Secure Hosts, Containers, VMs, Serverless Functions & APIs
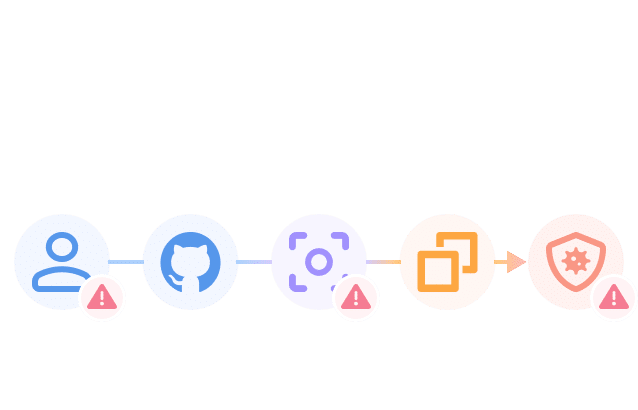
Upwind protects your workloads through continuous monitoring of network activity, file access and process execution, and real-time threat detection and response.
Trusted by leading enterprises around the world
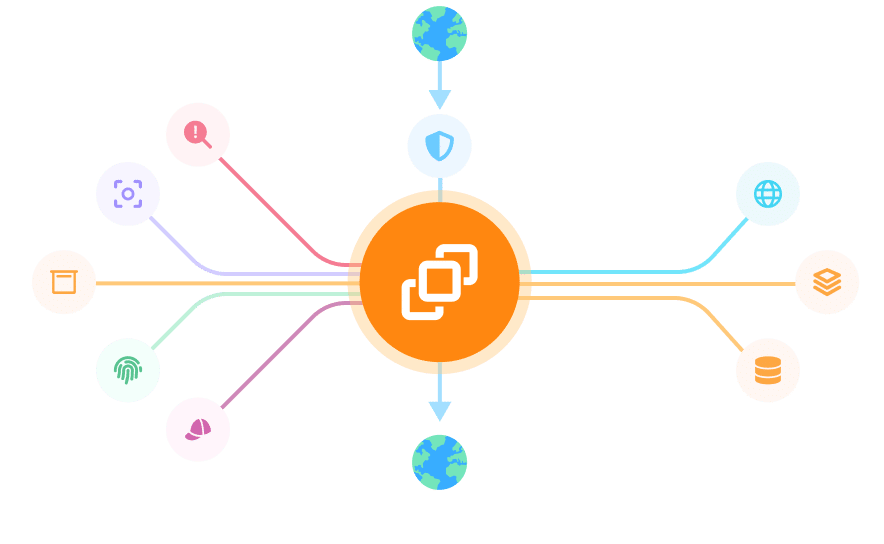
End-to-End Visibility of Cloud Workloads, Network Topologies, and Dependencies
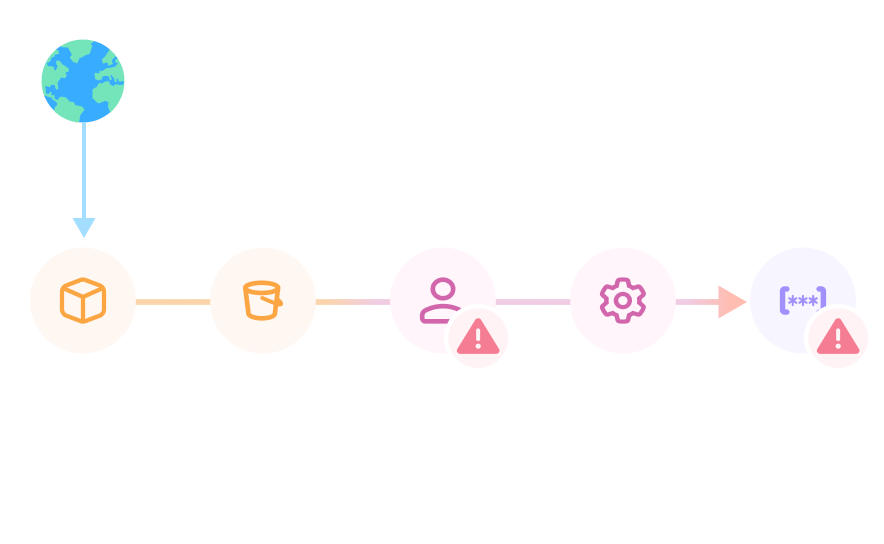
Untangle Cloud Rich Topologies
Gain deep visibility into your cloud network traffic. Map all workload-to-workload connections, services, and APIs in real time to understand how your containers and hosts communicate. Identify unusual flows, hidden dependencies, and misconfigurations that could introduce risk.
Discover APIs & Data in Motion
Continuously discover shadow APIs, sensitive data exposure, and unauthorized endpoints. Track sensitive data in transit, monitor API calls, and uncover exposed endpoints to reduce your attack surface. Proactively secure data in motion before attackers exploit weak points.
Track Process & File Access Baselines
Establish a baseline of process and file activity across containers and hosts. Monitor deviations such as unauthorized file access, abnormal process launches, or privilege escalation attempts. Quickly identify indicators of compromise by correlating file and process behavior with workload context and MITRE ATT&CK tactics.
Streamline Response to Threats
Respond in real time to threat activity, unexpected network flows, privilege escalations, or malicious process executions. Automatically stop attacks in progress by terminating processes, isolating identities or permissions, and blocking specific network requests to immediately contain security incidents.
Discover how organizations secure critical workloads with Upwind
Upwind helps us eliminate alert fatigue by providing us with information that is relevant and actionable in real-time.

Upwind’s ability to deeply prioritize risks and focus on what is critical has empowered our team with 7x faster time to remediation.

Upwind Threat Stories has drastically reduced triage and investigation time by correlating runtime detections with audit logs and giving us end-to-end visibility. Understanding who did what, how, and when, at a single glance has been a major game-changer.

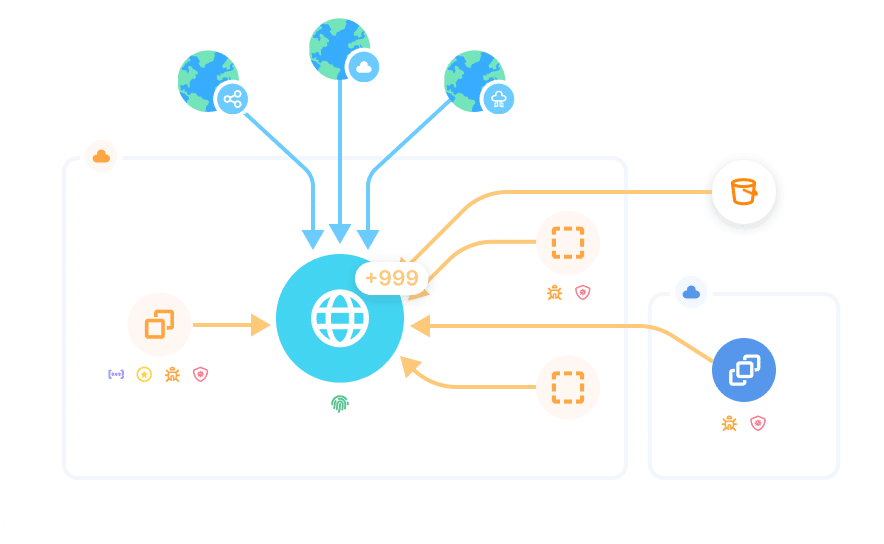
Continuous Protection and Security Context Across Hosts, Containers & Functions
Upwind gives you complete visibility and protection for your cloud workloads. View network topology in real time, receive contextual baselines based on workload behavior and respond to threats in real-time to protect all of your running workloads.
Discover & Secure Workloads in Real Time
7x Faster Remediation
Correlated Telemetry for 10x Faster Investigations
Secure Hosts, Containers, VMs, Serverless Functions & APIs with Upwind
See how Upwind protects your workloads through continuous monitoring of network activity, file access and process execution, and real-time threat detection and response.