Organizations often require greater security and control than public cloud providers can offer — especially when handling highly sensitive data or operating in heavily regulated industries. In such cases, private clouds provide an ideal solution, offering superior control, customization, and enhanced security by eliminating the shared infrastructure of public clouds.
However, this increased level of security and control comes with its own set of challenges and considerations from a security standpoint — from data protection to network segmentation and compliance, maintenance, integration with legacy systems, and with public cloud providers in a hybrid architecture — new complexities creep in.
A well-designed private cloud security strategy addresses these concerns so that workloads remain protected from cyber threats while maintaining performance and operational efficiency. What does it look like?
We’re exploring key aspects of private cloud security: best practices, essential security controls, and the role of automation and compliance in maintaining a secure cloud environment.
Understanding Modern Private Cloud Security
A private cloud consists of a highly customizable and secure cloud environment tailored to meet the specific needs of an organization. Private cloud security refers to the protection of enterprise applications, data, and infrastructure within that private cloud environment. Key components include:
- Access Control: Enforcing strict authentication and authorization policies so only authorized users and devices access critical resources.
- Data Encryption: Encrypting data both at rest and in transit to protect sensitive information from unauthorized access.
- Network Security: Implementing firewalls, segmentation, and VPNs to secure communication within the private cloud.
- Compliance and Governance: Adhering to regulatory standards like GDPR or HIPAA to meet industry-specific security requirements.
- Monitoring and Incident Response: Continuously monitoring the cloud environment for suspicious activity and having a strong incident response plan in place.
Private cloud security implementations help enterprises maintain control over their sensitive data and workloads with the benefits that come with cloud computing, like scalability.
The TL;DR on CNAPP
Want the actual TL;DR on CNAPP (hint – it starts with runtime security)? Don’t spend days reading someone’s PhD dissertation – check out our comprehensive 8 step CNAPP guide.
Get the E-BookKey Components in Private Cloud Security
Unlike public cloud environments, where security responsibilities are shared with the cloud provider, private clouds give enterprises full control over their infrastructure, leading to greater responsibility for security considerations. Consequently, a pantheon of tools and frameworks dominate discussions of securing the private cloud, addressing everything from access control to continuous monitoring, vulnerability management, and compliance. These tools not only help secure workloads but also ensure proper configuration, prevent misconfigurations, and enforce policies that align with an organization’s security and compliance needs.
Key tools and principles for private cloud security include:
- Cloud-Native Application Protection Platforms (CNAPPs): CNAPPs provide visibility and security across the entire cloud-native stack, including hybrid and on-prem workloads, ensuring secure deployment and operation across environments.
- Software-Defined Perimeters (SDP): SDP dynamically conceals network and cloud infrastructure by making applications and services invisible until authentication is successfully completed. It ultimately helps enterprises gain granular control over who accesses what, ensuring that only authorized users and devices can access specific applications, especially for remote workforces or distributed applications.
- Zero Trust Principles: Zero Trust practices enforce continuous verification of users, devices, and access rights, assuming no one is trusted by default, whether inside or outside the network.
- Identity and Access Management (IAM): IAM policies control who can access resources in the cloud and what they can do with them. As private cloud environments grow, maintaining strong identity verification and least privilege access balance the increased complexity of user roles, access points, and privileged access.
- Encryption: Data encryption at rest and in transit need encryption no matter where workloads run so that if data is intercepted, it can’t be accessed.
- Cloud Security Posture Management (CSPM): CSPM tools help enterprises continuously monitor and enforce security best practices and compliance requirements across private cloud resources, helping prevent misconfigurations and data breaches.
- Automated Security: As private cloud environments scale, automated security tools (including CI/CD security and vulnerability management) help make sure security is baked into the development and deployment pipelines.
Pros and Cons of Private Cloud Deployments
While private clouds may seem like an obvious choice for enhanced security and value, they aren’t ideal for every organization. Benefits like greater control, security, and customization come with trade-offs: higher upfront costs, operational complexity, and the need for specialized expertise to maintain and scale effectively.
Private clouds are popular, but so are public cloud platforms. In fact, 76% of enterprises use private clouds for at least some workloads, but just 3% rely on private cloud providers exclusively.
Organizations handling sensitive data may prefer the access control and customization they get with private cloud providers, but the discrepancy in private vs. public cloud use shows there’s still a place for a hybrid architecture among savvy organizations: there’s no perfect place for all workloads.
Advantages of Private Clouds
- Granular Control Over Security: Adjust security settings, access rules, and data protection exactly how your organization needs them.
- Simplified Compliance: Built to meet strict regulations (like HIPAA, GDPR, SOC 2), making it easier to prove compliance during audits.
- Reduced Risk of External Breaches: No shared resources with other organizations, lowering the chance of breaches common in public clouds.
- Customizable Security Tools: Add specialized protections like private firewalls, breach detection systems, or unique encryption methods.
- Reliable Performance for Security Systems: Security tools run smoothly without slowdowns since resources aren’t shared with others.
Disadvantages of Private Clouds
- Substantial Infrastructure Costs: Requires heavy investment in hardware, security tools, and specialized IT talent.
- Scalability Constraints: Less flexible than public clouds in terms of scaling.
- Operational Complexity: Demands continuous monitoring, updates, and management by expert staff.
- Insider Risk Exposure: Centralized control heightens vulnerability to privileged-user errors or malicious actions.
- Disaster Recovery Gaps: Limited built-in redundancy and resilience (compared to public clouds).
Hybrid vs Public Cloud vs Private Cloud Security
Key Differences in Security Models
Cloud security differs considerably across hybrid, public, and private cloud environments, particularly in control, risk exposure, and compliance. However, cloud-native application protection with AI is becoming a standard across all cloud security models. IDC predicts that by 2025, 23% of organizations will adopt AI-powered CNAPPs to maintain continuous compliance through cloud security posture management.
The following are the key security distinctions between the different cloud deployment models.
Public Cloud Security
Public cloud security relies on shared infrastructure managed by third-party cloud providers, where security responsibilities are divided under the shared responsibility model—that is, providers secure the cloud infrastructure, while customers must secure their data and applications.
While public clouds may offer advanced security features like DDoS protection and AI-driven threat detection and response, they also increase exposure to external threats due to multiple organizations sharing the same infrastructure. This multi-tenancy also exposes users to the noisy neighbor effect, where a tenant’s performance is degraded due to another tenant’s activities (e.g., one tenant consumes excessive resources, resulting in slower processing times for others). Additionally, public cloud providers implement standardized security policies that may not fully align with a specific industry’s compliance requirements.
Private Cloud Security
Private cloud security gives organizations full control over security policies, configurations, and infrastructure. This control is crucial for firms operating in industries/sectors with strict regulatory requirements and compliance mandates (e.g., healthcare, finance, government), as private clouds allow for bespoke configurations that meet the criteria of industry oversight bodies. Since private clouds operate on dedicated resources, the cyber risks associated with multi-tenancy and external breaches are effectively reduced or eliminated.
However, this expansive control comes at the cost of higher complexity and resource demands. Organizations must fully manage security operations, including firewall configurations, intrusion detection, encryption, and compliance audits. And unlike public clouds, private clouds require dedicated IT teams to handle functions like security updates, patch management, and incident response, to name a few.
Hybrid Cloud Security
Hybrid clouds offer greater flexibility and security customization capabilities by blending aspects of public and private cloud environments. Organizations can host sensitive workloads on a private cloud for enhanced security while leveraging the scalability and cost efficiency of public clouds for less critical applications (i.e., cloud bursting).
However, hybrid cloud security introduces its own unique challenges such as difficulties in securing data transfers between private and public environments, ensuring consistent IAM, and monitoring security threats across multiple platforms. Strong encryption, secure APIs, and unified security policies are important here for mitigating risks. Hybrid clouds also demand more advanced security architectures to maintain consistent protection across interconnected cloud infrastructures and environments.
Different security concerns emerge with each, making no single platform ideal for every use case — or even for an ideal security posture. In fact, security factors and other tech and business concerns shift in each environment. Here’s how:
| Factor | Public Cloud | Private Cloud | Hybrid Cloud |
| Control | Limited/ provider-managed | Full | Balanced with flexibility between public and private environments |
| Data Security | Data stored in shared environments, increased exposure risk | Data stored in a dedicated environment, reduced exposure risk | Sensitive data can be kept private while utilizing public cloud for less critical workloads |
| Compliance | Depends on provider | Easier to meet strict regulatory requirements | Can be custom tailored to meet specific compliance requirements |
| Threat Exposure | Higher risk due to multi-tenancy | Lower risk, private infrastructure | Exposure risk mitigated by keeping critical assets in private cloud |
| Customization | Limited | Highly customizable | Customizable based on workload needs |
| Cost | Low upfront costs | High upfront costs | Depends on workloads |
| Access | Provider managed, IAM | Full control | Flexible |
Choosing the Right Model for Your Organization
So how can teams choose? Ultimately, the decision comes down to individual workloads and their needs, an organization’s specific security needs, regulatory requirements, scalability, and cost considerations.
Private clouds offer greater control over security and infrastructure and may be the most appropriate deployment model if your organization handles highly sensitive data or requires adherence to strict compliance controls.
On the other hand, a hybrid cloud can provide the benefits of both the public and private cloud for organizations looking to strike a balance between cost and flexibility. A hybrid cloud deployment allows sensitive workloads to remain on-premises while leveraging the scalability of public cloud services for less critical tasks.
Alternatively, if cost-efficiency and scalability are the top priorities, the public cloud may be an ideal deployment model, as it allows pay-as-you-go services without the need for managing physical infrastructure. Ultimately, the right cloud deployment model should align with your organization’s specific operational goals, IT capabilities, and long-term strategic plans.
Secondary Considerations in the Hybrid Cloud
Many teams adopt a private cloud for sensitive workloads, aiming to realize the best of both worlds when it comes to cloud convenience and security. However, in coordinating their cloud resources, deeper, tech-specific challenges emerge.
First, there’s integration. Can private cloud resources integrate with the public cloud? Latency and compatibility issues may make the relationship challenging. Cloud-native tools that allow for real-time data flow, without gaps, are key to reducing the friction between clouds when it comes to security.
Perimeter security is another issue. The border between public and private clouds requires updated security tools where perimeter monitoring may no longer handle the demands of the dynamic environment. Zero Trust policies can take the place of firewall access, but teams must consider how they’ll enforce network segmentation in a hybrid environment, without impacting performance.
Consider data sovereignty. Sensitive workloads might be stored in the private cloud without an understanding of the requirements for data residency. Teams can deploy automated solutions to help sort it out. Automation itself can be an issue, as it’s a challenge to optimize solutions across environments.
Identity and Access Management can further bog down security teams, as their existing tools may not be able to manage the increasing complexity that comes with multiple clouds. Are granular access controls enforcing consistent rules across environments? Can they?
Finally, teams will be tasked with gaps in their disaster recovery strategies. Private clouds need to be able to deliver redundancy and resiliency in case of a breach. Can the cloud architecture recover without relying on public cloud failover?
Ultimately, adopting a private cloud means adding to the components of what’s likely already a complex cloud architecture, where security, compliance, and efficiency are all challenged.
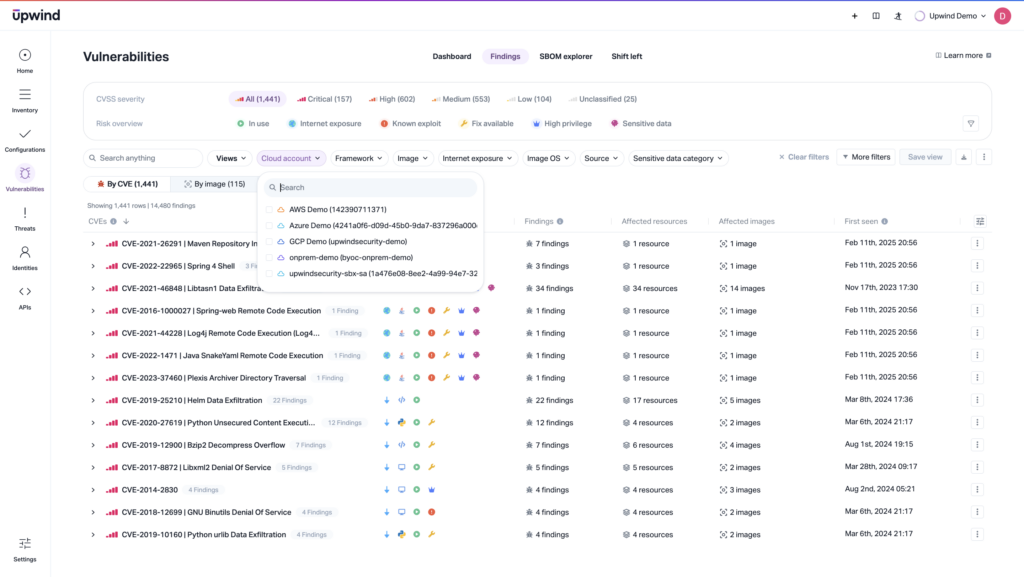
Upwind Secures Private and Hybrid Clouds
Visibility and consistent enforcement across clouds are where successful private and multi-cloud security start. No matter where your workloads run, Upwind is part of a layered security strategy for securing your environment. Upwind’s CNAPP enables thorough private cloud security management through comprehensive monitoring and automated security validation. By providing integrated vulnerability scanning, runtime protection, and compliance monitoring capabilities in a unified solution, Upwind helps organizations maintain robust security postures while eliminating the complexity of managing multiple disparate tools.
To see how it works, schedule a demo.
Frequently Asked Questions
How do you ensure data privacy in private clouds?
Ensuring data security and privacy in private clouds requires a multi-layered approach that involves implementing strong encryption, access controls, and continuous monitoring to protect sensitive data. Key practices include:
- Data Encryption: Encrypting data both at rest and in transit to prevent unauthorized access.
- Access Controls: Implementing strict role-based access control (RBAC) and least privilege access policies.
- Data Masking and Anonymization: Using techniques to anonymize or mask sensitive data when it’s not needed for processing.
- Compliance: Making sure the private cloud environment adheres to relevant regulations like GDPR, HIPAA, and SOC 2.
- Continuous Monitoring: Monitoring data access and activity to detect potential breaches or anomalies.
Since organizations have full control over their private cloud infrastructures, the onus is on them to implement strict security policies for safeguarding sensitive information from unauthorized access and breaches.
What are the essential security controls for private clouds?
Strong private cloud security requires a combination of technical, administrative, and physical controls to protect sensitive data, applications, and infrastructure. These include:
- Identity and Access Management (IAM) and multi-factor authentication (MFA) to ensure that only authorized users have access to cloud resources,
- Strong authentication mechanisms like RBAC to limit user permissions based on job responsibilities.
- Network security controls for stringent segmentation and traffic monitoring to prevent lateral movement in the event of a breach.
- Dynamic firewalls, Intrusion Detection Systems or Intrusion Prevention Systems (IDS/IPS), and CNAPP for secure communication between cloud resources and applications.
- Micro-segmentation tools at the network level for isolating workloads, making it more difficult for attackers to access critical systems even if a breach occurs, and regular network security audits to maintain a hardened private cloud environment over time.
- Data protection and encryption to secure sensitive information stored and processed within a private cloud.
- Regular data backups, disaster recovery planning, and data loss prevention (DLP) solutions to ensure that data remains protected and recoverable in case of system failures or compromises.
- Continuous monitoring and compliance enforcement to maintain a secure private cloud environment, including vulnerability assessments to detect and mitigate security risks proactively.
By implementing these essential security controls, organizations can build a resilient private cloud that protects their critical assets while meeting regulatory and business requirements.
How do you maintain compliance in private cloud environments?
Maintaining compliance in private cloud environments requires a structured approach to security, governance, and risk management. Organizations should first identify relevant regulatory frameworks that apply to their industry and geographic location. Once compliance requirements are established, organizations should design and implement policies to meet them. Cover the following areas:
- Data protection
- Access control
- Incident response
- Audit readiness.
Since private clouds provide greater control over infrastructure, organizations are responsible for ensuring that their security configurations align with compliance mandates — which differ by industry, geography, and voluntary certification standards.
What are the best practices for private cloud access control?
Strong access controls in private cloud environments incorporate:
- Commit to the Principle of Least Privilege so users have only the access and permissions necessary to perform their job functions—no more, no less. This can be achieved through RBAC, which assigns access rights based on users’ roles and responsibilities, ensuring individuals only have the permissions required for their specific tasks. By limiting access to sensitive resources, businesses can significantly reduce the risk of data breaches and insider threats. Regular access reviews are also essential to identify and remove unnecessary privileges, preventing the accumulation of excessive permissions over time.
- Use strong authentication mechanisms like MFA and IAM to streamline user authentication across cloud resources, ensuring consistency in access control policies. Security teams should also enforce strong password policies, including complexity requirements, expiration policies, and account lockout mechanisms to prevent credential-based attacks.
- Employ continuous monitoring and auditing to maintain a secure access control strategy. Organizations should log all authentication attempts, permission changes, and access to critical resources using tools like Security Information and Event Management (SIEM) for analysis. Restricting privileged account usage and requiring approval-based workflows for administrative access can help prevent misuse or unauthorized changes.
- Use network segmentation and automation to strengthen private cloud access control. Employ Zero Trust security principles and require continuous verification for every access request rather than assuming trust based on network location. Network segmentation further isolates workloads, limiting an attacker’s ability to move laterally within the cloud. Automating access reviews and deprovisioning processes ensures that former employees or contractors do not retain access to private cloud resources.
By following these best practices, organizations can enforce a strong access control strategy that protects private cloud infrastructure and critical data. And while it seems that teams may need to juggle multiple tools to maintain a strong cloud security posture, it doesn’t have to be that way. Solutions like Upwind help organizations maintain robust security postures while eliminating the complexity of managing multiple disparate tools.