When a Supply Chain Compromise Happens, Defenders Deserve More Than Starting From Zero
Notes on the Vercel / Context.ai OAuth incident, and how Upwind stands with its community through moments like these.
On April 19, Vercel disclosed a security incident stemming from a compromise of a third-party AI tool, Context.ai, whose Google Workspace OAuth application was abused by an attacker. A Vercel employee signed into Context.ai using their corporate Google account, and when Context.ai’s OAuth tokens were taken over, the attacker was able to pivot into Vercel’s environment and access environment variables that had not been marked as sensitive. Vercel has been transparent, is working with Mandiant and law enforcement, and has shared indicators of compromise to help the broader community investigate their own exposure.
These weeks are genuinely hard on everyone involved. The engineers, responders, and communicators at Vercel and Context.ai are doing difficult work in public, on a short clock, and they have our respect. Supply chain compromises are a shared problem across our industry, and every defender we have spoken with since the disclosure has asked a version of the same question: what do I need to do right now, and how do I know I have covered everything?
What follows is a practical look at how security teams can avoid starting from scratch at the most difficult possible moment, using threat context, exposure visibility, behavioral detections, and runtime evidence to scope response faster.
Before the News Breaks: MDR Helps Teams Start With Context
Upwind’s Managed Detection and Response team monitors threat intelligence around the clock. When a disclosure like this one lands, customers do not have to wait until someone reads the news and raises a ticket. Our analysts reach into shared Slack channels with the context that actually matters: what happened, which indicators of compromise to watch for, and a preliminary read on whether the incident is relevant to their environment.
Human expertise, applied early, is what turns a 3 a.m. pager into a calm conversation.
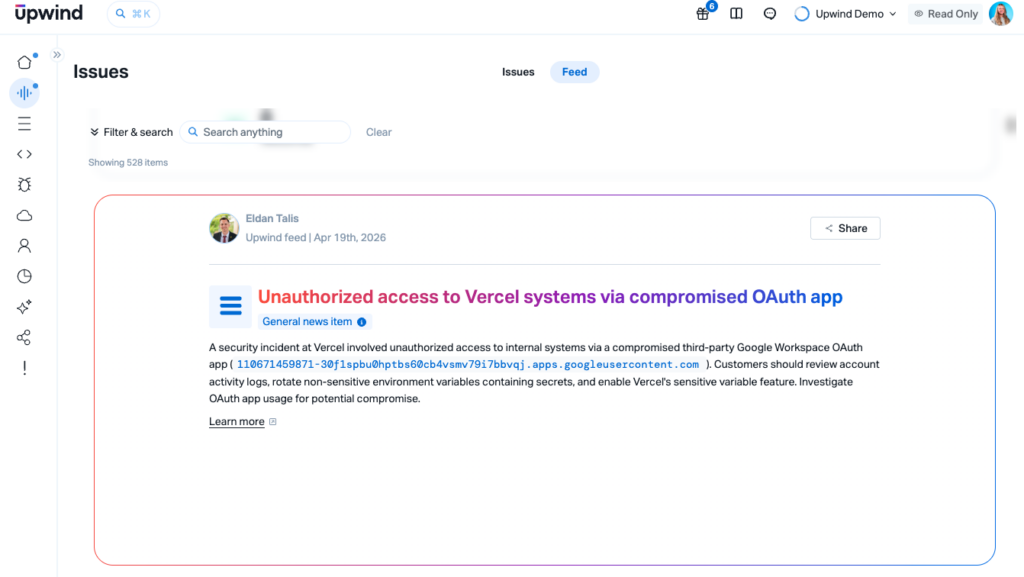
The Threats Feed Gives Defenders the Details in One Place
Following Vercel’s bulletin, Upwind’s Threats Feed surfaced the incident in the Issues view for customers. The feed includes the specific OAuth application ID Vercel disclosed (110671459871-30f1spbu0hptbs60cb4vsmv79i7bbvqj.apps.googleusercontent.com), recommended remediation steps, and a continuously updated thread as new technical details emerge. Defenders do not have to stitch together a timeline from news articles, vendor advisories, and DMs. The feed becomes the thread.
Once teams understand the disclosure, the next question is whether the relevant exposure exists in their own environment.
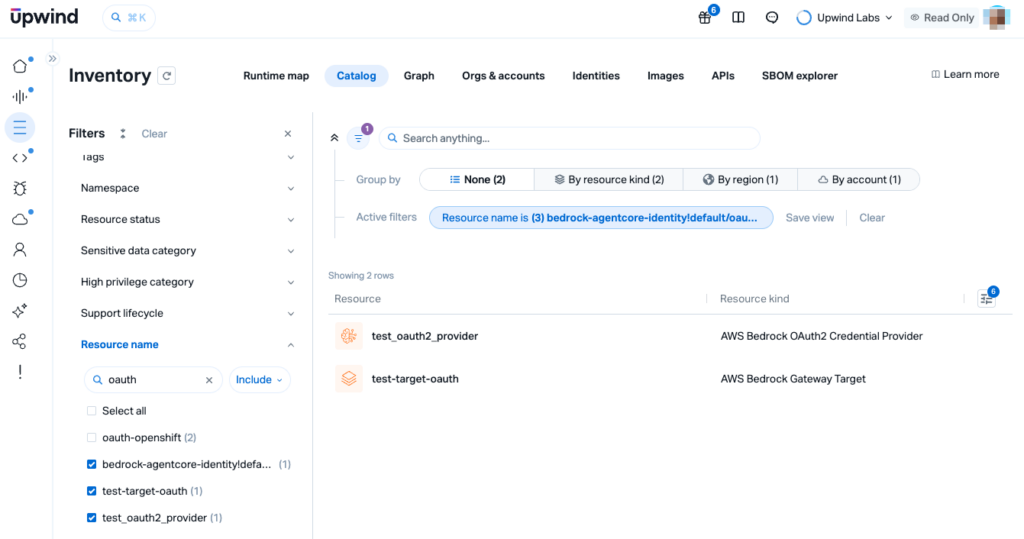
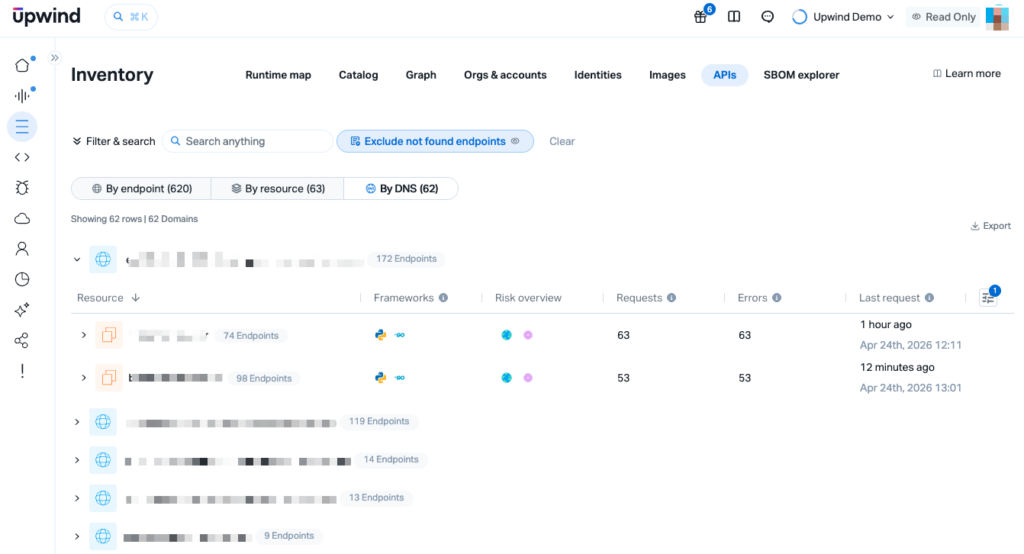
Inventory Answers the Exposure Question in Seconds
With agentless coverage already in place, the first stop for the question on everyone’s mind, “where is this in my environment?”, is Inventory → Catalog. A filter on OAuth-related resources surfaces all relevant assets across all cloud accounts and regions in a single view: resource name, account, resource kind, and region. No scripting, no per-account walk, no waiting on a sensor rollout. Just an immediate, auditable answer to the exposure question.
If exposure exists, responders need to know whether that access was used to assume roles, enumerate secrets, or retrieve sensitive parameters.
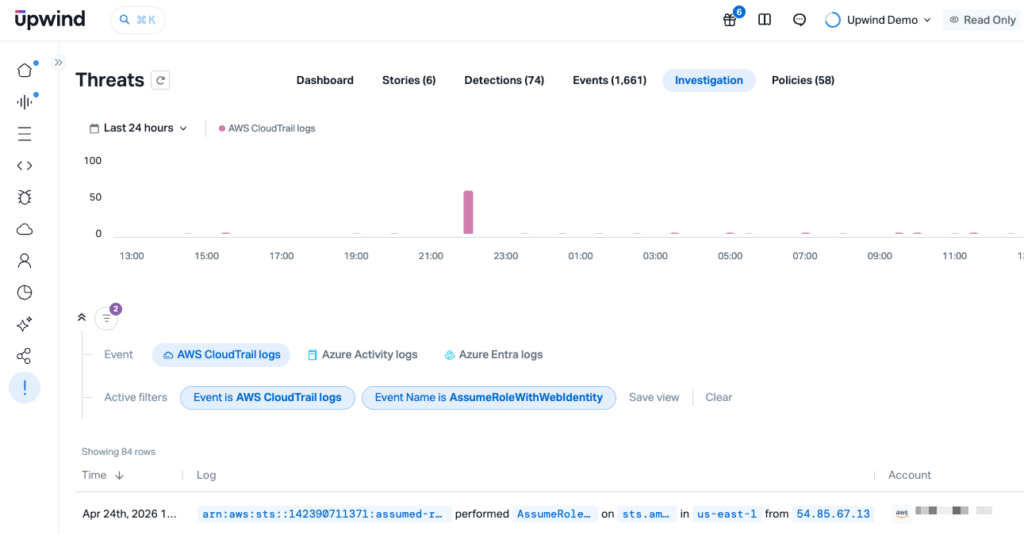
CloudTrail Correlations Detect Credential and Secret Harvesting
If an attacker has already gained a foothold, the behavior that typically follows is well characterized. Upwind correlates CloudTrail events to detect the harvesting patterns this class of attack may rely on:
- AssumeRoleWithWebIdentity — OAuth-based role assumption, directly relevant to this attack chain.
- GetSecretValue / ListSecrets — Secrets Manager enumeration.
- GetParameter / GetParameters / DescribeParameters — SSM Parameter Store access.
- Environment-variable reads in Lambda — targeting credentials stored at the function level.
These detections do not depend on knowing the specific threat actor or campaign. They fire on the behavior that any attacker with OAuth-grade access is likely to attempt.
Inventory helps teams understand exposure. Runtime telemetry helps them understand active behavior.
Runtime Sensors Help Answer the Hardest Question: Is Anything Actively Talking to the Threat?
For customers running the Upwind runtime sensor, we can go a step further. Because the Threats Feed already knows the compromised OAuth application identifiers, Upwind can map them against DNS resolutions and network connections from workloads in real time. A query for the specific OAuth App ID, or for related compromised infrastructure, answers the question that keeps responders up at night: is something in my environment actively trying to reach attacker infrastructure right now?
That is the line between inventory awareness and live threat detection, and it can be the difference between a well-scoped response and a multi-week forensic engagement.
The Bigger Picture
Incidents like this will keep happening. OAuth sprawl, third-party AI tools with broad read access, long-lived platform secrets, and environment-variable models that default to non-sensitive are patterns the entire industry is still working through. No single vendor solves this alone, and we have genuine respect for the teams at Vercel, Context.ai, Mandiant, and every responder’s desk who are working this one on short sleep.
The only way to fight supply chain attacks is with runtime security. When the next disclosure breaks, teams do not have to start from zero. The threat feed brings the context together. MDR helps triage what matters. Inventory helps answer the exposure question. And when runtime telemetry is enabled, Upwind helps teams detect suspicious activity in live workloads.
If you are working on this incident and want another set of eyes, we are here. That is what being part of a security community means to us.