Secure Data Across Cloud Environments
Trusted by hundreds of enterprises around the world
Discover and Secure Data Access at Scale



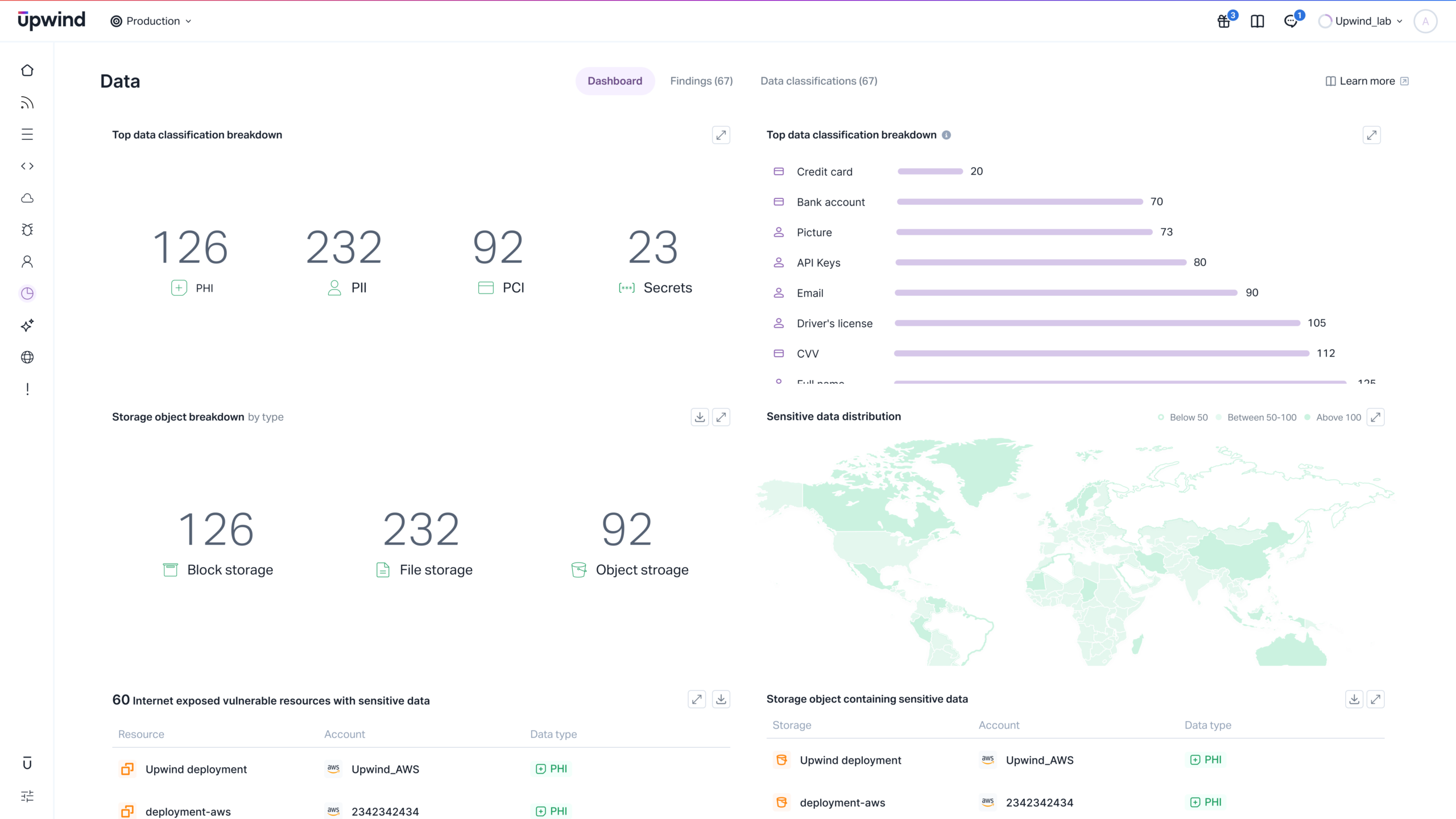
Discover & Classify Sensitive Data
- Automatically find sensitive data everywhere
Scan cloud workloads, storage, databases, and file systems for PII, PCI, PHI, and secrets.
- Runtime-aware data classification
Understand how sensitive data is accessed and used across services.
- Answer “where does my sensitive data live?”
Gain complete inventory of data assets — structured and unstructured.
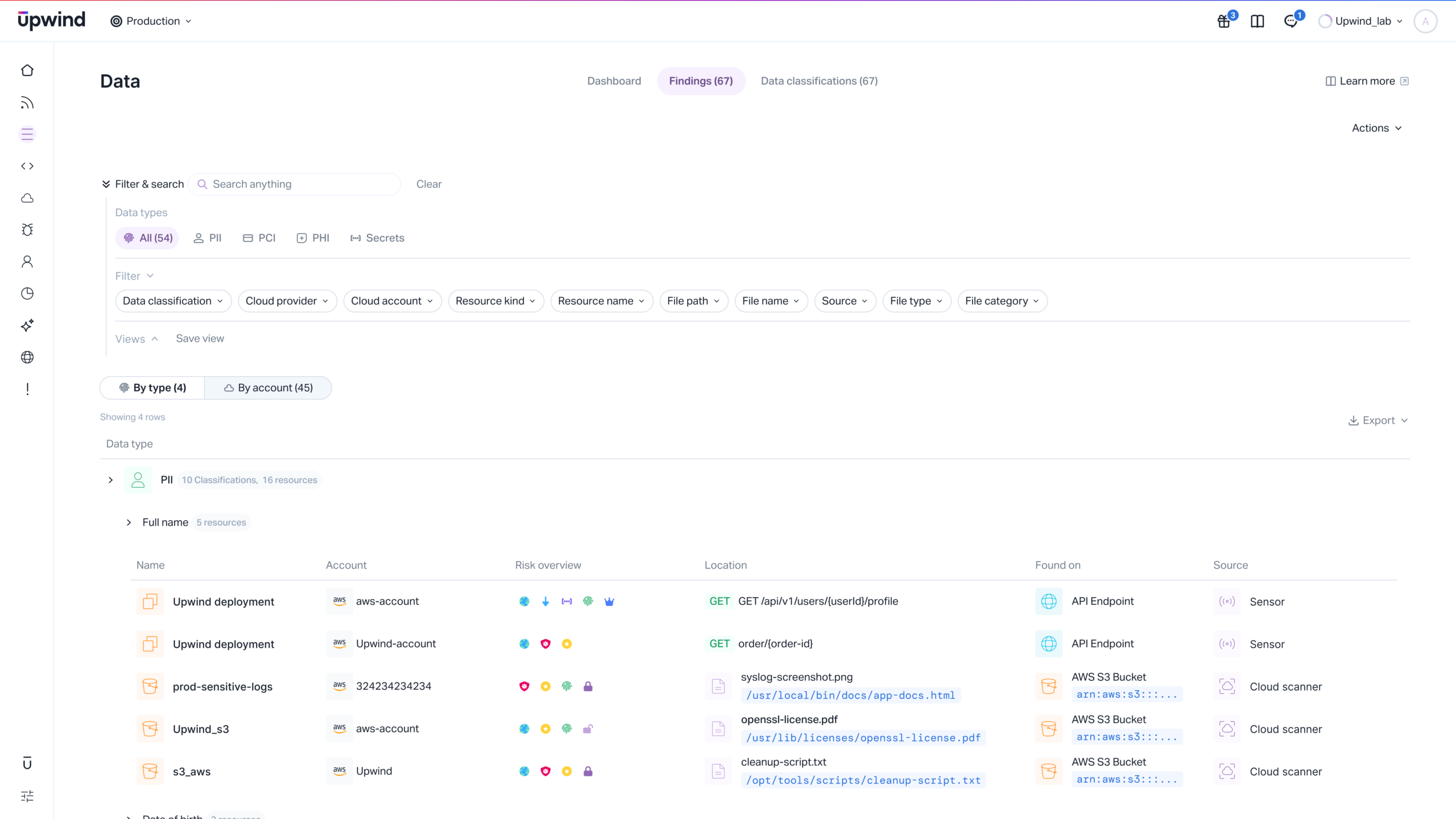
Find Cloud Risks with Data Context
- Prioritize what’s truly exploitable
Correlate data exposure with network paths, identity access, and vulnerabilities.
- Shrink data blast radius
Surface risky access relationships between data stores and external entities.
- Stop theoretical alerts
Remediate based on what attackers can actually reach — not what scanners guess.
Catalog & Map Data Across Your Environment
- Continuous cloud data catalog
Automatically index all data assets and their sensitivity levels.
- Map data lineage and flows
Visualize where data goes — app to app, cloud to cloud, internal to external.
- Eliminate shadow data
Detect unmanaged or unknown datasets before they become security liabilities.
Protect Data at Rest & In Motion
- Block unauthorized access
Detect and prevent attempts to reach sensitive data through risky channels.
- Inspect traffic targeting data stores
Identify exploitation attempts using real-time Layer 7 analytics.
- Safeguard data wherever it moves
Maintain protection during transmission across workloads and clouds.
Achieve Data Compliance at Scale
- Automate data compliance monitoring
Continuously validate controls for PCI, HIPAA, GDPR, HITRUST, and more.
- Generate audit-ready reporting
Produce compliance evidence enriched with runtime validation.
- Reduce audit fatigue
Streamline compliance with always-up-to-date data posture insights.