Expose How Attackers Can Actually Break In
Trusted by hundreds of enterprises around the world
Eliminate real exploitable risk



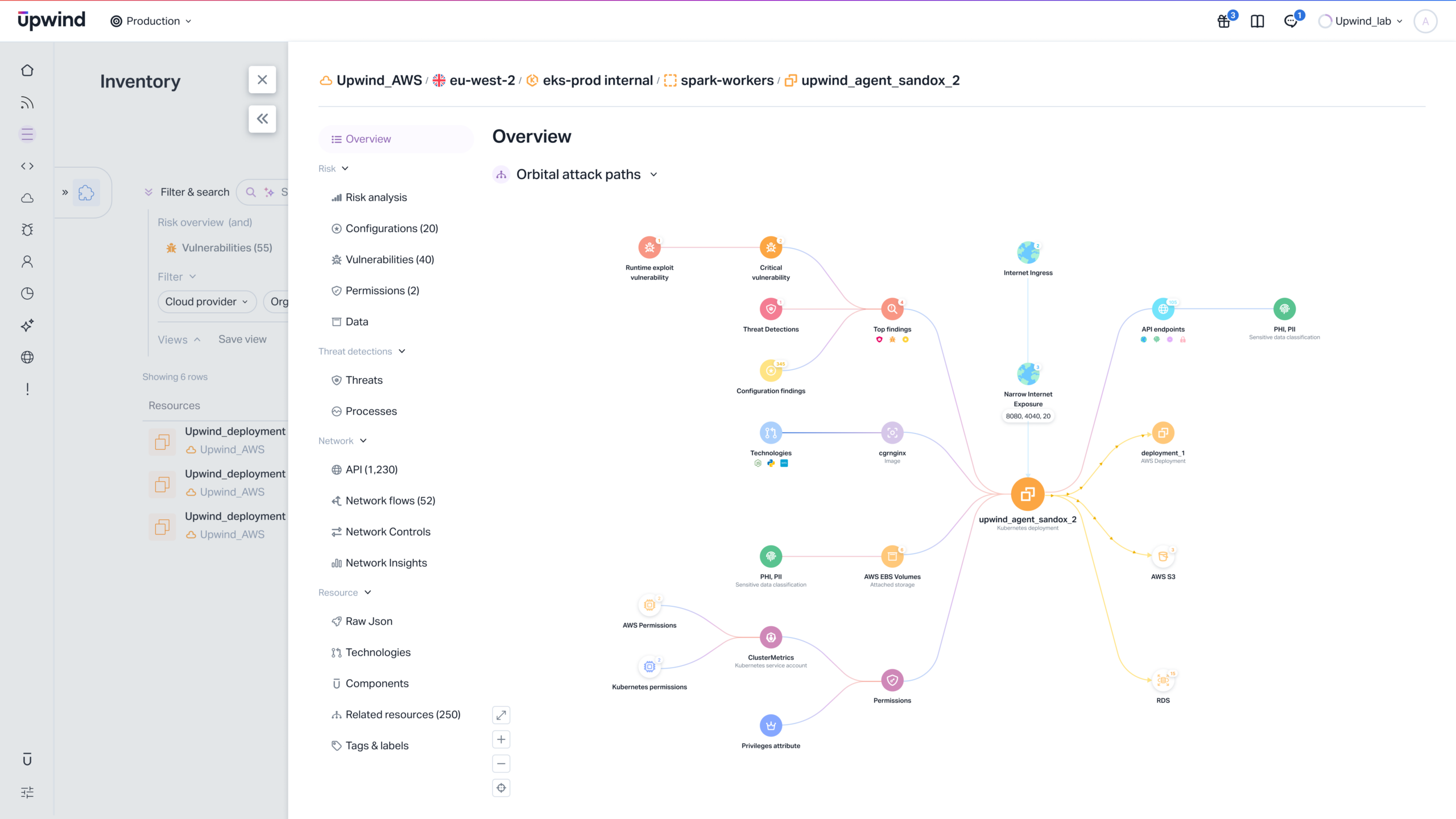
Visualize Real Attack Paths
- See how threats propagate
Map lateral movement across services, identities, APIs, and data.
- Reveal critical choke points
Identify resources whose compromise leads to major impact.
- Clarify attack graph complexity
Filter paths to only what matters.
Prioritize Based on Blast Radius
- Reduce noise with context
Focus on vulnerabilities tied to reachable, high-value assets.
- Understand damage potential
Evaluate risk based on what attackers can truly access.
- Accelerate risk decisions
Provide executives with business-level exposure clarity.
Analyze Identity-Based Attack Chains
- Map permission escalation paths
Show how compromised users could gain dangerous access.
- Uncover hidden privilege routes
Trace indirect and inherited access across clouds.
- Eliminate over-permissioned identities
Shrink attacker movement options before they’re abused.
Validate Exploitability in Runtime
- Filter out non-threats
Confirm whether services and dependencies are actually reachable.
- Align SecOps with engineering
Teams focus together on risks proven dangerous in production.
- Strengthen remediation impact
Close the pathways — not just the symptoms.
Accelerate Investigation & Containment
- Full attack context in minutes
Immediately see where attackers entered and where they’re headed.
- Isolate risky relationships
Break the chain to stop spread and protect key assets.
- Respond confidently
Eliminate threats backed by evidence, not assumptions.
See the Attack Path Before the Attacker Does