Introducing Upwind Data Security: Bringing Sensitive Data Risk Into Cloud Security Context
As cloud environments expand, so does the volume of sensitive data stored within them. For security teams, it is no longer enough to know whether a bucket is public or a workload is vulnerable. They also need visibility into a more fundamental question: what sensitive data exists across their cloud assets, and how does its presence change risk in context?
That is the purpose of Upwind’s Data Security (Data Security Posture Management) capability.
With Data Security, Upwind extends cloud security beyond infrastructure and workloads to include data at rest. It helps teams understand where sensitive data is stored, what type of data it is, and how that data should influence the overall risk profile of each resource.
Why Data Security Matters
Most organizations already have broad visibility into infrastructure risk. They can find exposed resources, vulnerable assets, or suspicious runtime behavior. But sensitive data often remains a blind spot.
A storage resource may look operationally healthy, yet still contain:
- customer records
- payment details
- health information
- secrets or credentials
- internal configuration files
Without data-aware context, security teams may struggle to prioritize the resources that matter most.
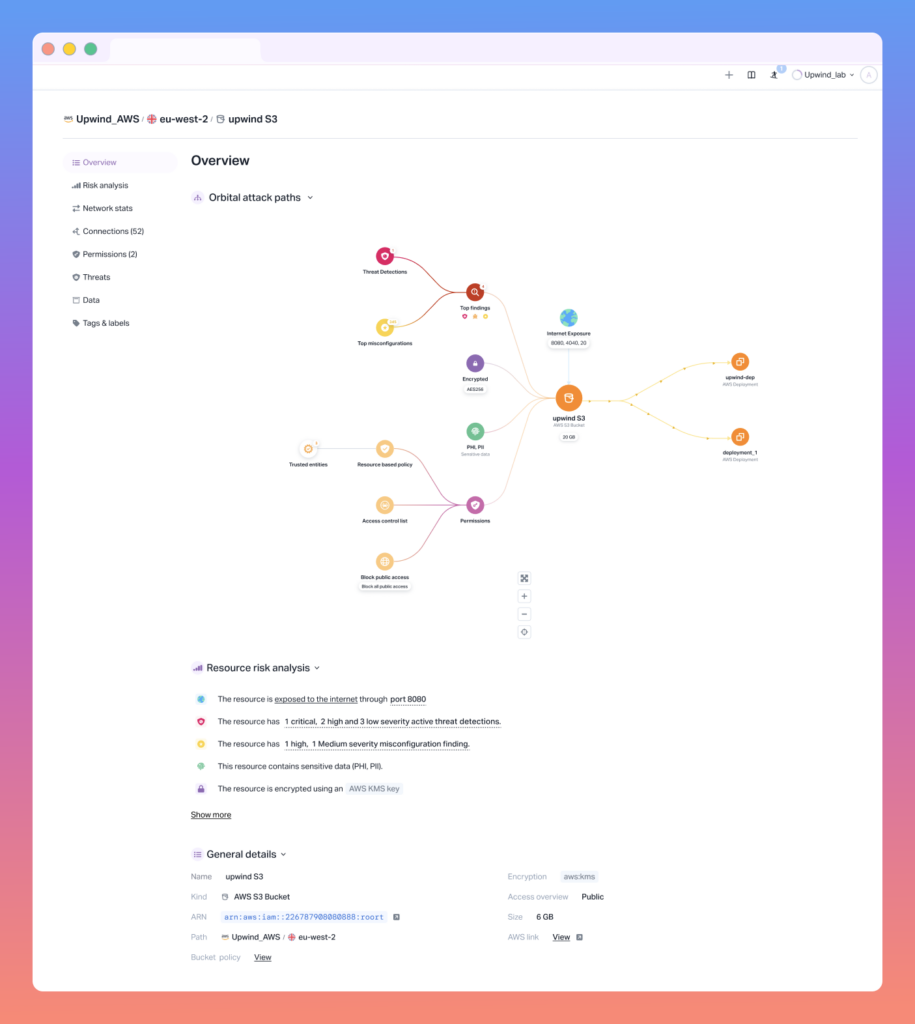
Upwind Data Security is designed to close that gap by surfacing sensitive data presence as a core risk signal, directly on the resource itself. That means teams can evaluate cloud assets not only by exposure and misconfiguration, but also by the actual business sensitivity of the data they hold.
Starting With the Storage Assets That Matter Most
Amazon S3 Buckets
S3 buckets will be scanned using the Upwind Cloud Scanner. Customers will be able to scope which buckets are included using tag-based include and exclude filters, making it easier to focus on the assets that matter most.
Each object in a bucket will be evaluated based on predefined scanning parameters such as:
- object size
- number of objects
- sample rate
This allows scanning to stay efficient even in large-scale environments.
Amazon EBS Volumes
For Amazon EBS, scanning is be performed out-of-band through snapshots, when snapshots are available. In this phase, scanning will focus only on supported file systems and mountable volumes.
Sensitive Data Detection That Becomes a Resource Risk Signal
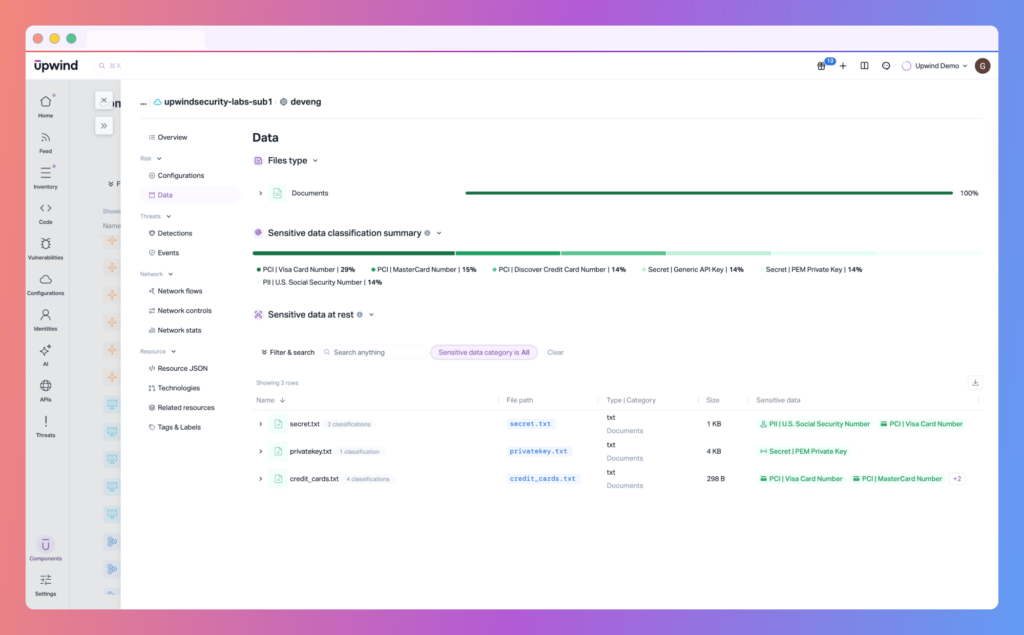
- PII such as email addresses and other personally identifiable information
- PCI such as payment card information
- PHI such as protected health information
For every match, Upwind will record:
- the type of sensitive data detected
- the specific location where it was found
- supporting evidence tied to the file or object
This information is then reflected as a risk indication on the resource itself, even when there is no formal policy violation attached.
That matters because it changes how teams prioritize. A publicly exposed bucket is risky. A publicly exposed bucket that also contains customer PII is much riskier.
Data at Rest vs. Data in Transit
Upwind already helps customers detect sensitive data moving through APIs. Data Security expands that visibility to stored data.
To make that distinction clear, the platform separates these two categories:
- In Transit: sensitive data flowing through APIs, detected by API scanning
- At Rest: sensitive data stored in files, buckets, or volumes, detected by Data Security scanning
This makes reporting and investigation much clearer. Security teams can quickly understand whether the issue is tied to data flow, data storage, or both.
Turning Data Exposure Into Actionable Findings
Data Security findings will appear in the Configurations module under a dedicated Data framework.
For every scanned asset, the platform can generate findings when sensitive or risky data is detected. These findings are designed to be actionable, not just informational.
Each finding can include:
- a finding ID and related policy context
- the affected resource, such as an S3 bucket or EBS volume
- the relevant file path, object key, or file type
- the type of data detected, such as email addresses, secrets, or credentials
- a severity score based on both classification and exposure context
- evidence such as snippets, sample patterns, or metadata for validation
This gives security teams what they need to investigate faster and validate the issue before escalating it.
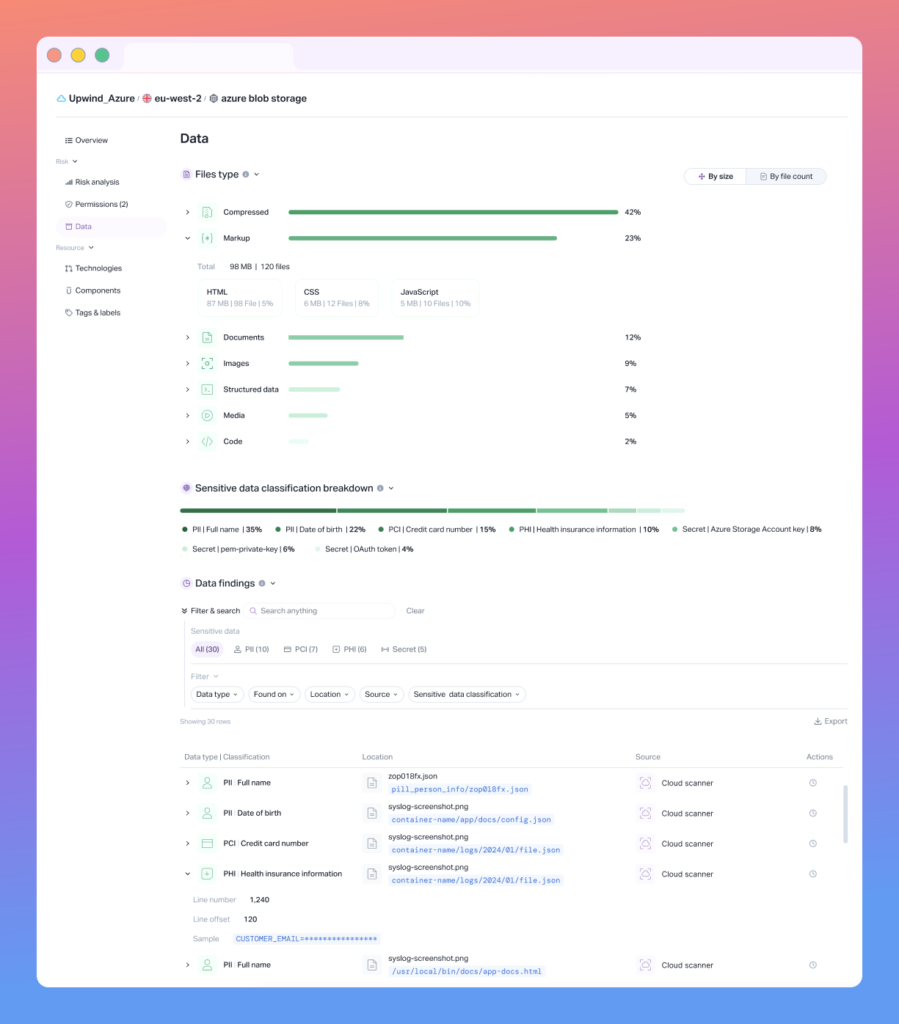
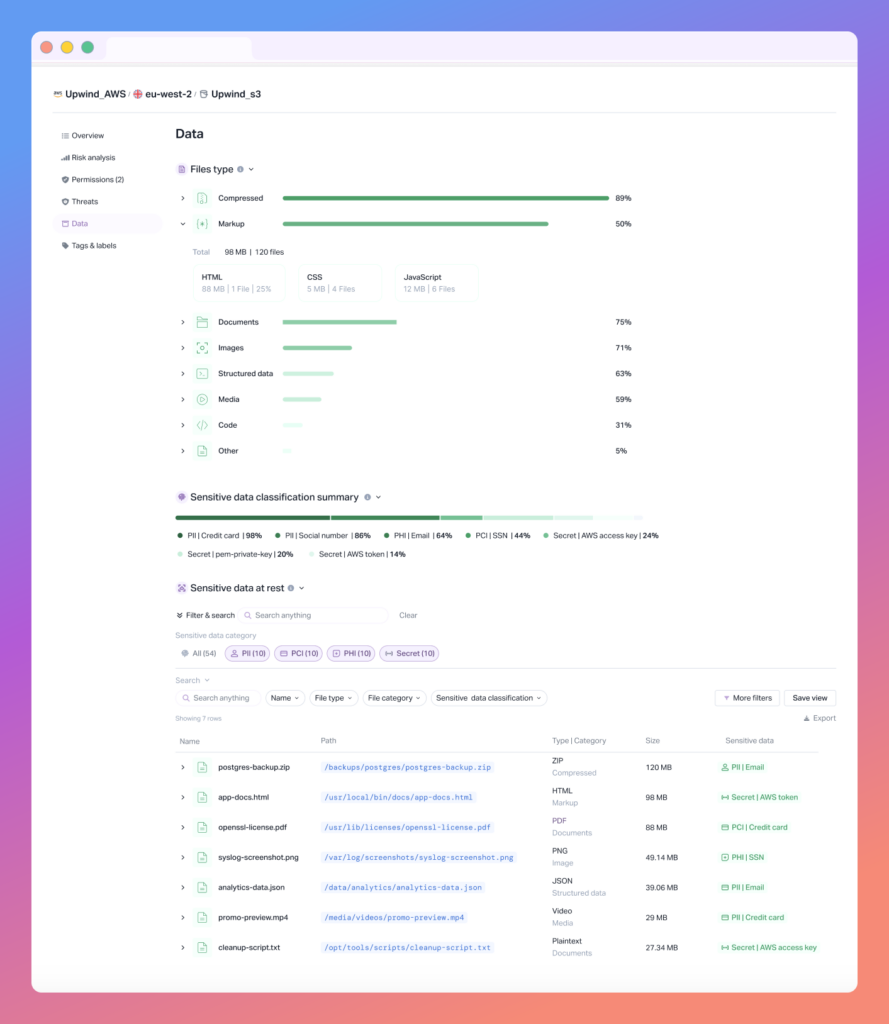
A New Data Tab in Resource Overview
To make Data Security part of the everyday investigation workflow, scanned resources include a dedicated Data tab in the Resource Overview.
This tab will give users a focused place to understand the data profile of a resource, including:
- aggregated scan results
- risk indication tied to sensitive data presence
- file type cataloging for the scanned asset
- filtering and sorting by file type, size, and severity
Instead of looking at data security in isolation, teams will be able to review Data Security results in the same place they already investigate runtime, vulnerability, and exposure issues.
File Type Cataloging for Better Visibility and Triage
As part of scanning, Upwind will automatically identify and categorize the types of files present in each scanned asset.
This file type catalog will appear within the new Data tab and help teams answer practical questions such as:
- Which resources contain PDFs or spreadsheets?
- Where are configuration files concentrated?
- Which assets contain keys, certificates, archives, or database files?
- Which file types are most commonly associated with sensitive findings?
More Granular Control Over What Gets Scanned
Data Security is not just about detection. It is also about operational control.
As part of the Cloud Scanners Configuration experience, users will be able to enable Data Security scanning per supported asset type and define scope using tag-based rules.
They will also be able to fine-tune scan behavior using advanced parameters at the global level, helping them balance coverage, performance, and noise reduction.
Over time, the goal is to support even more granular control directly from the resource itself, including:
- per-bucket overrides of global settings
- disabling scanning for individual buckets
- custom scan scopes for specific buckets, such as excluded paths or folders
This makes Data Security easier to operationalize in real-world environments where not every storage asset should be treated the same way.
Why This Matters for Security Teams
What makes Data Security powerful is not just that it detects sensitive data. It is that it places that data into the full cloud security context Upwind already provides.
A bucket with PII is not just a storage resource. It is a business-critical risk.
A volume with secrets is not just an asset. It is a potential blast-radius multiplier.
A file catalog is not just inventory. It is a way to understand where the most sensitive content lives and how it should be protected.
By connecting data sensitivity, resource exposure, and platform-wide context, Upwind helps teams move from raw detection to practical prioritization.
See It It In Action
Upwind Data Security brings data security into the same platform context as cloud exposure, vulnerabilities, runtime behavior, and configuration risk. Instead of treating sensitive data as a separate workflow, it makes data awareness part of how teams assess and prioritize cloud risk every day.
If you’d like to see how this feature fits into your environment – or to explore how Upwind can help you prioritize and remediate risk more effectively – schedule a customized demo with us. We’ll walk through your use cases, integrations, and security goals to show how Upwind delivers actionable cloud security at scale.