Secure Serverless Workloads at Runtime
Trusted by hundreds of enterprises around the world
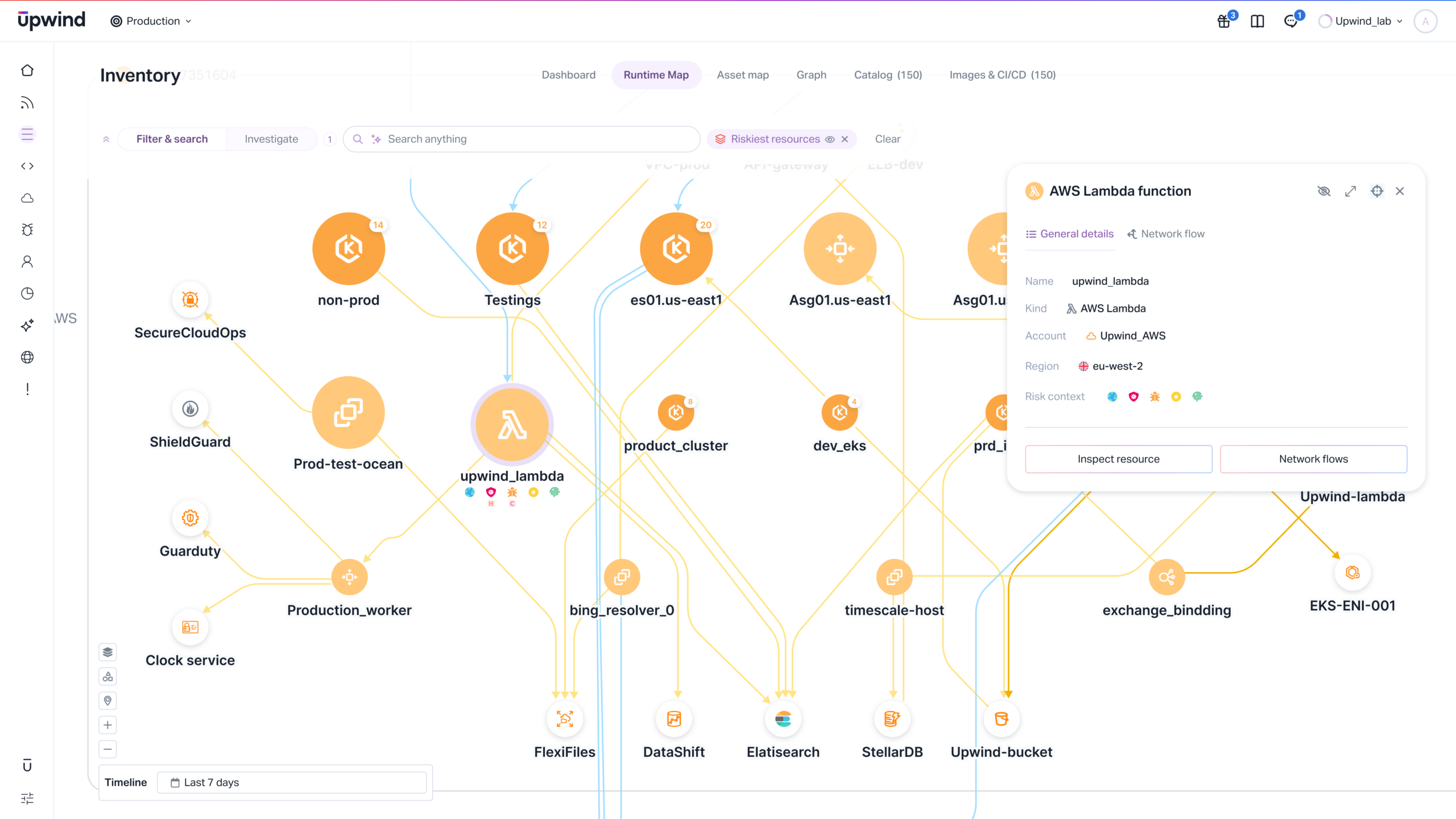
Comprehensive Visibility & Protection for Severless Workloads



Discover and Monitor Every Serverless Function
- Complete multi-cloud inventory
Automatically track every function across AWS, Azure, and Google Cloud so nothing is overlooked.
- Full dependency & connection visibility
Understand exactly what each function touches and how it behaves.
- Expose hidden risk
Surface blind spots and unauthorized activity with continuous monitoring.
Block Vulnerabilities, Malware & Secrets Exposure
- Identify risky packages at deployment
Detect vulnerable libraries, outdated components, and malicious artifact behavior.
- Stop secret leakage
Catch embedded keys and tokens before they ship.
- Prevent bad code from executing
Enforce guardrails that block exploitable functions pre-runtime.
Reduce Serverless Attack Surface
- Shut down over-permissioned functions
Remove excessive IAM privileges tied to real behavior.
- Fix misconfigured triggers fast
Prioritize exposure tied to reachable event paths.
- Cut risk without downtime
Protect functions while keeping applications running normally.
Prove Serverless Compliance with Runtime Evidence
- Map compliance controls to real activity
Validate SOC 2, ISO, and CIS benchmarks against live execution.
- Generate audit-ready reporting
Replace sampling and guesswork with continuous verification.
- Maintain compliance without the burden
Automate monitoring to reduce operational overhead.
Detect and Respond to Runtime Threats
- Spot suspicious behavior instantly
Detect anomalies like privilege escalation and unexpected data access.
- Automated threat containment
Terminate malicious processes and block propagation in real time.
- Accelerate investigations with context
Threat timelines show exactly what happened and what was impacted.
Continuous Serverless Protection