
regreSSHion: RCE in OpenSSH’s Server on glibc-based Linux Systems (CVE-2024-6387)
OpenSSH is widely known for managing secure shell connections (SSH). However, a recently discovered vulnerability in OpenSSH’s server (sshd), known as regreSSHion, has been identified. If a client does not authenticate within the LoginGraceTime (120 seconds by default, 600 seconds in older versions), sshd’s SIGALRM handler is called asynchronously. This signal handler calls functions that are not safe to use in such contexts (like syslog()). This issue affects sshd in its default configuration.
This vulnerability is a regression of CVE-2006-5051, reported by Mark Dowd in 2006, and reintroduced in October 2020 with OpenSSH 8.5p1.
Affected OpenSSH Versions
- OpenSSH versions earlier than 4.4p1: Vulnerable unless patched for
CVE-2006-5051andCVE-2008-4109. - Versions from 4.4p1 up to, but not including, 8.5p1: Not vulnerable due to a patch for
CVE-2006-5051. - Versions from 8.5p1 up to, but not including, 9.8p1: Vulnerable again due to the accidental removal of a critical safety component.
This vulnerability is exploitable remotely on glibc-based Linux systems. The syslog() function in these environments calls functions like malloc() and free(), which are not safe to use in a signal handler. This can lead to remote code execution as root since sshd runs with full privileges. OpenBSD is not affected by this vulnerability because it uses a safer version of syslog() that does not have this issue.
To exploit this vulnerability remotely, techniques from Michal Zalewski’s paper “Delivering Signals for Fun and Profit” (2001) were utilized.
Exploitation Scenarios
Various OpenSSH versions on i386 were targeted to understand the vulnerability better:
- SSH-2.0-OpenSSH_3.4p1 Debian 1:3.4p1-1.woody.3 (Debian 3.0r6, 2005)
- Approach: Interrupting a call to
free()withSIGALRMduring public-key parsing. - Outcome: This leads to remote root access after approximately 10,000 attempts, which is about one week with default settings.
- Approach: Interrupting a call to
- SSH-2.0-OpenSSH_4.2p1 Debian-7ubuntu3 (Ubuntu 6.06.1, 2006)
- Approach: Interrupting
pam_start()withSIGALRM. - Outcome: A similar issue results in remote root access after about 10,000 attempts, roughly one to two days with default settings.
- Approach: Interrupting
- SSH-2.0-OpenSSH_9.2p1 Debian-2+deb12u2 (Debian 12.5.0, 2024)
- Approach: Interrupting
malloc()withSIGALRMduring public-key parsing. - Outcome: Remote root access is achieved after about 10,000 attempts, which takes approximately three to four hours with 100 connections per 120 seconds.
- Approach: Interrupting
Research is ongoing, and efforts are being made to develop a more robust exploit for modern systems with stronger security features.
Patches and Mitigation
On June 6, 2024, this issue was fixed by commit 81c1099. The commit moved the unsafe code out of the SIGALRM handler to a safer context, effectively addressing the vulnerability:
- Commit Reference: Commit 81c1099
Mitigation
If backporting this commit is difficult, the issue can be mitigated by removing the unsafe code from sshsigdie(). This approach reduces the risk of exploitation by ensuring that potentially vulnerable code is not executed in an unsafe context.
for example:
Copied
If updating or recompiling sshd is not feasible, setting LoginGraceTime to 0 in the configuration file will prevent the race condition but may lead to denial of service (exhaustion of MaxStartups connections).
How Upwind Protects You from regreSSHion CVE-2024-6387
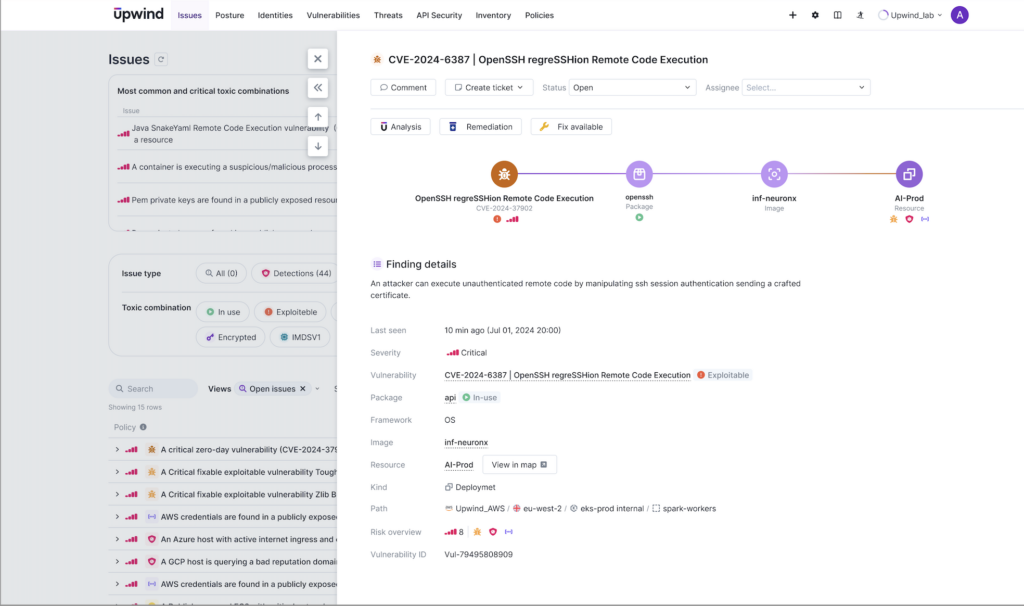
The Upwind Cloud Security Platform offers several solutions to OpenSSH vulnerabilities and other critical vulnerabilities by providing the following:
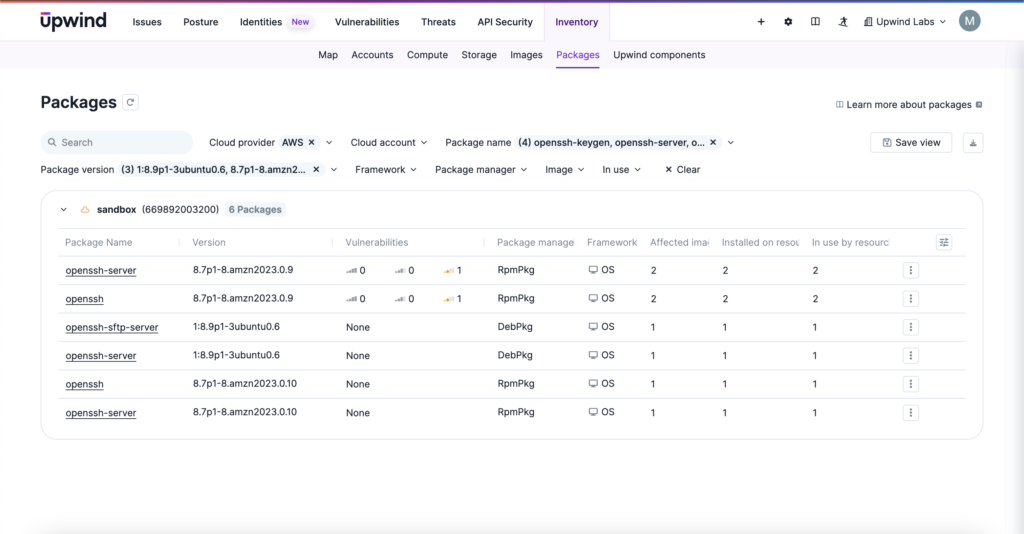
- Find Vulnerable Packages with Upwind’s SBOM Explorer: Search for and easily display all packages impacted by
CVE-2024-6387, including OpenSSH versions earlier than 4.4p1 and versions from 8.5p1 up to, but not including, 9.8p1. - View Scope of Resources: Find all resources that contain
CVE-2024-6387, which cloud accounts they are in, and which clusters, pods, namespaces, VMs and resources they are using. View the impactCVE-2024-6387has on resources in your environment including package dependencies available fixes. - Understand Risk Context: View the criticality of risk that
CVE-2024-6387poses in your environment, including toxic combinations of resources impacted by the CVE that also have internet exposure, are talking to a database, contain secrets, contain sensitive data and more. - Prioritize Package Upgrades: Create a list of vulnerable resources that should be prioritized for updates, using the recommended fixes listed in this article to quickly secure your environment.
Get Further Help from Upwind MDR
Upwind’s expert security team also provides 24/7 managed detection and response services, giving you real-time support for CVE-2024-6387 and all zero days or critical vulnerability findings. For additional help finding vulnerable packages, identifying the scope of resource usage with the CVE, understanding their risk context and prioritizing package upgrades contact the Upwind MDR team at [email protected] or schedule a demo.






