Validate Cloud Risk With Red Agent
After teams identify the risks that matter, the next challenge is proving which ones are actually exploitable. Severity scores, exposure labels, and long lists of findings can point teams in the right direction, but they do not always show whether an attacker has a viable path to impact.
In cloud environments, that path often depends on how multiple conditions connect. A reachable workload, vulnerable image, public endpoint, permissive network rule, unauthenticated API, active identity, or sensitive downstream service. The risk is not just the individual finding. It is the path those findings create together.
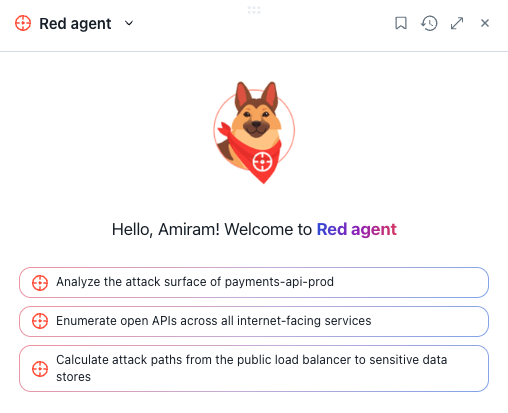
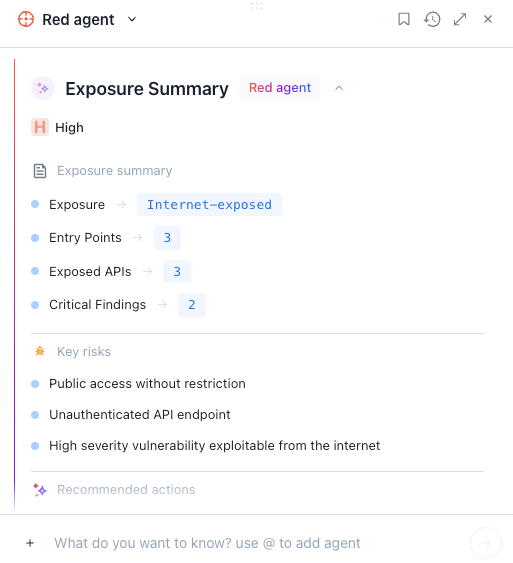
Red Agent, part of the Upwind Agentic Pack, brings agentic AI into cloud risk validation. It analyzes exposure, attack paths, vulnerabilities, APIs, identities, and runtime context to help teams understand what an attacker could actually reach, exploit, and chain together.
Validation Requires More Than Severity Scores
Severity scores help teams understand potential impact, but they do not prove real exploitability. In cloud environments, the same finding can carry very different risk depending on where it runs, whether it is reachable, and what it connects to.
That context matters even more as AI accelerates the threat landscape. When attackers can move faster from discovery to execution, teams need to know not only what risks are severe but actually exploitable in their environment.
Red Agent helps teams move beyond static prioritization by validating risk against real cloud context so they can focus on the issues most likely to create real business impact.
How Red Agent Validates Attack Paths
Instead of treating exposure as a flat label, Red Agent evaluates cloud risk from an offensive perspective. It looks at what is reachable, what is misconfigured, what is vulnerable, which APIs are exposed, which identities are involved, and how those signals could connect into a real attack path.
Red Agent helps teams understand:
- Which exposed assets create meaningful risk
- Whether a finding is reachable and exploitable
- How an attacker could move from an entry point to a sensitive asset
- Which vulnerabilities, APIs, identities, and permissions compound the risk
- What evidence supports prioritization and remediation
- Which actions can reduce the highest-impact attack paths
Teams can focus remediation on the attack paths most likely to create real impact, backed by evidence of which risks are reachable, exploitable, and connected across their cloud environment.
Exposure Alone Does Not Prove Exploitability
Internet exposure is an important signal, but it does not make every exposed asset equally urgent. Some exposed assets sit behind authentication, serve limited functionality, or have no meaningful path to production systems or sensitive data.
Risk increases when exposure becomes a usable entry point. That may mean an unauthenticated API tied to sensitive data, a vulnerable workload with permissive network access, or an overprivileged identity that can expand the blast radius.
Red Agent helps teams validate whether exposure creates a real path to impact, so they can prioritize the exposed assets that are reachable, exploitable, and connected to business-critical systems.
Why Runtime Context Makes Red Agent Different
A model can summarize a vulnerability, but it cannot determine real cloud risk without context around reachability, exposure, workload behavior, identities, APIs, and runtime activity.
The Upwind Agentic Pack is grounded in Upwind’s runtime-first cloud security platform, so investigation and validation start from what is actually running, exposed, communicating, and active in production.
In the broader Agentic Pack workflow, Blue Agent helps teams investigate suspicious activity and build the evidence-backed incident story. Red Agent builds on that work by validating whether prioritized cloud risks are reachable, exploitable, and connected to real impact.
Bring Agentic Validation Into Cloud Security
Red Agent gives teams a faster way to validate cloud risk with attacker-informed context and runtime-backed evidence. As part of the Upwind Agentic Pack, it helps security teams understand which risks are truly exploitable and which actions should take priority.