From “Encrypt Everything” to “Encrypt for the Quantum Era”: The Upwind Cloud Cryptography Framework
For most of the last decade, cloud security teams have lived by a simple slogan: encrypt everything. Encrypt at rest. Encrypt in transit. Use customer-managed keys. Rotate them. Pass the audit. Move on. That slogan just expired. In August 2024, NIST finalized the first three post-quantum cryptography (PQC) standards and explicitly told organizations: start using […]

Miasma: A Worming npm Supply Chain Attack on Red Hat Cloud Services
Executive Summary On June 1, 2026, unauthorized commits were pushed to repositories in the RedHatInsights GitHub organization and used to publish malicious versions of 32 packages under the @redhat-cloud-services npm scope. The campaign, tracked as Miasma, executes a 4.2 MB obfuscated payload through an npm preinstall hook the moment any of these packages is installed, […]
Security for AI: Every Pillar of Cloud Security Just Got a New Job
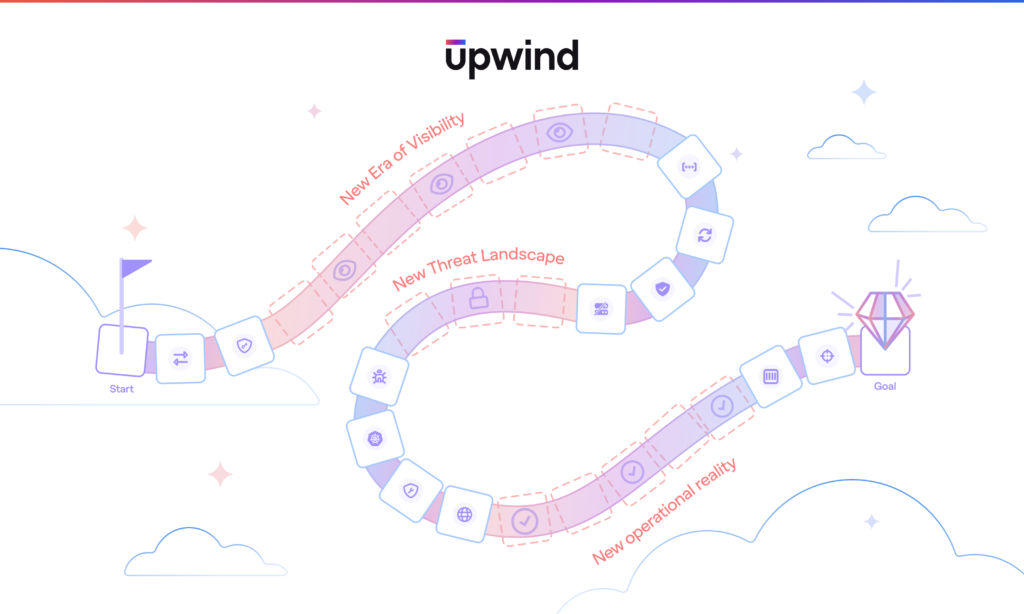
A few weeks ago, I wrote about Upwind becoming agentic, AI for Security. We put a fleet of Agents, Blue, Red, and Green, to work investigating threats, validating exposures, and remediating risk at machine speed. That was one half of the story. This is the other half. Security for AI. AI has rewired our known […]
No Way Out? Bypassing the AWS Data Perimeter with Bedrock AgentCore
A novel Command-and-Control (C2) channel weaponizes legitimate AWS services to establish two data channels, successfully circumventing one of the cloud’s strongest security defenses. Status: Infiltration Channel is FIXED, Exfiltration Channel is OPEN. TL;DR This research was presented at fwd:cloudsec North America 2026. Watch the full talk below. What Is the AWS Data Perimeter? For the […]

Upwind Brings Realtime Intelligence to Cisco Cloud Control
We are thrilled to announce that Upwind has been selected as a launch partner for Cloud Control Studio, part of Cisco Cloud Control, bringing realtime intelligence on cloud and AI security into the platform. Unveiled at Cisco Live Las Vegas on June 2, 2026, Cisco Cloud Control is the unified platform for agentic IT operations. […]

Thanks to GlassWorm, your developer’s laptop is now the most dangerous device in your company. You’re Welcome.
Key Takeaways We’ve spent the last decade hardening the perimeter. Using firewalls, Zero Trust and EDR on every endpoint. SOC analysts surviving on cold brew and adrenaline just to keep us safe. And then GlassWorm walked straight through the front door. Like taking candy from a baby. If you haven’t been following this one, here’s […]

We Compiled the Top 10 MCP Use Cases for Upwind
A new vulnerability enters the backlog. A workload is exposed. A misconfiguration affects production. An identity behaves unexpectedly. A customer asks for evidence. An audit or pentest is coming up. Each moment requires the same understanding of what is real, what is urgent, what is connected, and what should happen next. The Upwind MCP Server […]
Upwind Researcher Spotlight: Dan Gansel
“You have to map the core logic and syntax of the system before you can find the interesting primitives.” This June 1st, Dan Gansel will walk on stage at fwd:cloudsec 2026 in North America to demonstrate a fully functional command-and-control channel that operates inside the AWS Data Perimeter, the cloud-native gold standard for keeping sensitive […]
Scale AI Adoption Securely With Upwind AI Security
AI is entering production faster than many security teams can keep up. As teams embed AI into applications, developer workflows, and cloud operations, security teams need to know where AI runs, what it can access, and which risks need action. Upwind AI Security connects AI usage to realtime cloud context, giving teams a practical way […]

Refuse the Seat: Why Modern CISO Leadership Advice Is Failing the Profession
Key Takeaways The single most repeated piece of advice in security leadership is also the one doing the most damage to the profession. Earn your seat at the table. Become a business translator. Integrate into the operator class. The CISOs who follow that advice end up burned out, legally exposed, and stuck in five-jobs-in-one roles […]













