The Evolution of EDR and CWPP
As the technological landscape continues to innovate and scale cloud operations, cyber security techniques are rapidly evolving to keep pace with the expanding threat landscape and increasingly innovative bad actors.
Cybersecurity incidents, including ransomware attacks, phishing attempts and data breaches have become more frequent and sophisticated. According to the 2022 Cost of a Data Breach Report by IBM, the average cost of a global data breach was $4.35 million, an increase from $4.24 million in 2021. Costs of data breaches in the U.S. are even more expensive – averaging $9.44 million, over $5 million more than the global average.
As organizations move from on-premises to hybrid-cloud or cloud-native models of operation, attack surfaces are only continuing to grow. Gartner predicts that cloud spending will be 14.2 percent of total global enterprise IT spending in 2024. Statistica reports that regardless of industry, half of enterprises had workloads running in the public cloud in 2023, and 48 percent of those workloads included data.
However, with increasing cloud presence also comes increased risk – IBM reports that over 45 percent of data breaches happen in the cloud. According to the 2020 Cloud Security Report by Cybersecurity Insiders, misconfiguration of cloud platforms was identified as the leading cause of data breaches in the cloud.
IBM reports that over 45% of data breaches happen in the cloud
As attack landscapes continue to evolve, security professionals must also remain agile in their infrastructure defense, making use of more traditional solutions such as EDR, while also employing cloud solutions like CWPP to increase their cloud infrastructure security.
What is EDR?
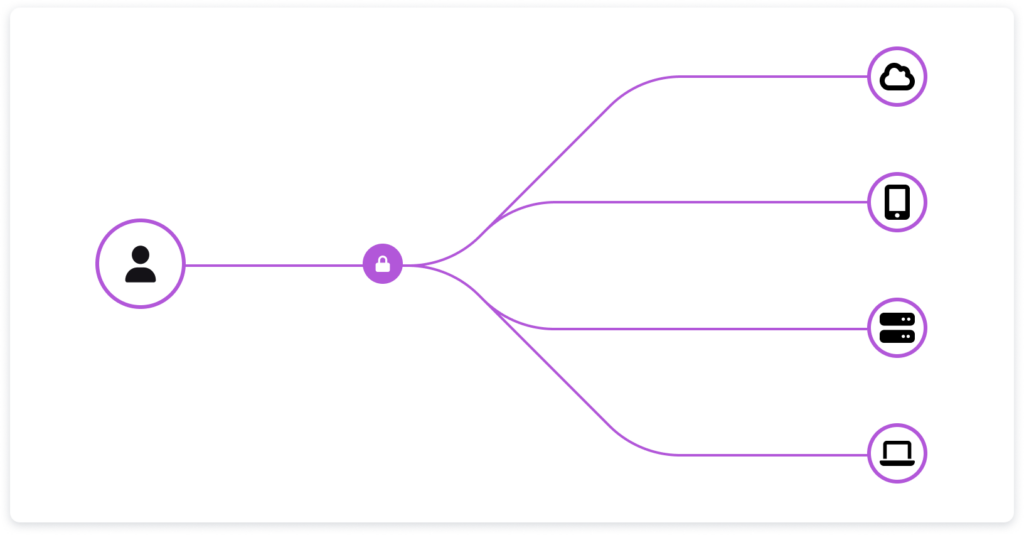
Endpoint Detection and Response (EDR) solutions are one of the main strategies employed to detect and respond to advanced threats targeting endpoints, such as desktops, laptops, servers, and mobile devices. EDR is the continuous monitoring of endpoints, including threat detection and vulnerability detection for endpoints.
As technology and cyber attacks have become increasingly complex, EDR systems also have evolved, moving from traditional antivirus software and perimeter defenses to behavioral analysis and machine learning. EDR solutions are generally used to prevent malware or other threats from targeting endpoints.
EDR solutions provide real-time, continuous visibility into endpoint activities, giving security teams the ability to detect and automate responses to threats. EDR techniques now take into account threat intelligence and data analytics to identify malicious behaviors and allow teams to respond quickly to incidents.
However, while EDR solutions help secure on-premises infrastructure, many organizations require further protection as they move into hybrid-cloud or cloud-native environments. This new frontier of cybersecurity has led to the emergence of Cloud Workload Protection Platforms (CWPP).
The Birth of CWPP
Cloud adoption has grown significantly in the past 10 years, and with that there is a growing need for solutions that protect cloud infrastructure. One of the most prominent categories of infrastructure security is CWPP solutions focused on protecting workloads running in the cloud, including serverless functions, containers and virtual machines. Overall, CWPP solutions provide better cloud visibility, as well as vulnerability management, risk detection and compliance monitoring.
A CWPP helps organizations understand workload vulnerabilities and prioritize those that pose the most significant risk to their environment. Just as EDR solutions help stop threat actors at endpoints, CWPP solutions help organizations stop bad actors from exploiting vulnerabilities in their cloud infrastructure and workloads.
So what exactly is a CWPP?
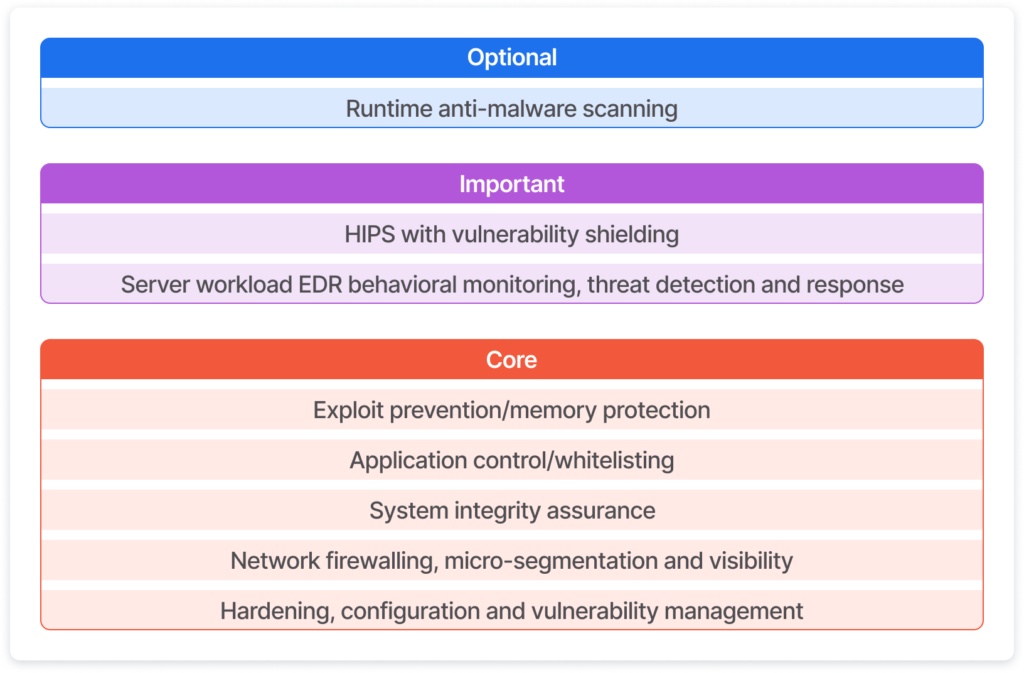
Gartner defines CWPP as workload-centric security protection solutions, which provide eight layers of protection for cloud workloads including: vulnerability management, scanning for vulnerabilities prior to production, network firewalling, system integrity protection, application control, behavioral monitoring, intrusion prevention and runtime anti-malware protection.
What is CWPP in Practice?
In other words, it can be difficult for organizations to have complete visibility and understanding of their infrastructure when it’s spread across a variety of servers, platforms and machines. CWPP solutions break down those visibility barriers and give a complete view of running workloads, helping companies get a full-picture view of a their security situation.
CWPP solutions give organizations a number of advantages in protecting their running workloads. Some of the most important CWPP functions include:
- Visibility: CWPP provides increased visibility of multi-cloud and multi-architecture environments, enabling teams to view all of their infrastructure in one place.
- Flexibility to Scale: One of the main benefits of cloud infrastructure is the ability to remain agile and scale up or down with business needs. CWPP allows application security to also be flexible and scale capacity up or down.
- Threat Detection: CWPPs help security teams identify threats in their cloud environment, including malware, executable files, running processes and even fileless (in-memory) malicious code.
- Vulnerabilities Management: CWPPs allow security teams to identify vulnerabilities and get to the root cause at a much faster rate, automating responses and saving countless hours of security tasks.
EDR, CWPP and CDR
While CWPP gives security teams increased visibility and protection for their cloud infrastructure, they often fail to provide the ability to detect and respond to threats and vulnerabilities in real time.
Many CWPP solutions use side-scanning methods, which show security teams risk and threat detections, but miss a critical piece – runtime insights. Without a real-time understanding of cloud environments, it puts security teams at a disadvantage when protecting against increasingly sophisticated threat actors, which can cause significant damage in a short amount of time. This is in sharp contrast to the speed at which EDR operates, which is real-time detection and response for endpoints.

With the increasing speed of threat actors, the need has emerged for real-time cloud detection and response, also known as CDR. Cloud detection and response solutions effectively work in a similar way to an anti-virus for the cloud, at a much larger scale than EDR.
In the EDR landscape, organizations work with a static amount of endpoints and are able to adjust their protection strategies accordingly. However, cloud infrastructure is dynamic and operates on a far grander scale, meaning CDR solutions have to provide real-time detection and response for an ever-changing landscape with equally dynamic threat actors.
CDR is effectively taking the visibility provided by CWPP solutions, and giving it an added twist – runtime capabilities that allow organizations to monitor their cloud environments at any given moment and keep up with the increasing speed of attackers.
This need for runtime detection and response capabilities is set to only grow as organizations increasingly operate in hybrid-cloud or cloud-native environments. Cloud-native security requires the fundamental tenets of EDR such as real-time monitoring, vulnerabilities management and automated threat detection and response, but with an evolved security strategy for the cloud. As CWPP continues its evolution with CDR to provide these real-time capabilities, the push for solutions that leverage runtime data and context will only continue to grow.