Upwind’s Runtime-Powered Threat Detection
As organizations move to the cloud and put their mission-critical applications and most sensitive information in the cloud, adversaries target it and are using AI to compromise companies in hours, making the issue of threats and attempted cloud attacks a question of “when” not “if.” IBM’s Cost of a Data Breach Report in 2022 showed that 45 percent of breaches in 2021 were cloud-based, with the average cost of a data breach in the U.S. costing $9.44 million. For security teams, attacks and breaches often feel unavoidable, especially as cloud runtime attack surfaces increase, making them an easier target for bad actors.
45 percent of breaches in 2021 were cloud-based, with the average cost of a data breach in the U.S. costing $9.44 million
IBM’s 2022 Cost of a Data Breach Report
Real-time Detection & Immediate Response
To do so, organizations need complete cloud visibility and understanding of what their cloud infrastructure and applications are actually doing at runtime, in order to immediately recognize threats and abnormal behavior in their environment. Those added layers of protection have a direct ROI – IBM’s report also found that companies who employed security automation saved an average of $3.05 million, making a clear case for security teams to employ security solutions for faster threat responses.
Increasingly advanced threat actors and expanding attack surfaces across cloud environments make identifying and stopping threats difficult for security teams, resulting in time-intensive threat hunts that can take days to get to the root cause. In the case of a breach, every wasted minute results in a higher cost of breach, making the need to rapidly identify and respond to threats a top priority for organizations.
Types of Cloud Threats
There are countless ways that threat actors can carry out cloud attacks, and organizations need to be aware of the most common possibilities in order to adequately protect against them.
Malware
Short for malicious software, malware is used to describe software that is designed by threat actors to steal data or cause damage to cloud infrastructure. Common malware attacks in cloud computing include:
- Comand & Control- a bad actor attempts to communicate with and control an infected machine or network.
- Spam – a bad actor takes control of an EC2 instance to communicate with a remote host on port 25 with the intention of sending out spam in mail servers.
- Cryptoming – a bad actor takes control of cloud resources to mine cryptocurrencies
- Brute Force – an attacker uses trial and error to crack passwords, login credentials and encryption keys, called brute force because of often aggressive means to crack codes including several hundred attempts per second.
- Drive-by-Download – malicious code often downloaded by visiting an infected website that exposes users to different types of threats, allowing bad actors to steal or collect information, inject Trojans or introduce other malwares.
- Phishing – an attacker impersonates someone or creates a malicious domain that impersonates an institution, causing an authorized user to reveal sensitive information.

Malicious Network Attacks
Malicious network attacks occur when a bad actor gains access to a network, elevating their privileges in order to commit malicious behaviors such as accessing sensitive data. Examples of malicious network attacks include:
- Denial-of-Service (DoS) – a malicious actor using a single computer attempts to make a virtual machine unavailable to its intended users by disrupting its normal functions, usually by overwhelming or flooding it with requests until normal traffic can’t be processed. This can happen in a cloud environment when an EC2 instance begins generating a large amount of DNS, UDP or TCP traffic, signaling the environment might be attempting to conduct a DoS attack using DNS, UDP or TCP protocols.
- Distributed Denial-of-Service – a type of DoS attack that is launched from distributed sources, rather than a single computer, using the methods listed above.
- Port Scan – a malicious actor scans your ports to identify any vulnerabilities that can be exploited.
- Port Probe – when an EC2 instance has an unprotected EMR-related port that is being probed by a known malicious host.
- Black Hole – when an EC2 instance is attempting to communicate with an IP address of a remote host that is a known black hole. A black hole is a place in the network where incoming or outgoing traffic is silently discarded without informing the source that the data didn’t reach its intended recipient.
Malicious Behavior
Malicious behavior usually refers to new port communication or unencrypted communication, signaling a new behavior that an environment has never performed before. Examples of malicious behaviors include:
- Unusual Network Port – when an EC2 instance is communicating with a remote host on an unusual server port that it has no history of communicating with.
- Unusual Traffic Volume – when an EC2 instance is generating unusually large amounts of network traffic to a remote host, with no history of sending this much traffic to this remote host.
- Unusual DNS Resolver – when an EC2 instance is communicating with an unusual public DNS resolver, with no history of communication with this DNS resolver.
- Unusual DNS over HTTPS (DoH) – when an EC2 instance is performing an unusual DoH communication, with no recent history of similar communication.
- Port Sweep – an EC2 instance probes a port on a large number of publicly routable IP addresses, which normally signals that it is scanning for vulnerable hosts to exploit.
- New Library is Loaded – a newly created or recently modified library is loaded by a process inside a container, which can indicate that a bad actor may have gained access to the container and has downloaded and executed malware as part of a compromise.
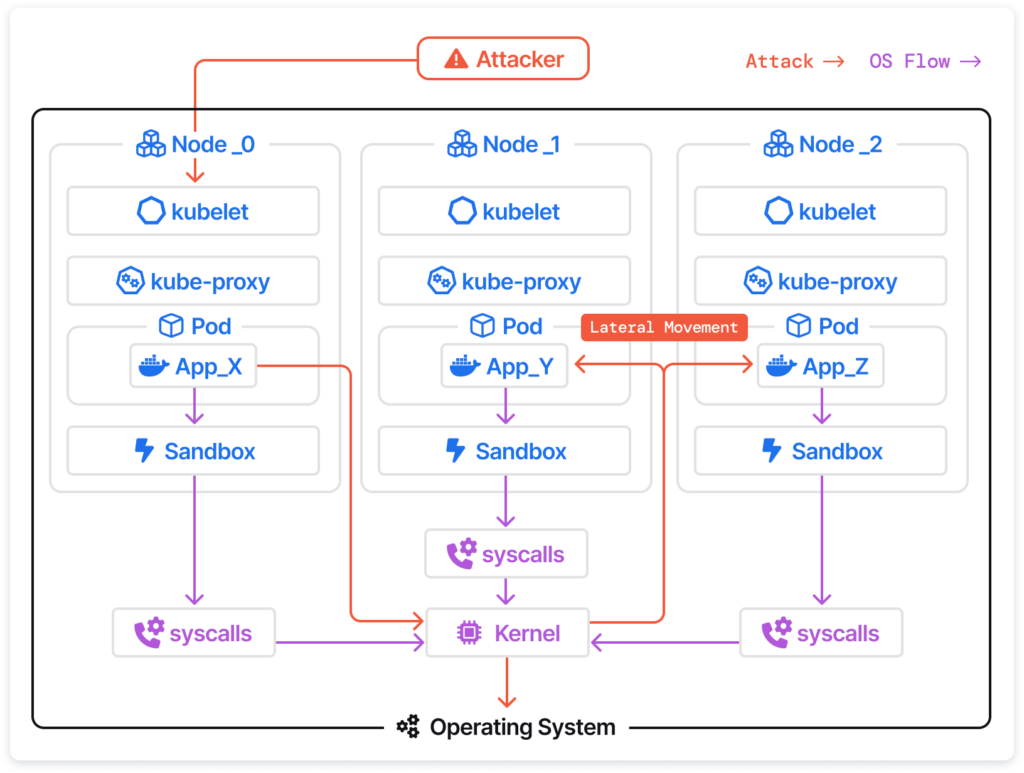
Lateral Movements & Privilege Escalations
Lateral movements and privilege escalations occur when a bad actor gains access to a network, elevating their privileges in order to commit malicious behaviors such as accessing sensitive data. These types of attacks include:
- Lateral Movements – a movement used by a bad actor to search an infected network for vulnerabilities, in order to escalate privileges and get to an ultimate target. It is called “lateral” because of the way attackers move sideways through an environment to search for a vulnerability to exploit. Pass the hash (PtH) attacks, pass the ticket (PtT) attacks, remote services exploitation, secure shell (SSH) hijacking and windows admin shares are all examples of common lateral movement attacks.
- Privilege Escalations – an attacker gains access to elevated rights, privileges, entitlements or permissions that go beyond what was assigned to an identity, account, user or machine. For example, an attacker with an iam:CreatePolicyVersion permission could create a new version of an IAM policy with custom permissions. When creating a new policy version, they could add a flag (–set-as-default) to create a new default policy version that does not require set policy versions. Using this escalation method, they could allow a user to get full administration access of an AWS account.
With the amount and complexity of cloud attacks only growing, organizations must be constantly vigilant in order to adequately protect their cloud environment from threat actors attempting to exploit their data or cause harm to their infrastructure.
One of the most effective ways to protect cloud infrastructure and applications from threat actors is to employ continuous detection and response solutions, allowing organizations to identify and respond to threats in real-time.
The Pillars of Proactive Threat Detection
In order to stay ahead of threats and bad actors, organizations must be able to see and understand everything that is happening in their cloud environment. This includes:
- Understanding Environmental Baselines: In order to proactively protect against threats, organizations need to understand what their environment normally looks like, and what constitutes normal behavior. Some of the aspects that must be considered are:
- Network Communication Baselines – Understand which ports usually talk to your environment, and which ports your environment normally talks to.
- Process Execution Baselines – Know which processes run in your cloud environment and what their normal execution looks like.
- Encryption Baseline – Know if your network tunnels are being sent as encrypted tunnels or unencrypted tunnels.
- Runtime Insights: In order to proactively detect threats and risks, you need real-time, runtime insights into what your infrastructure and applications are actually doing. The runtime aspect is critical, as threat actors use increasingly sophisticated attack methods that need to be detected the moment they occur.
- Deep Investigation: Effective threat detection also requires streamlined root cause analysis so that security teams can identify the root cause of threats in seconds, rather than days, and immediately respond to them.
- Immediate Response: Finally, security teams must be able to respond to threats in real-time, stopping them before they are able to cause significant damage. Without effective response options, security teams are left holding information about bad actors without the ability to actually stop them.
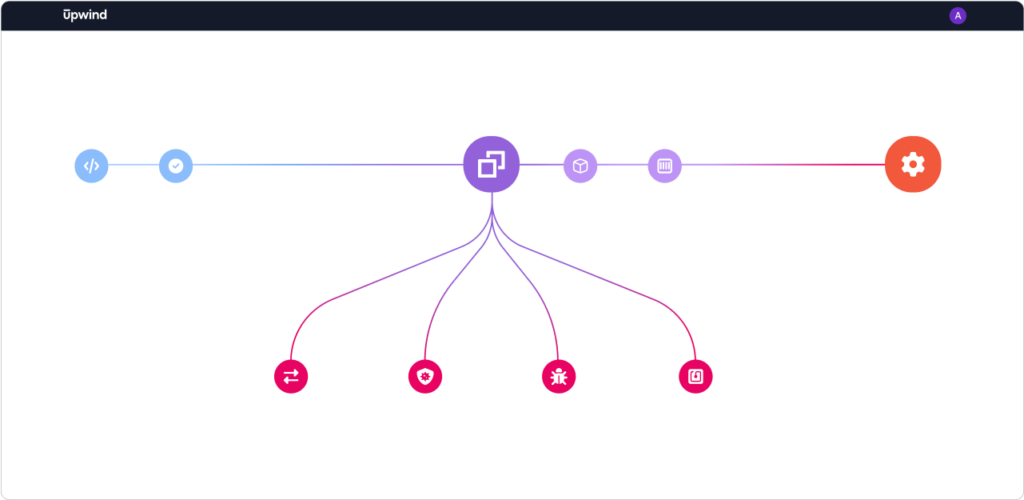
Upwind’s Runtime-Powered Threat Detection
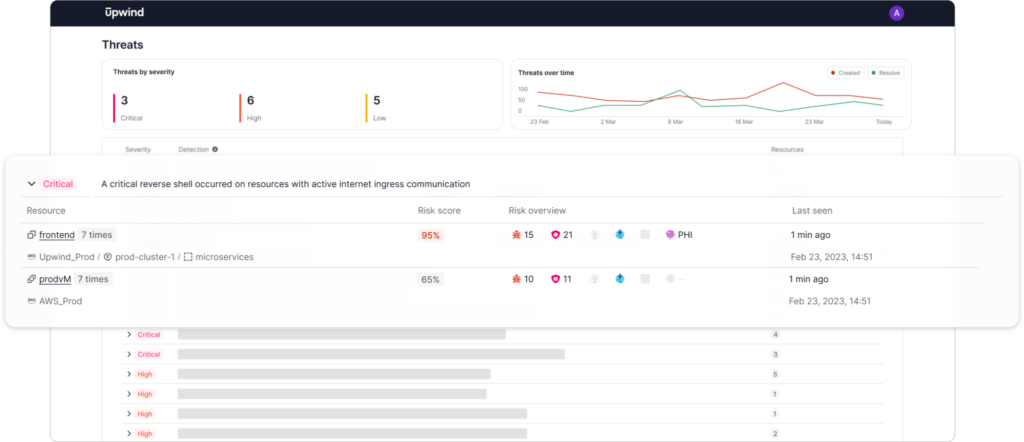
Upwind’s Runtime-Powered Threat Detection immediately identifies threats and bad actors with real-time, runtime insights, allowing security teams to identify, contextualize and respond to threats as soon as they occur.
Process Execution
Upwind monitors various activities related to executing code or commands in a system. This includes identifying malicious processes and behaviors and detecting network utilities, malware, crypto mining and other tools that attackers commonly use.
Network Activity
Upwind monitors network traffic for suspicious activities, such as Port Sweeps, DoS attacks, Spam, connections to black holes, sinkholes, Crypto or Tor networks and malicious IPs & domains.
Kubernetes Audit Logs
Upwind monitors Kubernetes API resources for suspicious activities, such as privilege escalation, lateral movement and data exfiltration.
File Activity
Upwind monitors file-related activities, such as file creation, modification and deletion. This is monitored for the detection of malicious behaviors, suspicious activities and unauthorized access.
Upwind’s Baseline Identification
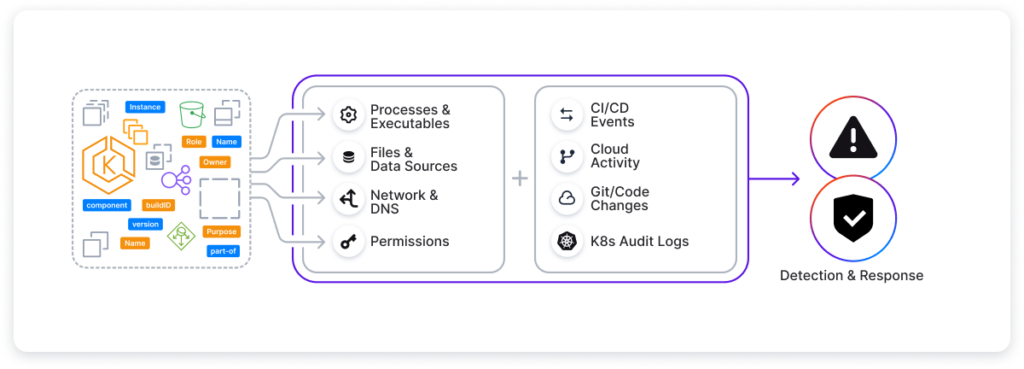
Upwind’s Threat Detection identifies and learns your environment’s Network Communication, Process Execution, and Encryption Baselines by employing multi-context anomaly detection from CI/CD events, Cloudtrail logs, Git/code changes, K8s logs and Azure activity logs. By understanding what your environment typically looks like and go beyond typically signature-based threat detection to also perform signature-less threat detection and identify any anomalies in your cloud environment.
Upwind’s Runtime Insights
One of the most important characteristics of Upwind’s Threat Detection is that it happens in real-time, using crucial runtime insights. We do this by using an eBPF-based agent for analysis of processes, files and networks, immediately identifying threats and bad actors as soon as they enter your environment. Our eBPF agent is run in the OS kernel space and is light-weight, runs in multi-cloud and multi-architecture environments and is easy to deploy and operate.
Many security tools use side-scanning techniques that provide updates hours or even days later, or employ heavy agents that weigh down your system and can cause performance degradation. Upwind takes a different approach, leveraging our lightweight eBPF agent to provide real-time, contextualized insights that allows you to understand what is happening in your cloud environment at any given moment.
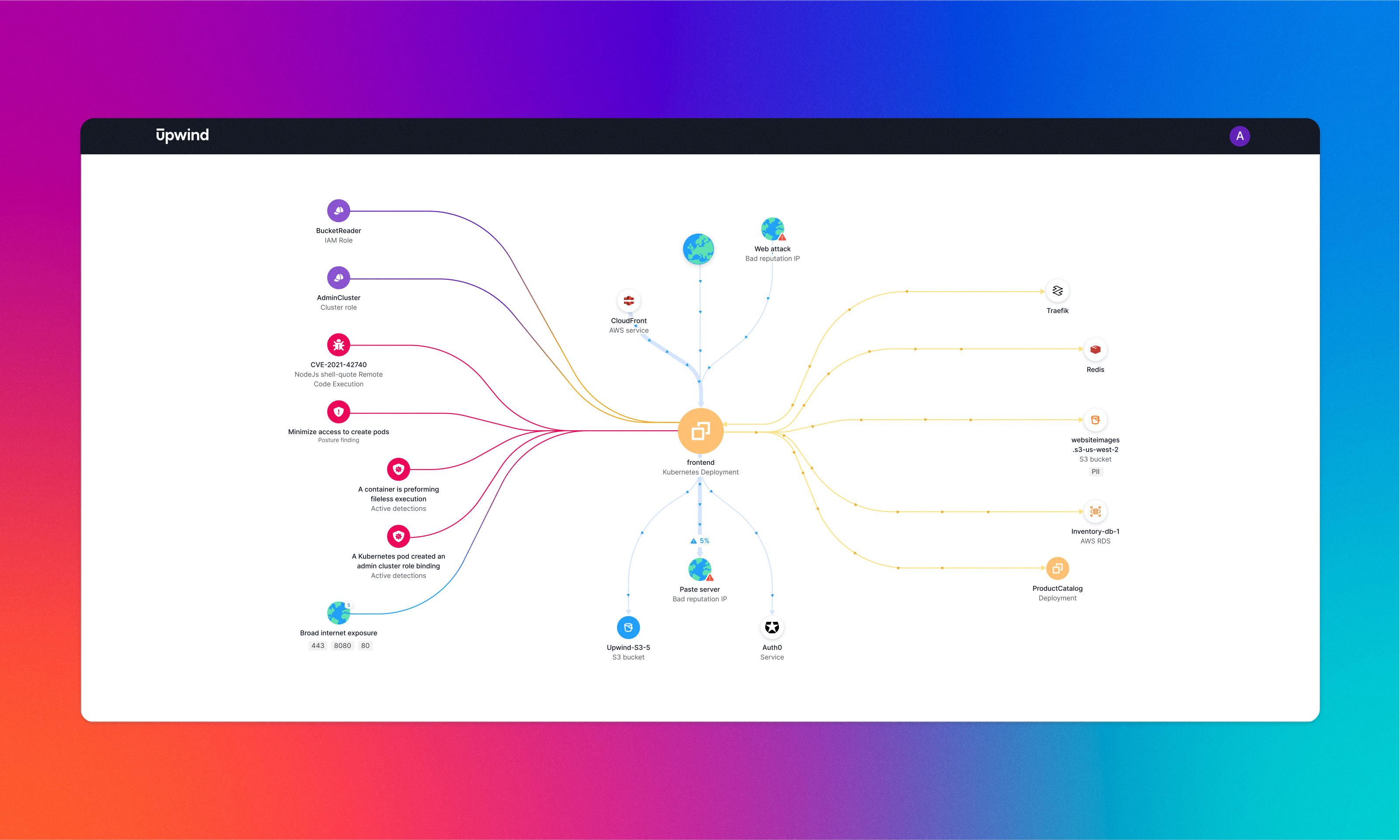
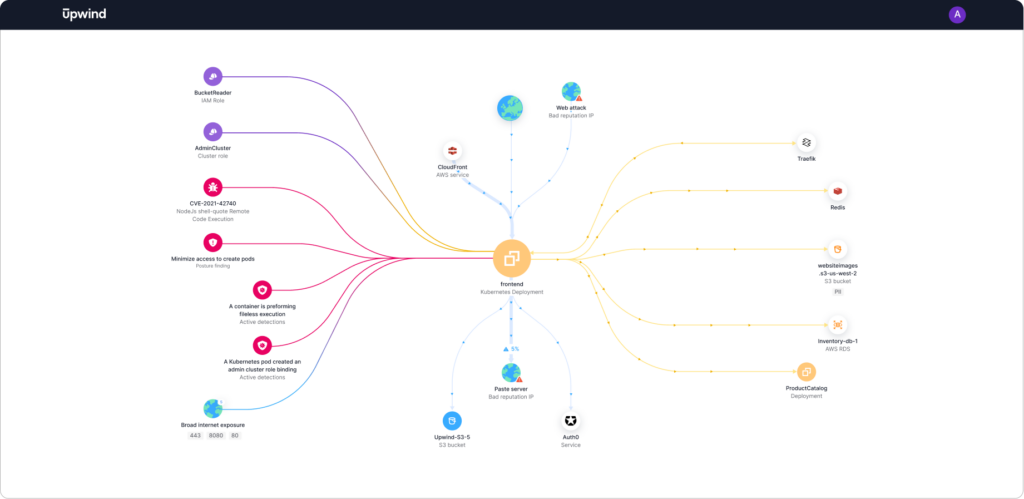
Upwind’s Deep Investigation
Upwind’s eBPF-agent also allows you to conduct thorough investigations of detections and receive all of the needed context to understand which threats are actually critical to your environment. Upwind’s root cause analysis allows you to immediately go to the root cause of risks and threats, down to the developer that introduced a vulnerability that was exploited by a threat. You can also see and understand everything that happens in your cloud environment, down to every network call, which you can see on Upwind’s topology map and examine which services are talking to each other and drill down to a process tree level and examine root cause.
This deep context and runtime insights allow security professionals to stop wasting time & resources on triaging applications behavior and go directly to the root cause of threats. While it would have previously taken hours or days to understand the root cause of threats or attempted breaches, Upwind’s Threat Detection allows you to do the same remediations within minutes, saving your security team vital time and money.
Upwind’s Immediate Response to Threats
Upwind’s eBPF-agent not only provides you with runtime insights, it also allows you to immediately respond to threats by blocking specific network traffic or intercepting system calls. With Upwind’s Threat Detection, you can respond immediately to threats by killing a process, quarantining a workload or container from traffic or creating a policy that prevents future malicious executions. This allows you to not only stop current threats, but to automate responses to them in the future and even prevent them entirely in the future with custom prevention policies.
In short, Upwind’s Threat Detection allows security teams to perform advanced threat hunting with complete cloud visibility, rapidly identify and respond to threats in real-time and get to the root cause of threats 10x faster.
Learn More
To learn more about Upwind’s Intelligent Threat Detection and Response capabilities, refer to the Upwind Documentation Center (login needed).
To see a live demo of Upwind in action, please email us at [email protected].
Up & Upwind! 🏄♂️