Accelerate Cloud Investigation With Blue Agent
The AI threat landscape is moving faster on both sides. Attackers are using AI to scale campaigns, accelerate exploit development, and move faster from discovery to execution. Defenders need AI that helps them keep pace without adding noise or pulling teams away from the work that matters most.
Prioritization helps teams focus on the risks and signals that matter, but it does not complete the investigation. Once suspicious activity surfaces, teams still need to understand what happened, which systems were involved, whether the behavior was expected, and what evidence supports the next step.
Blue Agent, part of the Upwind Agentic Pack, brings agentic AI into cloud security investigation. It helps teams move from prioritized cloud alerts to validated responses by investigating suspicious activity using runtime cloud context, connecting related evidence, and building the incident story faster.
Blue Agent Brings Agentic AI to Cloud Investigation
Blue Agent is the investigation agent in the Upwind Agentic Pack. It helps analysts move through an investigation without manually chasing every pivot across tools.
When suspicious activity appears, Blue Agent analyzes the signal alongside related runtime events, workload behavior, cloud assets, identities, vulnerabilities, exposures, permissions, and reputation data. It connects the evidence into an investigation path the analyst can review, question, and extend.
Blue Agent helps teams understand:
- What happened before, during, and after the alert
- Which workloads, assets, identities, processes, files, and connections were involved
- Whether the activity looks malicious, benign, or inconclusive
- What evidence supports escalation, continued investigation, or closure
- Which follow-up queries can move the investigation forward
Blue Agent does more than summarize what already exists. It works across runtime and cloud context to surface related evidence, organize the investigation, and help teams move toward a supported decision.
Why Runtime Context Makes Blue Agent Different
Agentic AI only works in cloud security when it has the right context. A model can summarize an alert, but it cannot investigate risk without understanding the environment behind it.
Blue Agent is grounded in Upwind’s runtime-first cloud security platform. That means investigations include how workloads behave, which identities are active, which services communicate, where exposure exists, and which risks connect to real activity.
A vulnerable workload, suspicious connection, or identity action can mean very different things depending on whether it is active, exposed, reachable, or tied to sensitive systems.
Blue Agent brings that context into the investigation so teams can understand what happened faster and make better decisions about what comes next.
Blue Agent in Practice
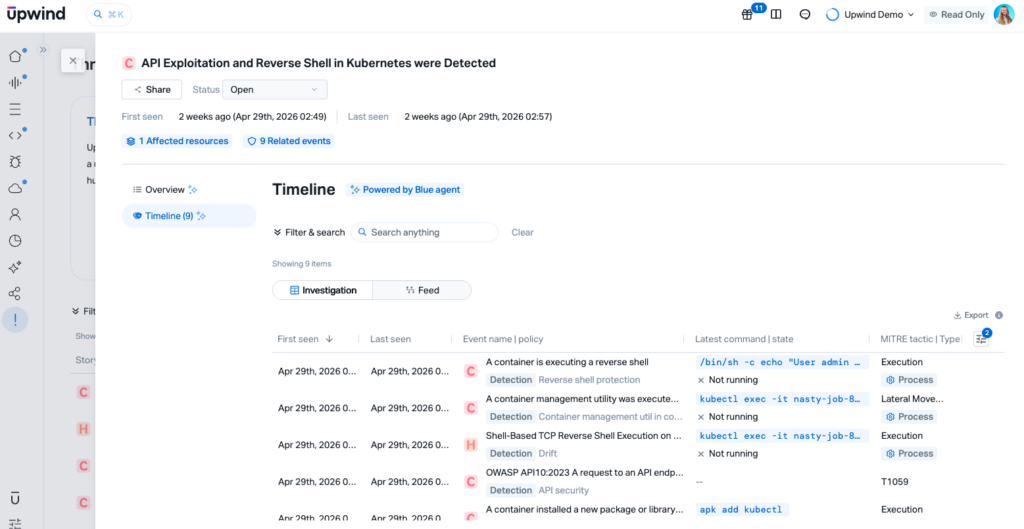
A new alert flags suspicious activity tied to a production workload. The alert has already been prioritized because it connects to real runtime behavior, but the team still needs to understand what happened.
Blue Agent reviews the related activity across processes, files, network connections, domains, cloud assets, identities, vulnerabilities, exposures, and reputation signals. It connects those signals into a timeline, highlights related evidence, and shows which systems were involved.
Instead of manually building every query, the analyst can use Blue Agent to follow the investigation path, ask follow-up questions, and preserve evidence for review or handoff.
Bring Agentic Investigation Into Cloud Security
Blue Agent gives teams a faster way to investigate prioritized cloud alerts with runtime context, evidence, and guided next steps. As part of the Upwind Agentic Pack, it helps security teams move from investigation into the broader agentic workflow for validation and response.





