Stop Chasing Ghosts: Why You Need Layer-Level Visibility in Your Container Images
The industry has a “shift left” problem. We’ve become excellent at scanning images and generating massive spreadsheets of vulnerabilities. But for most security teams, a scan result is just the start of a forensic investigation. You find a critical CVE, but then the real work begins:
Is this in the base image?
Did a developer add this in a RUN command?
Who actually owns the fix?
Traditional scanners treat container images like a black box—a monolithic artifact where security is “all or nothing.” This creates a massive “noise” problem where security and engineering teams waste hours chasing ghosts in the build history instead of remediating risk.
The “Old Way” vs. The Upwind Way
The Old Way involves manual back-and-forth. Security sends a ticket, Engineering says “that’s not our code,” and the ticket dies in a backlog. You’re scanning often, but fixing slowly because you lack the context of how the image was constructed.
The Upwind Way is runtime-first and context-aware. By providing deep visibility into image layers, we bridge the gap between the static build process and the active runtime environment. We don’t just tell you something is broken; we show you exactly which architectural decision introduced the risk.
The Questions Traditional Tools Can’t Answer
If you are relying on standard image scanning, your team is likely struggling to answer these four questions:
- Who owns this fix? Is this a vulnerability inherited from the golden image managed by DevOps, or an npm package added by a developer?
- What was the specific command? Which line in the Dockerfile—specifically—introduced the vulnerable library?
- Where is the blast radius? If this base image is compromised, which downstream application layers are effectively “poisoned”?
- Is this actually exploitable in production? Without knowing the layer context, how can you correlate the vulnerability with actual runtime behavior?
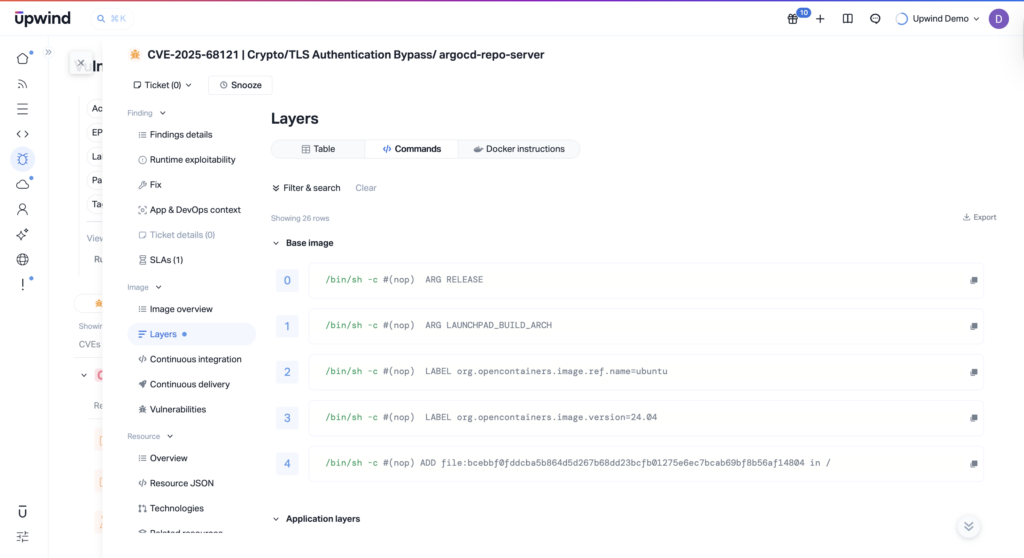
Technical Breakdown: Precision Through Image Layers
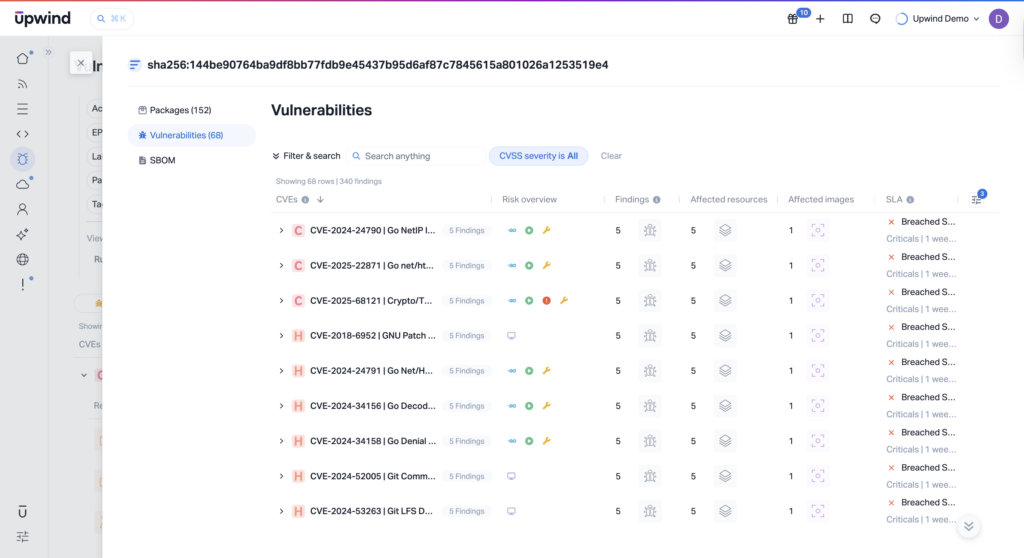
With the release of Image Layers, Upwind provides granular telemetry into the container construction process. We’ve moved beyond the “flat” view of an image to a structured, 1:1 mapping of the build history.
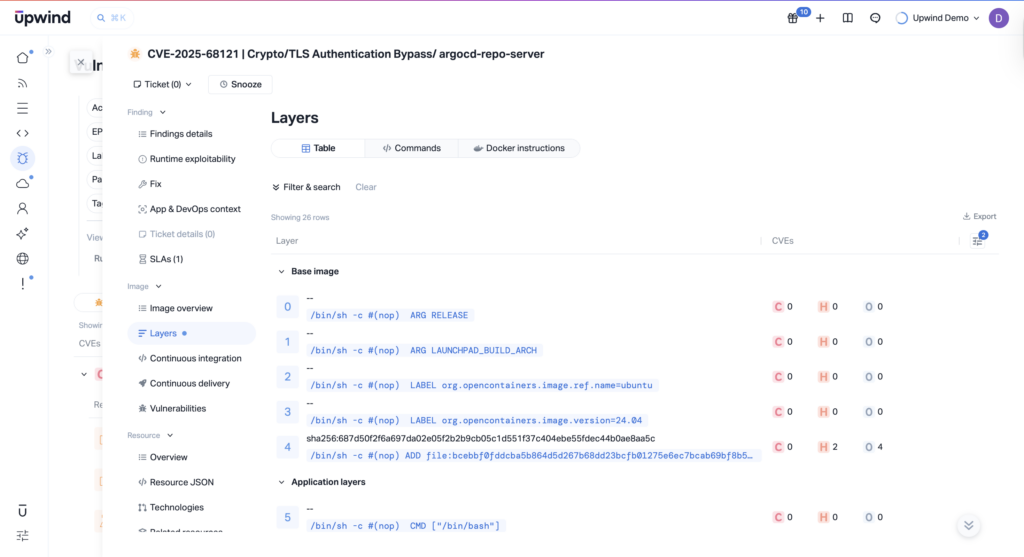
Layer-Level Vulnerability Attribution
We’ve integrated layer context directly into the vulnerability finding. By leveraging eBPF-powered runtime data and cross-referencing it with the image’s manifest, Upwind identifies the precise layer and the associated build step (e.g., RUN, COPY, ADD) where a vulnerability was introduced.
Definitive Ownership Mapping
This is where we eliminate friction. Upwind now automatically categorizes vulnerabilities into two distinct buckets:
- Base Image Vulnerabilities: Routed to Platform and DevOps teams for global patching.
- Application-Level Vulnerabilities: Routed to the specific Engineering pod responsible for that service.
Full Build Transparency & SBOM Export
Visibility shouldn’t be trapped in a UI. We provide a full layer-by-layer breakdown with the ability to export Software Bill of Materials (SBOM) data for the entire image or a specific layer. This allows for deep forensic audits and compliance reporting that actually reflects the build architecture.
The Impact
Security is a game of speed. When you provide engineers with a ticket that says “CVE-2024-XXXX introduced in Layer 4 via ‘RUN apt-get install…'” instead of a generic PDF report, everything changes.
- 90% Reduction in Triage Time: No more manual “Dockerfile archeology” to find where a package came from.
- Elimination of “Finger-Pointing”: Clear demarcation between platform and application code.
- Signal over Noise: Focus your remediation efforts on the layers that are actually active in your runtime environment.
See It In Action
Stop treating your containers like compiled binaries and start seeing them as a traceable stack of architectural layers. With Upwind’s Image Layers, you get a transparent view of your build process mapped directly to your risk profile. We provide the technical evidence needed to turn security findings into immediate developer action, ensuring that your “Shift Left” strategy actually results in a “Fix Fast” reality.
If you’d like to see how this feature fits into your environment – or to explore how Upwind can help you prioritize and remediate risk more effectively – schedule a customized demo with us. We’ll walk through your use cases, integrations, and security goals to show how Upwind delivers actionable cloud security at scale.