Achieve Deeper Runtime Threat Investigation with Upwind Detection Logs
Imagine a threat appears, vanishes, and then reappears two days later – same process, slightly different path. Without the right visibility, you’d treat it like a new incident each time. But with Upwind Detection Logs, you get the historical context to see the full picture. Upwind provides deep runtime visibility and security across all environments, […]
Streamline Cloud Threat Detection and Response with Upwind’s Major Threats Module Enhancements
Cloud security teams are drowning in alerts, struggling to prioritize real threats among endless notifications. To help security professionals cut through the noise, we are thrilled to announce major enhancements to our Threats Module, further empowering security professionals to understand deep context for every threat detection, identify emerging threat actors, and respond to threats faster. […]
Introducing New Runtime Security Features for Modern Containerized Environments

At Upwind Security, we continuously enhance our security capabilities to address emerging threats and provide unparalleled runtime protection for containerized environments. In this update, we are excited to introduce new detection and prevention policies designed to secure workloads against sophisticated attacks. Next-Generation Threat Detections Over the past several weeks we have added additional detection policies […]
Detect & Respond to Advanced Cloud Threats with Upwind
Upwind’s next-generation cloud security platform not only provides real-time risk analysis and threat detection, it also gives you the ability to respond to threats in real time. In this article, we will dive deep into how Upwind detects threats in real time, our advanced methods of activity-based threat detection, and ways you can stop or […]
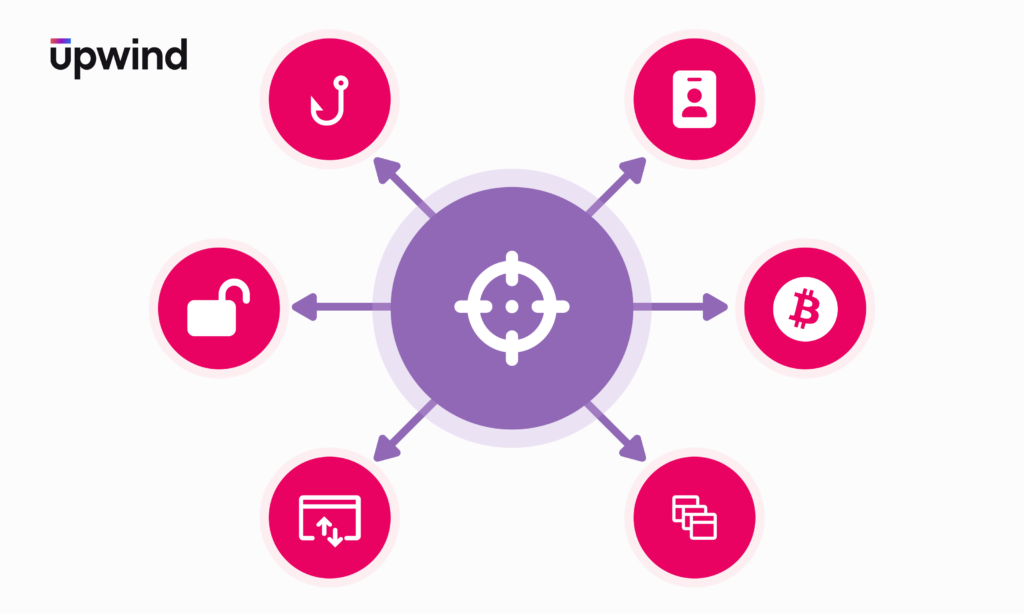
Cloud Heist: How Hackers Lock Accounts and Drain Wallets

Cloud environments have changed how organizations manage their infrastructure, offering flexibility and scalability. But these benefits also bring new risks, and even small mistakes in cloud security can have serious consequences. For example, Google Cloud once accidentally deleted data from a $125 billion Australian pension fund due to a simple configuration error. Although this wasn’t […]
How Adversaries Use Telegram to Evade Detection

In recent years, there has been a significant increase in adversaries exploiting popular messaging apps such as Telegram, Discord, Signal, and others to conceal their malicious activities. Among these platforms, Telegram stands out due to its robust security features, including end-to-end encryption and anonymous account creation, making it a go-to tool for cybercriminals. Overview Most […]
Understanding File-Based Attacks
File-based attacks are a growing concern in cybersecurity. These attacks involve tampering with files to gain unauthorized access, steal information, or cover up malicious activities. In this post, we’ll break down what file-based attacks are, look at some real-world examples, and walk through a typical attack scenario. What Are File-Based Attacks? File-based attacks exploit how […]
Enhance Your Threat Detection Capabilities with Custom Policy Scope

We are excited to announce a significant new capability, giving you the ability to customize threat detection policy scope in the Upwind platform. Upwind has always provided powerful out-of-the-box threat detection policies based on predefined attack vectors, ensuring real-time threat detection. With this new capability, Upwind provides even more customization to fit your unique infrastructure […]
How Organizations Use Upwind’s File-Based Threat Monitoring
Upwind’s threat detection capabilities give you real-time protection against cloud attacks, including malicious file activities. Upwind’s lightweight, high-performance eBPF sensor goes beyond monitoring file activities to enrich that data with information about an event’s context and provide insights into the actions taken on the file, including read, write, and truncate (delete). You can leverage this […]
Power Your Cloud Security with Software Development Lifecycle (SDLC) Context

We are excited to introduce a new capability that enables you to bring-your-own version control system to the Upwind platform – which integrates rich context from pull requests and build-time activities directly into our cloud infrastructure security platform. Upwind offers unprecedented end-to-end visibility of your cloud infrastructure and applications, marrying intelligence from both build time and […]