.
- Get richer findings with supporting evidence
Vulnerability findings include more context to speed up triage and help teams remediate with confidence.
See It In Action
If you’d like to see how this feature fits into your environment – or to explore how Upwind can help you prioritize and remediate risk more effectively – schedule a customized demo with us. We’ll walk through your use cases, integrations, and security goals to show how Upwind delivers actionable cloud security at scale.