The AI Threat Landscape Demands a New Cloud Security Model
This week, the Shai-Hulud npm campaign showed how quickly a compromised package can move through the software supply chain, jumping across trusted dependencies and reaching build pipelines before many teams even knew what they were looking at. But this is not just an npm story, and it is not just a story about one campaign.
It is part of a larger shift. Attackers are using automation, AI, and trusted software relationships to move faster than static security workflows were designed to handle.
The result is a widening gap between when risk appears and when defenders can detect, validate, prioritize, and remediate it.
The pattern behind the threat landscape
Across the first part of 2026, the incidents have looked different on the surface. Compromised npm and PyPI packages, weaponized CI/CD workflows, n8n vulnerabilities, AI tool compromise, and automated exploitation against GitHub Actions.
But underneath those incidents, the same pattern keeps showing up.
First, software supply chain risk is no longer a separate category. It is part of the cloud attack surface. Package registries, CI/CD pipelines, workflow automation platforms, security tooling, and third-party SaaS integrations now shape how attackers reach production environments. The dependency graph has become the multiplier. The weakest trusted node often becomes the entry point.
Second, AI has become both an infrastructure and an attack surface. Teams now rely on AI tools, LLM gateways, model infrastructure, and AI-connected workflows in production environments. Attackers are targeting those systems while also using AI to speed up reconnaissance, exploit development, phishing, and payload generation.
Third, automation, AI, and Agents have changed the tempo of attacks. Campaigns no longer depend on a human operator manually moving through every step. Bots can scan, target, exploit, and pivot across multiple environments at once.
These are not predictions. They are observations from the field. The gap between disclosure and exploitation used to be measured in months. Now, teams are watching it collapse into hours, and sometimes minutes.
Static security was built for a slower attacker
Many cloud security programs still rely on operating models that assume attackers have friction.
Daily scans. Weekly signature updates. Queue-based alert triage. CVSS-driven prioritization. Remediation is planned for the next sprint. We are shifting from the age of priority and labor into the workforce and agency; the side with more agency and workforce will have the upper hand.
Those workflows made more sense when exploit development took weeks or months, and when defenders had time to assess risk before it reached production traffic. That assumption no longer holds.
A 24-hour scan cycle cannot keep up with a campaign that moves through the dependency graph in a few hours. A static severity score cannot tell you which vulnerable package is actually running, exposed, reachable, and connected to sensitive systems today. A ticket queue cannot close the gap when automated exploitation is already moving at machine speed.
Defenders need a new approach to close the pace gap
Security teams need workflows that can move from signal to action much faster.
That means detection that can triage itself with live environment context. It means investigations that assemble evidence in minutes, not hours. It means exploitability validated against what is actually running, not assumed from a static score. It means remediation that connects back to the code, configuration, workload, identity, or pipeline that created the risk.
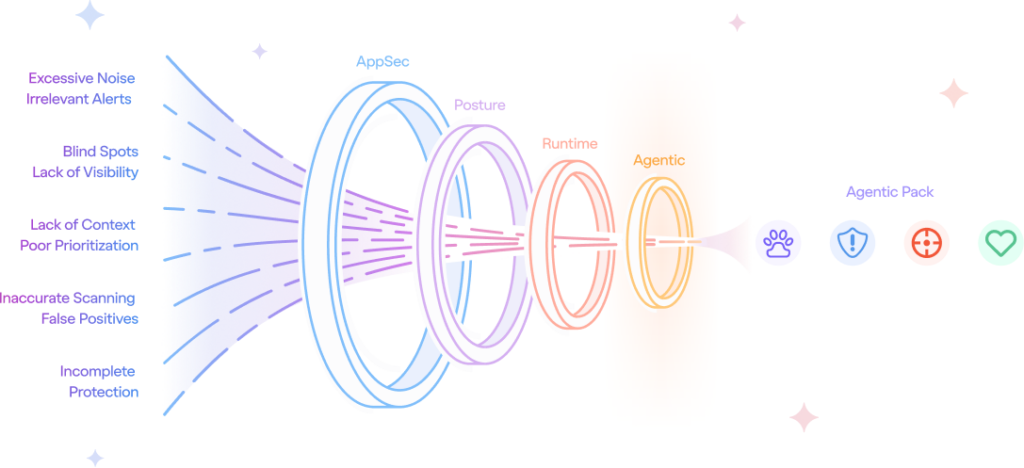
This is where agentic cloud security becomes necessary. Not as a generic AI assistant, but as a set of purpose-built agents that can take real steps inside the security workflow with the right context, controls, and human oversight.
What we built
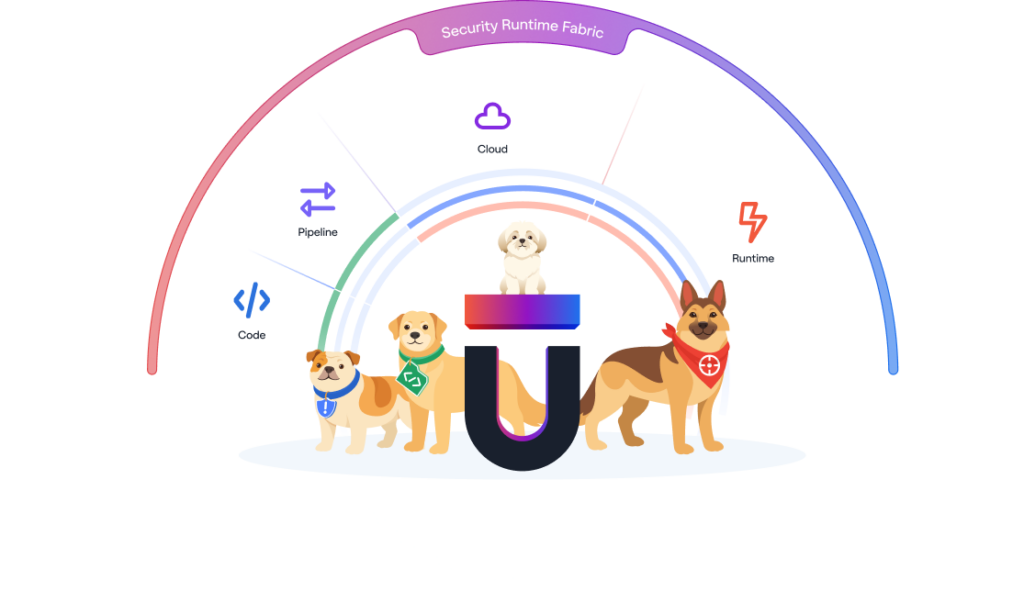
The Upwind Agentic Pack was built for this new pace of cloud security.
It brings AI agents into the Upwind Cloud and AI Security Platform to help teams investigate threats, validate exploitability, and remediate risk across cloud environments. The agents work with context across code, runtime, identity, infrastructure, vulnerabilities, APIs, and workloads, so teams can move from finding to action faster and with more confidence.
Priority is dead
The campaigns will keep getting faster. The software supply chain will keep multiplying its impact. AI-connected infrastructure will keep expanding the attack surface. The window between disclosure and exploitation will keep shrinking.
Attackers are not waiting for the next scan cycle, the next sprint, or the next dashboard review.
Cloud security needs prioritization that moves with the environment. That means understanding what is running, what is exposed, what is reachable, what changed, and what can be acted on now across code, cloud, and AI.
That is the shift we’re building to support.





