What is eBPF?
Observe every workload directly from the kernel, giving you real-time insight into processes, network flows, and file activity without performance impact.
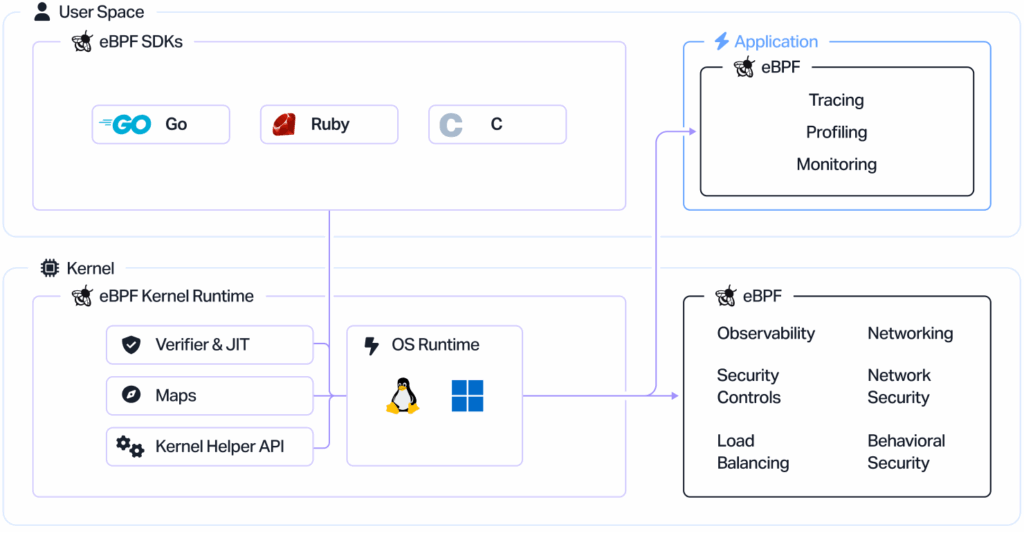
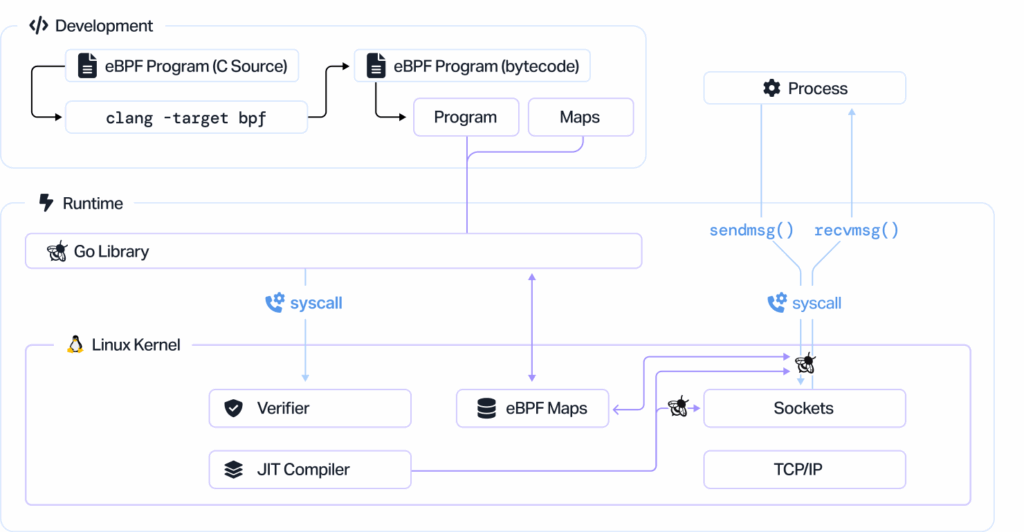
Dynamically program the kernel for efficient networking, observability, tracing, and security
What’s possible with eBPF?
Networking
Accelerate packet processing while remaining in kernel space. Extend functionality with custom protocol parsers and easily define forwarding logic to meet evolving performance and compliance needs.

Observability
Collect and aggregate in-kernel metrics with the flexibility to generate visibility events and data structures from a wide range of sources, without exporting samples or adding overhead.
Tracing & Profiling
Attach eBPF programs to trace points across kernel and user applications, gaining deep visibility into probe points and performance data. This enables powerful introspection and faster root-cause analysis of system behavior.

Security
Combine real-time visibility into system calls with a full packet- and socket-level view of network activity. Build security systems that operate with richer context and deliver stronger detection and response capabilities.
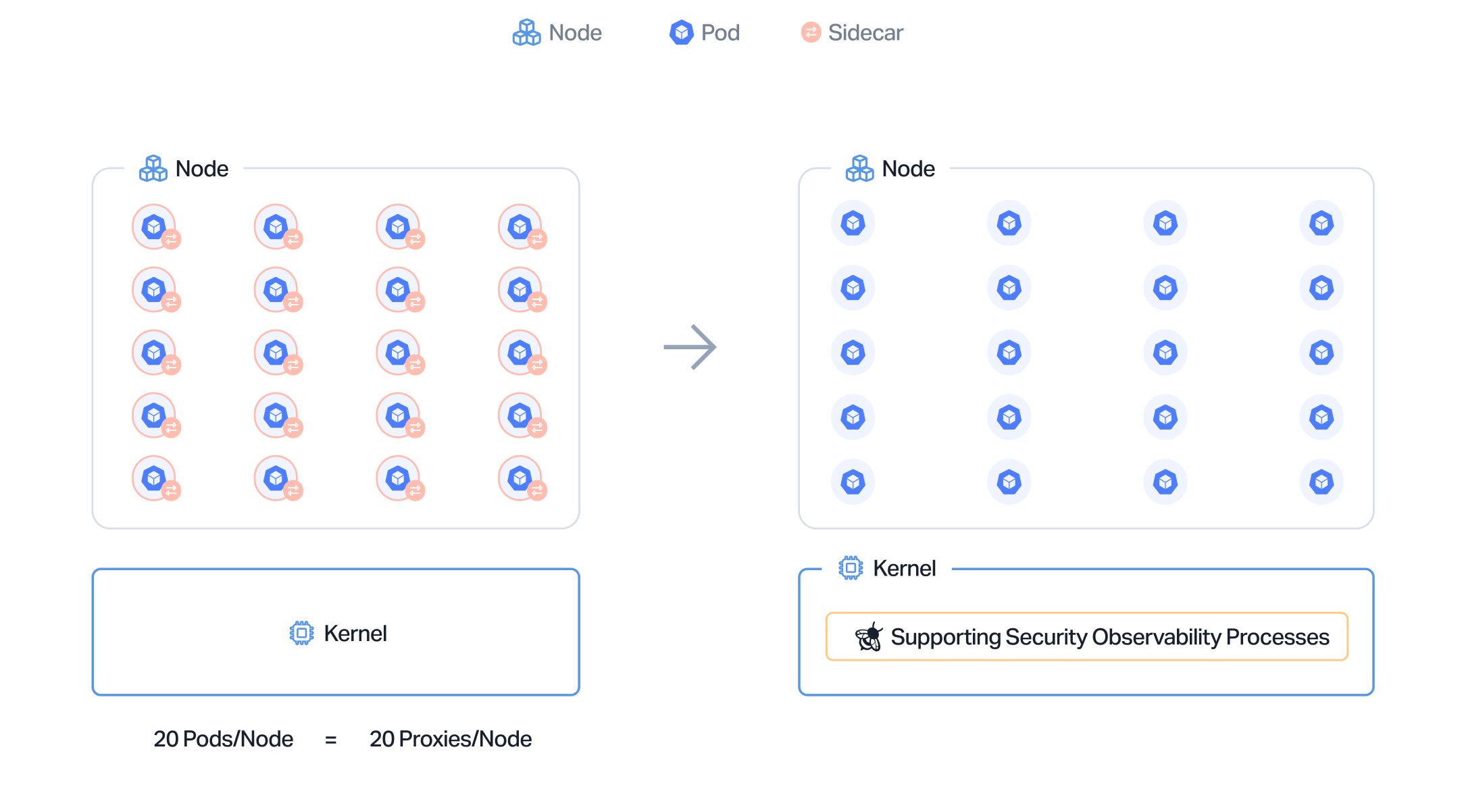
eBPF vs sidecar model
Upwind leverages eBPF to safely attach to any running workload across containers, hosts, and serverless environments without code changes or downtime. This deep, non-invasive visibility allows us to trace behavior, detect anomalies, and correlate runtime events to real risks.
The future of real-time monitoring
Upwind continuously verifies kernel-level telemetry collected through eBPF to ensure accuracy, integrity, and safety. Every process, connection, and syscall is validated in real time, providing trusted visibility into workloads without intrusive agents or code modification.
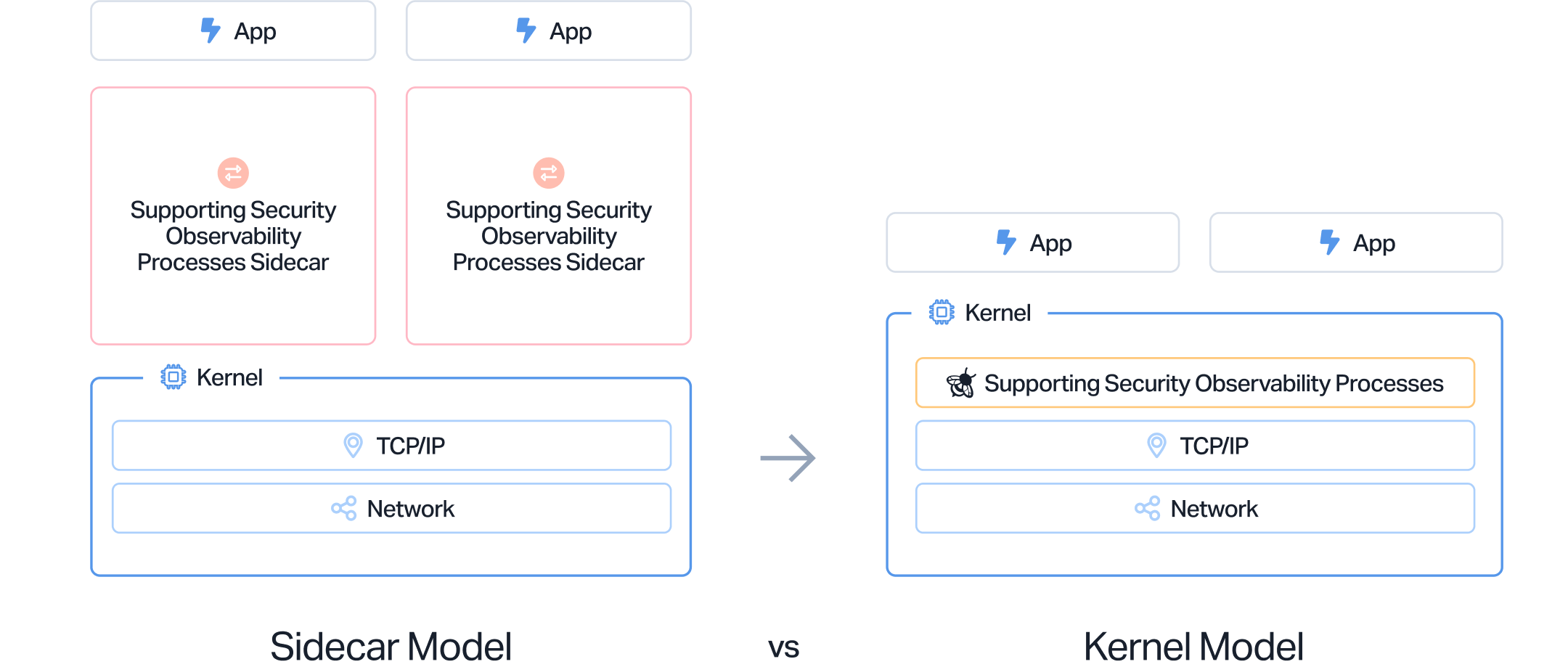
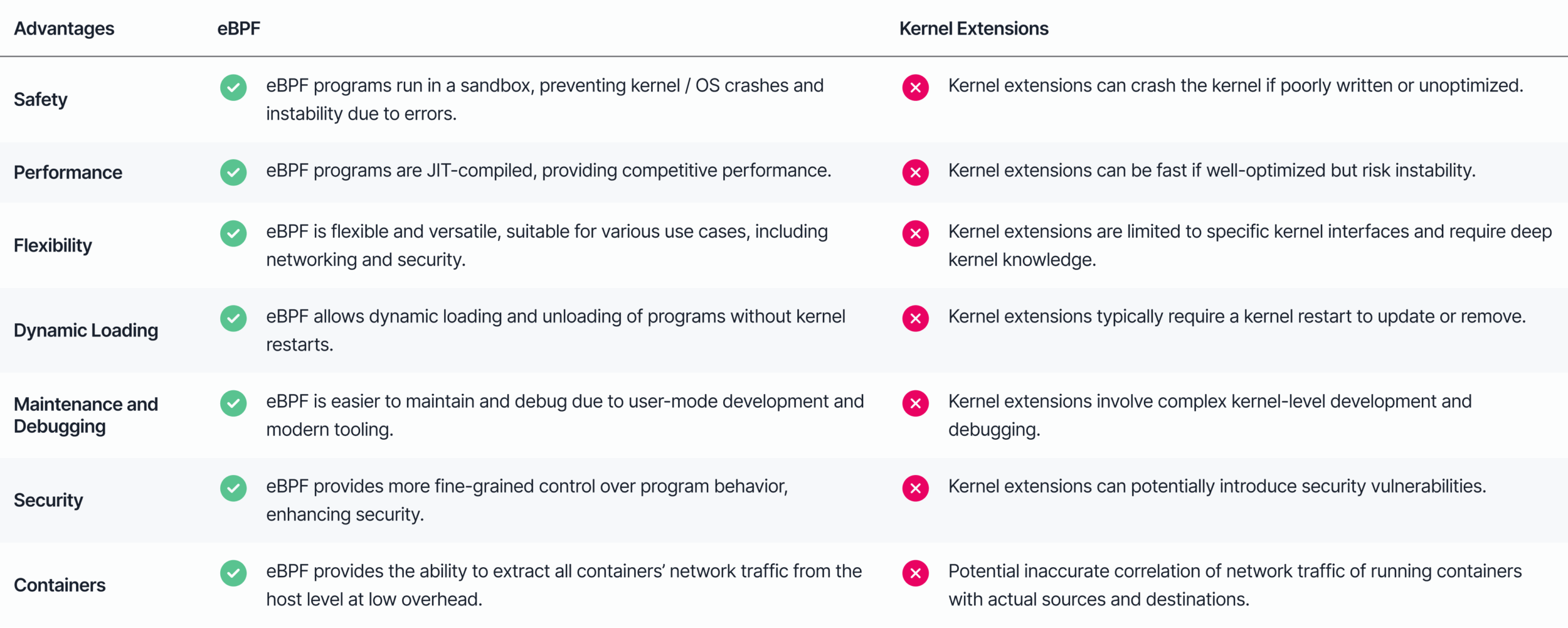
Unlock the kernel without extensions
Upwind uses eBPF to extend your observability and security stack directly into the operating system. From workload inventory to network flow mapping and file monitoring, Upwind turns low-level kernel data into actionable insights that power runtime-aware posture, detection, and compliance.