Introducing the Upwind MCP Server for Runtime Cloud Security
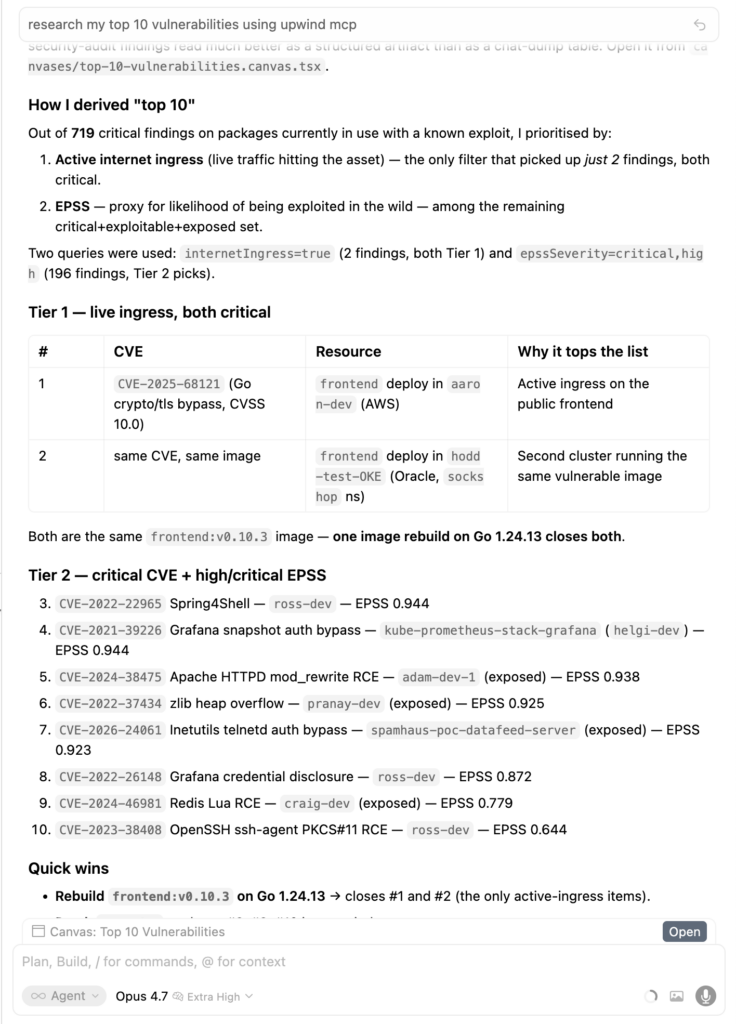
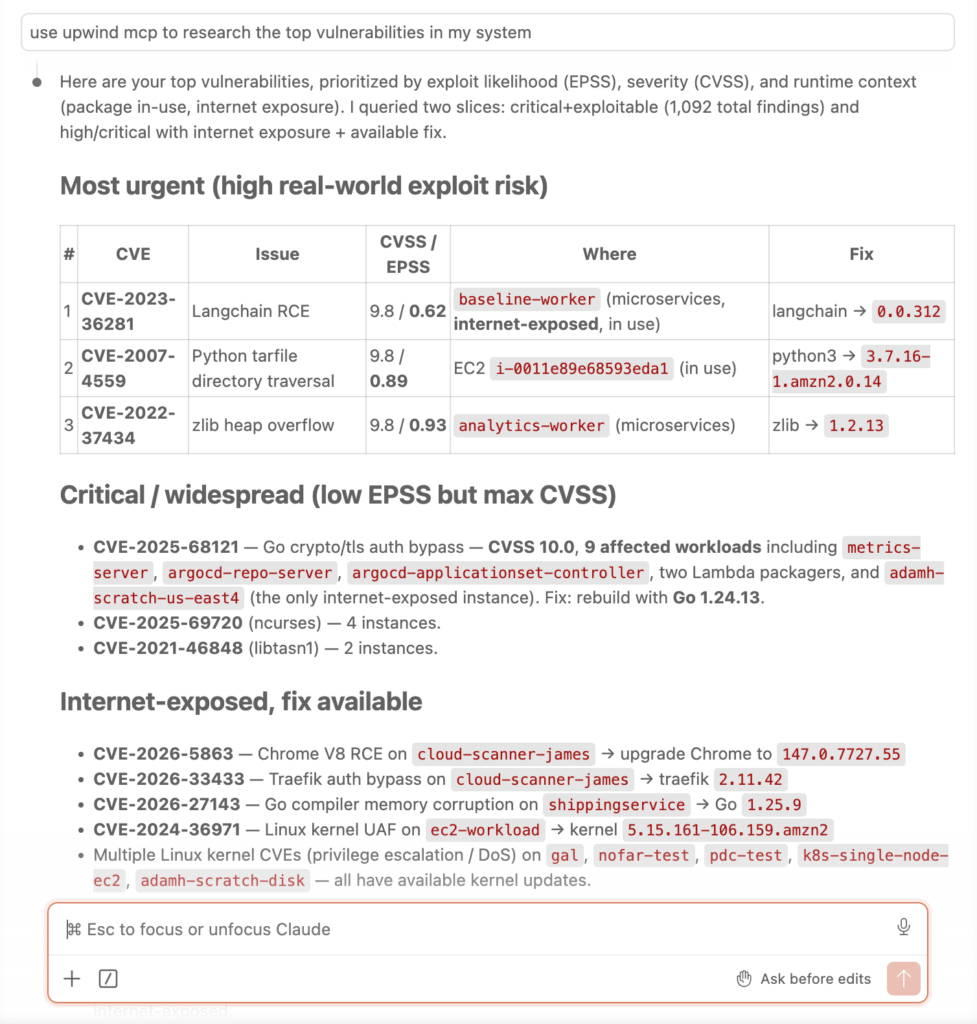
Security teams already have enough findings to sort through. Vulnerabilities, misconfigurations, and alerts pile up every day, but only a limited number create real risk in production. The harder problem is knowing which issues are exposed, active, and worth fixing first.
The Upwind MCP Server brings that runtime context into existing tools. With MCP support, customers can connect compatible clients to Upwind and use selected Upwind capabilities to investigate threats, analyze assets, review findings, triage vulnerabilities, and check compliance without building a custom integration for every use case.
Upwind already helps teams prioritize risk inside the platform by showing what is actually running, reachable, and active. The Upwind MCP Server extends that context into connected workflows, so teams can investigate and act with the same runtime information beyond the platform.
Put Runtime Context to Work Beyond the Platform
Static scans can find issues, but they often leave teams with long lists of findings and little guidance on what matters now. Security teams still have to validate exposure, confirm activity, identify ownership, and decide whether an issue deserves immediate action.
Runtime context changes that process. It shows how workloads, identities, network paths, and services behave in production, so teams can separate theoretical risk from real exposure.
The Upwind MCP Server brings that runtime context into connected tools and agent-based workflows. Instead of forcing teams to switch contexts or build custom integrations, it gives compatible clients a structured way to access selected Upwind capabilities.
What is the Upwind MCP Server?
The Upwind MCP Server lets MCP-compatible clients connect to Upwind and use selected platform capabilities.
MCP, or Model Context Protocol, gives AI clients and agents a structured way to connect with external systems, discover available tools, and interact with them. With MCP support, Upwind can make selected security context available to compatible clients, so teams can use Upwind data during investigations, asset reviews, vulnerability triage, compliance checks, and other supported workflows.
This matters because context determines priority. A vulnerability in a running, exposed workload deserves a different response than the same vulnerability in an inactive or unreachable asset. The Upwind MCP Server helps connected tools use that runtime context when teams investigate, prioritize, and respond.
What does this look like in practice?
Teams can connect MCP-compatible clients to Upwind’s hosted MCP Server and access supported Upwind capabilities through MCP. This gives teams a cleaner path to use Upwind security context outside the platform without creating a separate integration for every tool or workflow.
This supports key areas of the Upwind platform, including threats, detections, inventory, vulnerabilities, configuration findings, compliance, SBOM, API Security, Shift Left, workflows, policies, and webhooks.
For the current list of supported tools, setup steps, supported clients, and regional details, teams should use the Upwind MCP Server documentation.
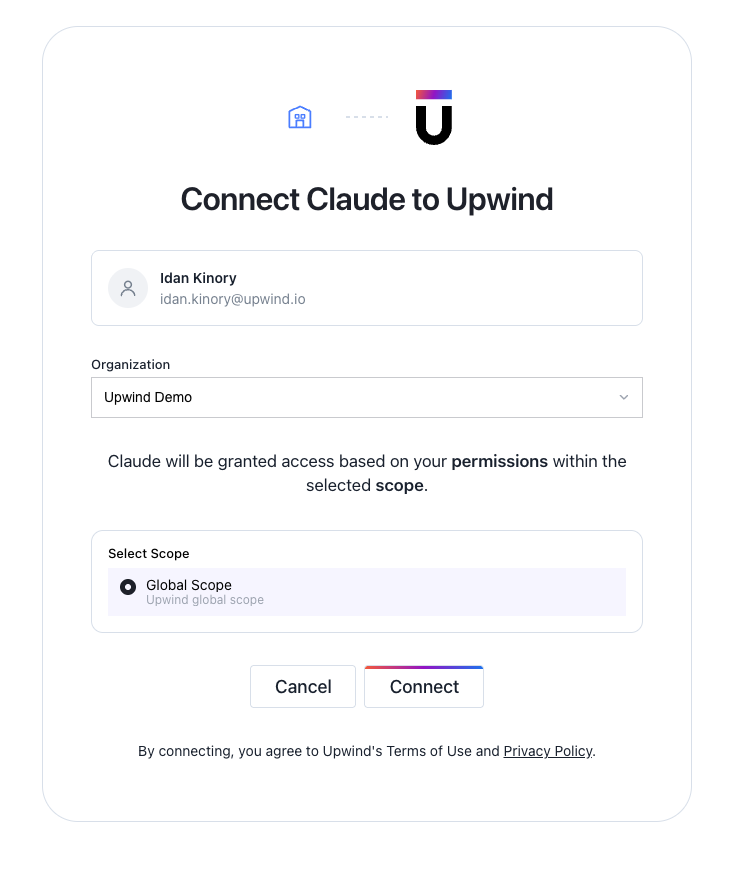
Upwind also supports authenticated remote MCP, so users can sign in through OAuth instead of managing long-lived credentials across different tools. For environments that require a local stdio connection, teams can use a remote MCP helper to connect to Upwind’s hosted server.
How does this help security teams move faster?
Security work rarely happens in one system. Teams investigate threats, review findings, open tickets, validate fixes, and coordinate with engineering across multiple tools. When every workflow needs separate context, teams lose time and risk decisions slow down.
The Upwind MCP Server helps teams carry runtime context into those workflows. A security engineer can investigate an active threat with workload context, review a vulnerable asset based on runtime activity, or check compliance findings with a clearer view of the environment behind them.
That helps teams:
- Spend less time validating low-priority findings
- Focus remediation on issues that are active, exposed, or reachable
- Give engineering teams clearer context for fixes
- Review threats, assets, vulnerabilities, and compliance findings from connected tools
- Make faster decisions with runtime-informed security data
Runtime context helps teams move from “what was detected?” to “what should we fix first?”
Focus on the risks that actually matter
Cloud security teams do not need more findings in more places. They need better context for deciding which risks require action.
Upwind solves that problem with runtime context. The Upwind MCP Server brings that same context into connected tools, helping teams investigate threats, analyze assets, review findings, and prioritize remediation based on what is actually happening in production.
Instead of chasing every possible issue, teams can focus on the risks that matter most.
Click here to learn more about Upwind’s approach to cloud security at runtime.