Deep Dive: CVE-2024-37902 and Potential Impact on DeepJavaLibrary Users
AWS announced today, June 17, that there is a potential security issue with archive extraction utilities in DeepJavaLibrary versions 0.1.0 through 0.27.0 that could allow an attacker to tamper with your system.
What is DeepJavaLibrary?
DJL is a free, open-source library by AWS used for building deep learning models in Java. It provides easy-to-use tools for training, testing, and deploying your models. This project enjoys strong community support with over 4,000 stars and hundreds of forks on GitHub.
Understanding CVE-2024-37902
DJL versions prior to 0.28.0 are susceptible to a vulnerability concerning absolute paths within archived artifacts (compressed files like ZIP or JAR). An absolute path specifies the complete location of a file on a system. When processing these archived files, DJL might attempt to extract them based on the absolute paths contained within the archive. If these paths target system files, the extraction process could overwrite critical system files, potentially compromising system stability.
Deep dive into the code
The problem resides inside the file api/src/main/java/ai/djl/util/TarUtils.java
Copied
While it checks if the file name contains “..” thus preventing a file by the name of ../../../bin/echo from replacing system files, it does not check for files starting with “/” such as /bin/echo that will overwrite system files
The latest DJL versions fix the vulnerability by removing leading separators from filenames during archive extraction, preventing absolute path exploitation:
Copied
Which versions are affected?
- DJL versions 0.1.0 through 0.27.0 are affected by this vulnerability.
How do you fix affected versions of DJL?
If you are using an affected version of DJL, it is recommended that you upgrade to version 0.28.0 or higher. Upgrading will ensure that you are protected from this vulnerability.
How Upwind protects against critical CVEs
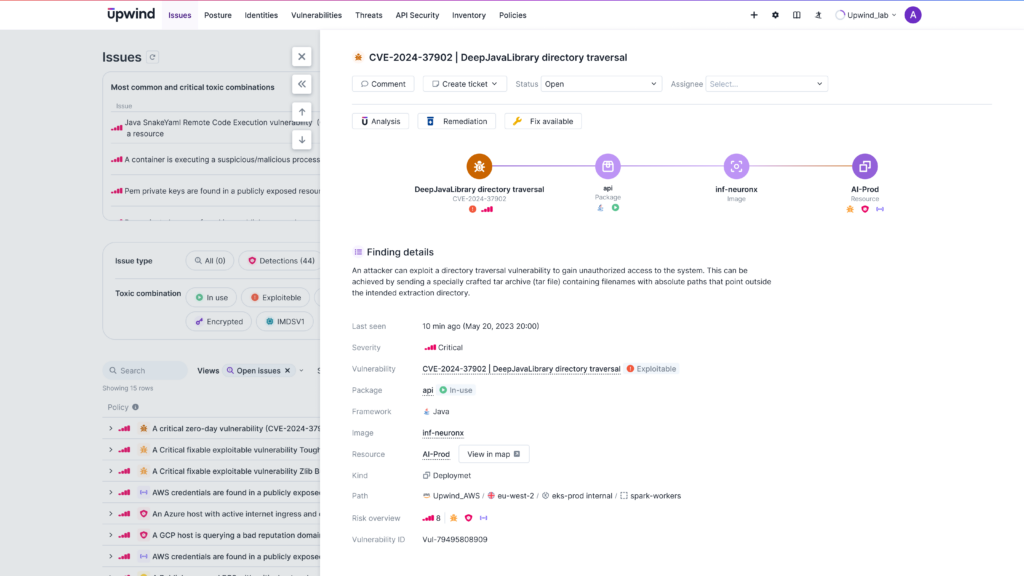
The Upwind Cloud Security Platform offers several solutions to CVE-2024-37902 and other critical vulnerabilities by providing the following:
- Vulnerability management: Upwind’s vulnerability management helps you reduce noise and prioritize critical vulnerabilities. View the immediate impact vulnerabilities have on your environment including package dependencies, all affected resources, and available fixes.
- Threat detection: Upwind’s threat detection system proactively identifies and alerts you to anomalous activity within your environment, helping you go beyond malware signature recognition to identify advanced threats.
- Critical Issues Prioritization: Upwind Issues intelligently identifies open attack paths and “toxic combinations” of threats, vulnerabilities and posture issues, helping you to efficiently address your most relevant security concerns.
Learn More
Want to learn more about how Upwind protects you against critical vulnerabilities? Visit the Upwind Documentation Center (login required) or schedule a demo.







