Know What You Have. Protect What Matters.
Trusted by hundreds of enterprises around the world
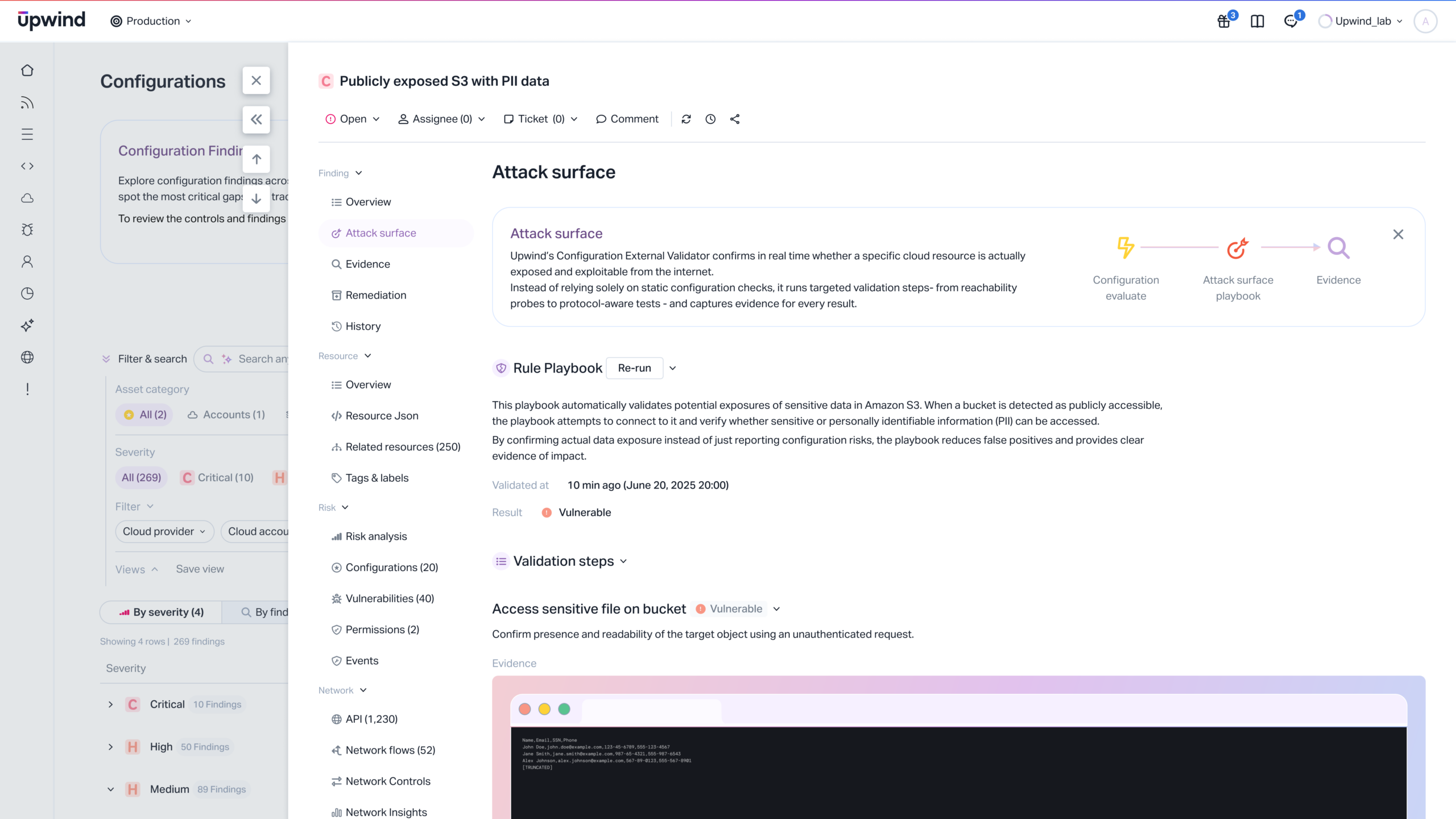
Best-in-Class Attack Surface Reduction



Discover Every Asset Across Your Cloud Estate
- Uncover shadow and unmanaged resources
Reveal forgotten, orphaned, or unexpected deployments.
- Full inventory across all environments
See every workload, function, API, identity, and endpoint in one place.
- Real-time awareness as environments shift
Stay ahead of exposure created by rapid development changes.
Identify What’s Publicly Exposed
- Detect internet-facing workloads automatically
Know exactly what attackers can reach today.
- Spot high-impact misconfigurations
Catch unintended exposure from open network routes or shared resources.
- Understand true perimeter risk
Tie external exposure to live services and sensitive data.
Prioritize by Real Exploitability
- Cut noise from theoretical findings
Filter using runtime reachability, privilege, and identity paths.
- See blast radius before attackers do
Understand what’s at stake if an asset is compromised.
- Fix what reduces risk fastest
Direct teams toward high-impact changes backed by evidence.
Track Ownership for Faster Resolution
- Align assets to responsible teams
Eliminate “who owns this?” delays during remediation.
- Speed operational workflow
Route issues directly into the tools developers use.
- Drive accountability on critical exposures
Prioritize the issues that matter most to the business.
Maintain a Continuous Security Baseline
- Measure posture improvements over time
Know whether exposure is trending downward.
- Prevent exposure re-introductions
Policies ensure risky patterns don’t reappear.
- Always audit-ready
Maintain visibility aligned with compliance requirements.
Eliminate Exposure Before Attackers Can Exploit It