Expanding Compliance Coverage with New Industry Frameworks and Upwind’s Cloud Hygiene Framework
Cloud security teams are being asked to do more than ever. They need to prove compliance against growing regulatory demands, reduce configuration risk, and keep cloud environments lean, secure, and aligned with how they were actually designed to operate.
That is why we are excited to introduce several new frameworks now available in Upwind’s Configurations and Security Issues modules, alongside a new Upwind-native framework built to uncover a different class of cloud risk: the operational drift, unused assets, and waste that often accumulate silently over time.
New compliance frameworks now supported
Upwind now supports the following additional frameworks:
- CIS Amazon Web Services Foundations Benchmark v6.0.0
- NIST 800-171
- DORA 2024/1532
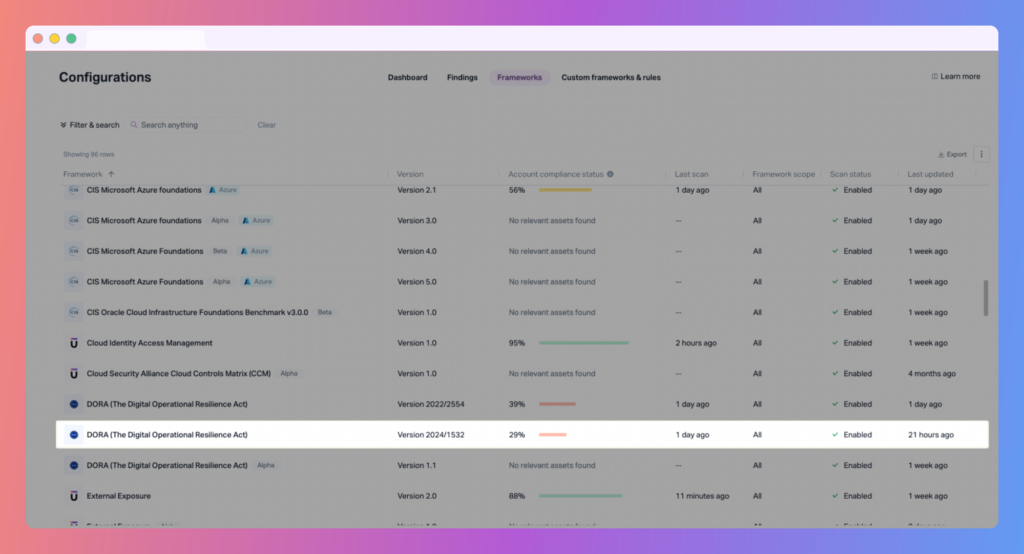
These additions expand coverage for teams operating in regulated industries and help organizations map cloud misconfigurations and security issues to the standards that matter most to them.
For customers, this means broader out-of-the-box compliance visibility and a faster path to identifying where cloud environments may fall short of internal requirements, industry expectations, or external audits.
Why these additions matter
Compliance is no longer a niche requirement. For many organizations, it is now a core part of cloud security operations.
Different teams face different pressures. Some need to align with widely adopted benchmarks such as CIS. Others need to meet strict controls for handling sensitive data under frameworks like NIST 800-171. Financially regulated organizations are also increasingly focused on operational resilience requirements introduced by regulations such as DORA.
By adding support for these frameworks, Upwind helps security and cloud teams:
- Assess environments against more of the standards their business cares about
- Prioritize remediation with clearer compliance context
- Support customer evaluations and proof-of-concept processes more effectively
- Strengthen posture across multi-cloud environments without relying on disconnected tooling
Introducing the Upwind Cloud Hygiene Framework
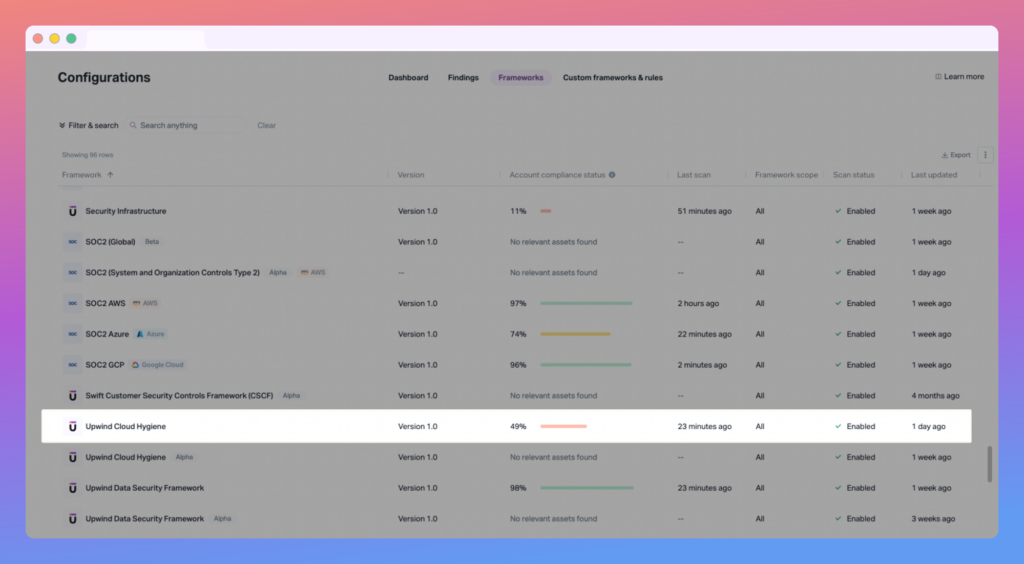
Alongside these industry frameworks, we are also launching the Upwind Cloud Hygiene Framework.
This is a new Upwind-native framework designed to identify misconfigurations and conditions that leave cloud assets unused, disconnected, or no longer aligned with the intended architecture.
In practice, these issues often fall between traditional security and operations workflows. They may not always look like critical vulnerabilities at first glance, but they can create real risk over time by increasing attack surface, adding unnecessary complexity, and driving avoidable cloud spend.
The Cloud Hygiene Framework is meant to bring these issues into focus.
What the Cloud Hygiene Framework looks for
This first release includes checks designed to surface signs of waste, architectural drift, and stale or orphaned resources across cloud environments.
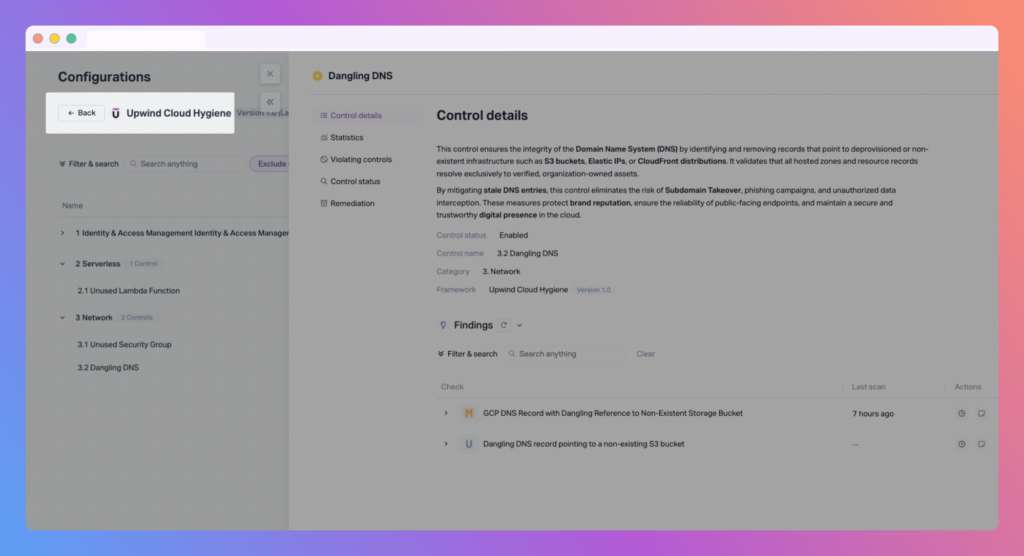
Examples include:
- An unused AWS Lambda function running on an outdated runtime
- An inactive high-privilege AWS execution role
- Unused network access control lists that should be removed
- An AWS IAM role that has not been used for more than 90 days
- A dangling DNS record pointing to a non-existing S3 bucket
- A GCP DNS record with a dangling reference to a non-existent storage bucket
- AWS serverless applications with missing deployed functions
- Azure serverless applications with missing deployed functions
These are the kinds of findings that may not always be captured by traditional compliance benchmarks alone, but they matter for both security and efficiency.
Security, hygiene, and cost are increasingly connected
Cloud environments rarely stay clean on their own.
As teams move quickly, infrastructure changes. Services are deprecated. Roles remain active long after they are needed. DNS records outlive the resources they were meant to point to. Serverless applications evolve, but pieces are left behind. Over time, this creates an environment that is harder to secure, harder to understand, and more expensive to operate.
That is where cloud hygiene becomes valuable.
By highlighting misconfigurations tied to unused infrastructure, stale privileges, and architectural drift, Upwind helps teams go beyond basic compliance and address the day-to-day realities of managing cloud environments at scale.
This also creates a useful bridge between security and FinOps goals. Reducing waste is not only about lowering cost. It is also about shrinking unnecessary exposure and making the environment easier to govern.
A broader view of cloud risk
With the addition of CIS AWS Foundations Benchmark v6.0.0, NIST 800-171, DORA 2024/1532, and the new Upwind Cloud Hygiene Framework, Upwind continues to expand how organizations can assess and improve their cloud posture.
This release is about more than adding new boxes to check. It is about giving teams better visibility into both formal compliance requirements and the practical issues that weaken cloud environments over time.
When security, compliance, architecture, and operational hygiene are viewed together, teams are in a much stronger position to reduce risk and act with confidence.
See It It In Action
Compliance coverage is important, but real value comes from being able to connect those frameworks to actionable findings across your environment. With these new additions, Upwind helps teams not only align to more standards, but also uncover hygiene and drift issues that traditional frameworks often miss.
If you’d like to see how this feature fits into your environment – or to explore how Upwind can help you prioritize and remediate risk more effectively – schedule a customized demo with us. We’ll walk through your use cases, integrations, and security goals to show how Upwind delivers actionable cloud security at scale.