Secure Human & Non-Human Identities
Discover human and machine identities across clouds. Understand who has access to what and enforce least privilege access across your services.
Trusted by Leading Enterprises Around the World
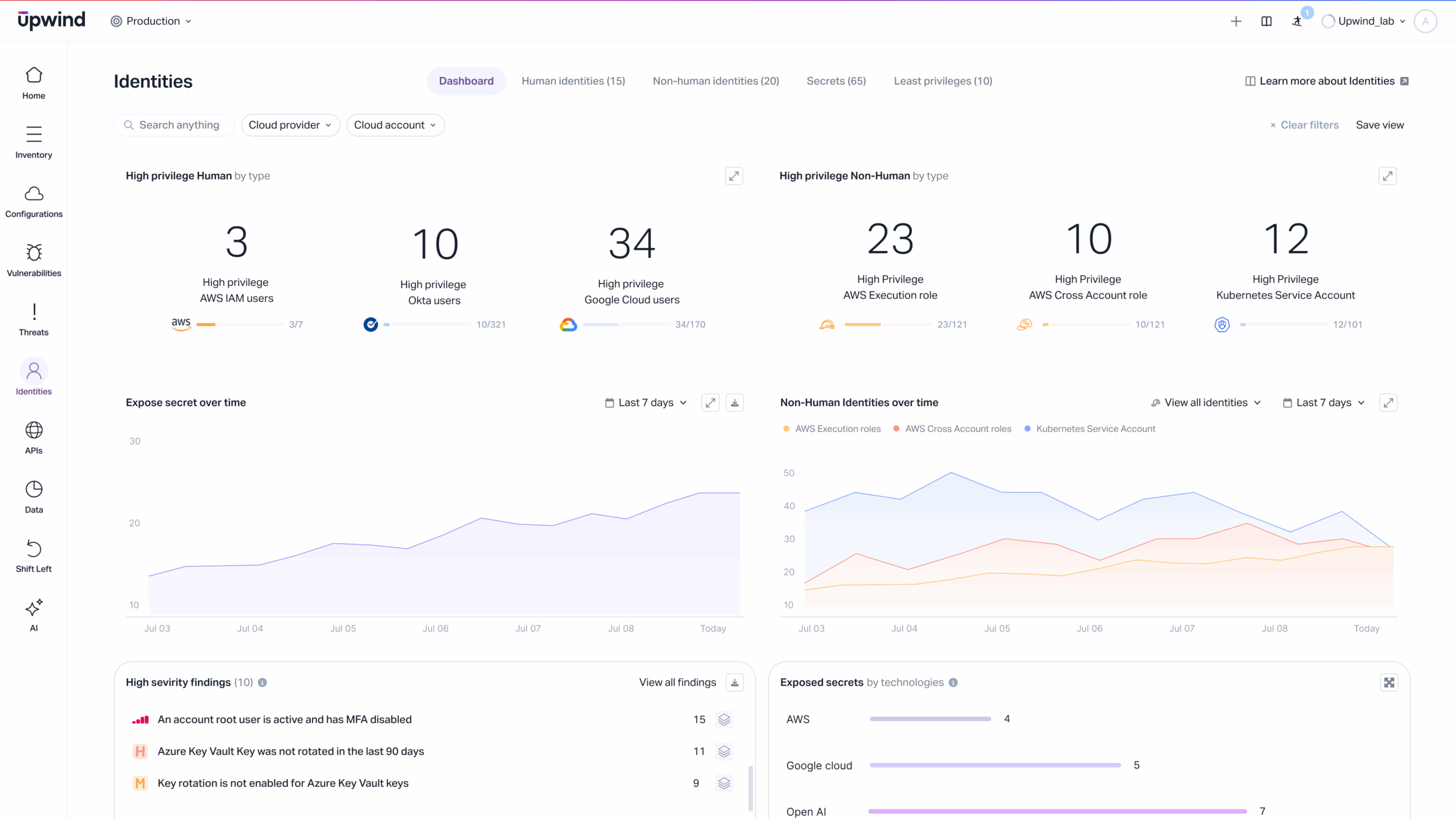
Discover & Secure Cloud Identities at Scale
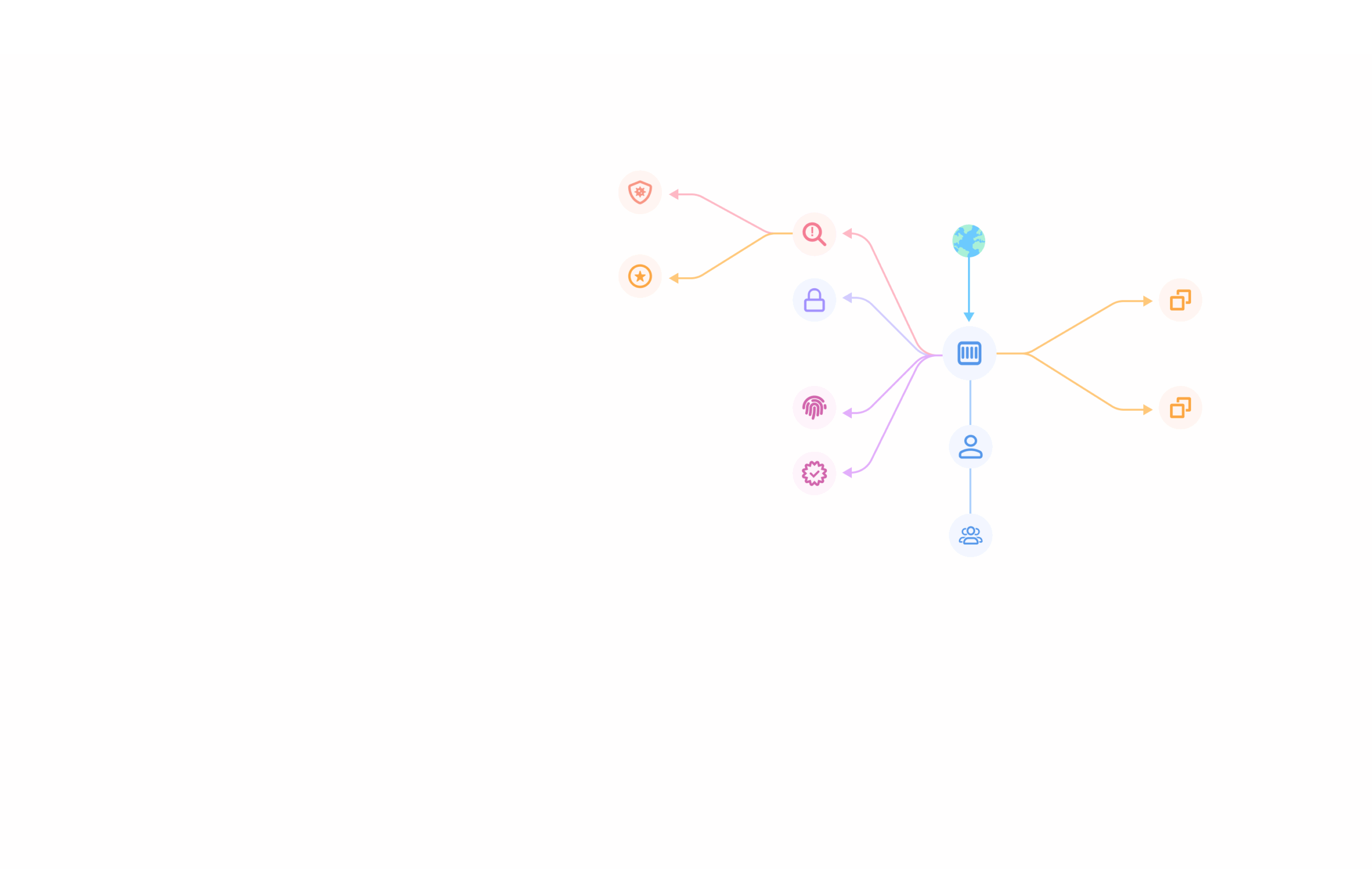
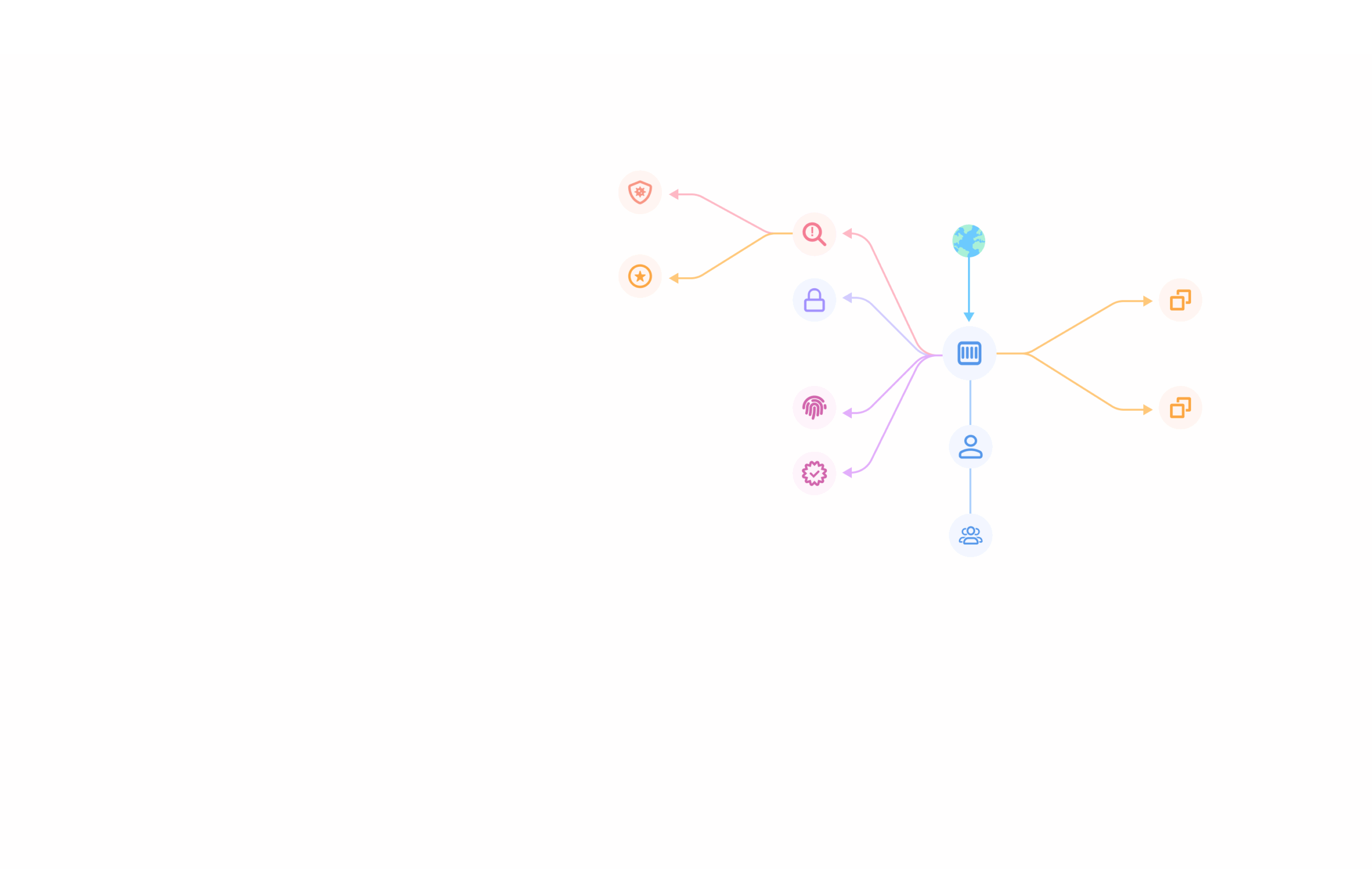
Map Permissions from Identity Providers to Cloud Resources
Untangle the complex flow of permissions from identity providers such as Okta, MSFT Entra, Ping Identity, or OneLogin all the way through to cloud provider IAM groups, roles, and the underlying resource permissions. Gain a unified view that clearly shows how identities translate into real access across your cloud environment.
Classify Access Levels Across Roles and Identities
Automatically classify identities and roles based on the type and level of access they hold. Distinguish between risky identities with high-impact privileges (write, modify, create) and those with lower-impact rights (read, view, manage). Understand which identities pose the greatest risk and require immediate attention.
Correlate Identity Permissions with Cloud Posture
Connect identity permissions directly to your cloud security posture to correlate identity context with exposed resources and critical vulnerabilities. Identify where risky permissions align with sensitive assets, giving you the context needed to prioritize remediation and reduce the blast radius of potential attacks.

Analyze Impact of Lost Secrets and Unused Roles
Perform in-depth analysis of unused or stale roles and exposed secrets. Detect secrets within containers and VMs, and map them back to the identities and permissions that could exploit them. Proactively eliminate unnecessary roles and remediate lost secrets to close security gaps.
Baseline Identity Access and Detect Threats
Use cloud activity logs to continuously monitor identity behavior over time. Establish baselines for normal access patterns and detect anomalies or threats in seconds. This proactive approach helps you quickly identify compromised identities or privilege misuse before they escalate.
Discover how organizations manage and secure cloud identities with Upwind
Upwind’s ability to not only identify and provide visibility into identities but also baseline their behavior has provided us with a new level of identity understanding. Using Upwind, we have been able to eliminate risky privileges, reduce the attack surface and streamline compliance.

With Upwind, we are able to identify any vulnerabilities and can prioritize them for remediation — helping us operate more efficiently and securely.

Upwind’s ability to deeply prioritize risks and focus on what is critical has empowered our team with 7x faster time to remediation.

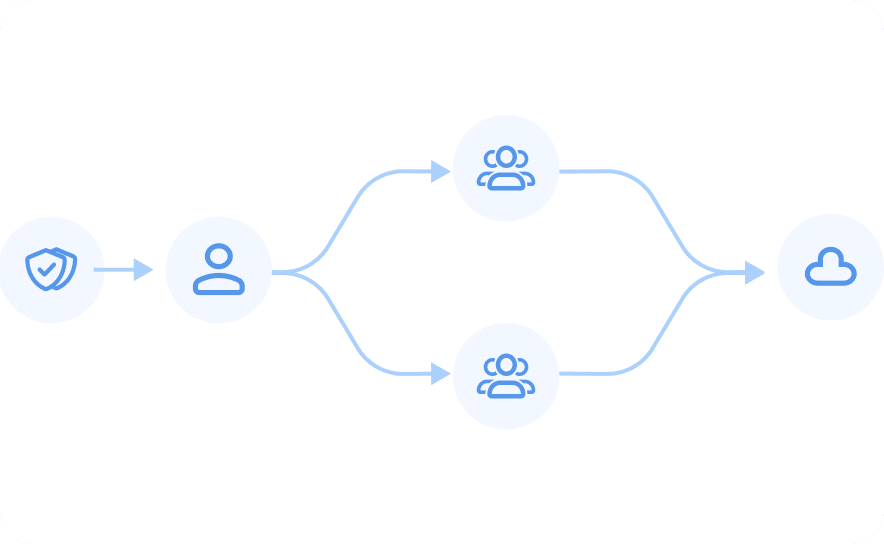
Discover and Secure Identity Access at Scale
Understand identity access from source to destination. Discover & analyze human and non-human identities across clouds. Eliminate unused or overly permissive roles and enforce least privilege access.

Discover Identities from the
Source (idP & cloud IAM)
Find Overly Permissive Roles
and Exposures
Avoid Breaches and Prioritize
Identity Risks
Secure Human & Non-Human Identities with Upwind
Discover human and machine identities across clouds with Upwind. Understand who has access to what and enforce least privilege access across your services.