Find & Fix Cloud Misconfigurations
Trusted by hundreds of enterprises around the world
Discover how organizations eliminate critical risks with Upwind



Discover All of Your Cloud Assets for Complete Visibility
- Map every cloud asset instantly
Automatically inventory all services, identities, and workloads across every cloud and account.
- See every layer of your environment
Gain unified visibility from compute to network to APIs — no blind spots or hidden infrastructure.
- Eliminate unmanaged risk
Ensure every asset is tracked, monitored, and secured as part of your cloud estate.
Leverage Cloud Context to Understand Asset Relationships
- Unified relationship mapping
Visualize how workloads, services, and identities interact across cloud boundaries.
- Reveal real attack paths
Understand how risk can move laterally between systems to target critical assets.
- Align ownership for accountability
Link assets to teams so issues are quickly resolved by the right people.
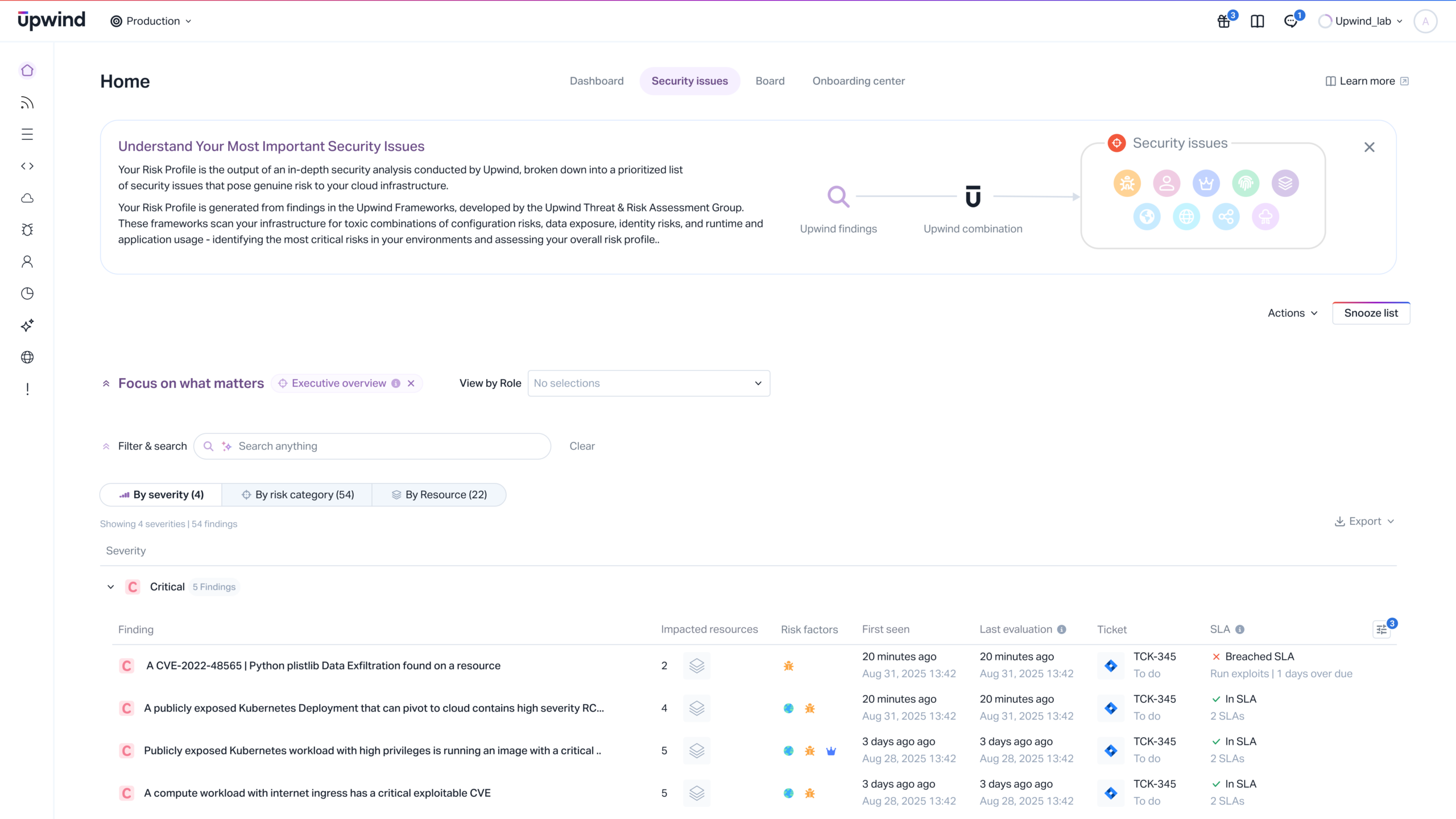
Proactively Identify Exposures & Their Potential Impact
- Context-aware risk insights
Combine asset context, privileges, and connectivity to surface true high-risk exposures.
- Prioritize by blast radius
Focus on fixes that materially reduce real attack surface — not just alert volume.
- Reduce noise and false positives
Break out of static, siloed findings and escalate only what actually matters.
Discover Risks & Ensure Compliance
- Continuous compliance monitoring
Automatically assess posture against standards like CIS, HIPAA, NIST, and more.
- Pinpoint critical control failures
Highlight the gaps that create immediate exposure or regulatory impact.
- Streamline audits and reporting
Maintain always-current evidence and remediation history for faster certification.
Discover Vulnerabilities & Threats in Context
- Deep scanning across compute and storage
Detect misconfigurations, exposed secrets, malware, and exploitable vulnerabilities.
- See what attackers can actually reach
Filter findings using network and identity context to avoid wasting effort.
- Resolve risk faster with clarity
Equip teams with clear prioritization and guidance on where to start.
Discover, Map and Prioritize Critical Risks